Email Security that Evolves with Modern Threats
0 分鐘閱讀

Kevin Oliveira
In a previous post I discussed how email represents the weakest data security vector for organizations. Email volume over the past several years has increased exponentially. Unfortunately, so has data loss through email. In this context, it's not surprising that email remains one of the most popular ways for bad actors to deliver malware and phishing attacks.
According to Jennifer Glenn, research director for IDC's Information and Data Security products:
"Email and collaboration tools are often the gateway to an organization's most sensitive assets..."
"Security tools aimed at enforcing protection and educating users at this pivotal egress point are essential for secure and trusted digital transformation."
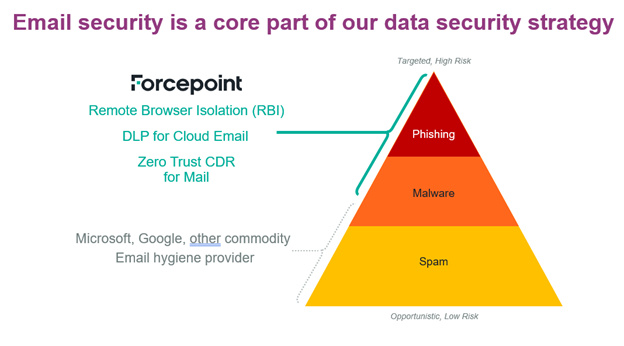
While there have been some important improvements in the email data security market in the last couple of years, one major change is that basic email hygiene that addresses incoming email spam and many types of malware has become ubiquitous. Many of our customers are using Microsoft 365 or Gmail. And both vendors' capabilities to cover spam and malware have improved. We call this “commodity email hygiene” – it’s widely available and very often our customers already have this through their email services.
But as we all know, hackers never sit still. Phishing attacks are more sophisticated; and more complicated malware attacks continue to increase while they become more targeted, requiring stronger security capabilities. Forcepoint is addressing these changes in the following ways:
- We are continuing to provide email security solutions through Forcepoint DLP for Cloud Email, Email Security Gateway (on-prem), and Forcepoint ONE which includes DLP protection for email. As stated, email is a serious security threat vector for data exfiltration. The ability to effectively prevent data loss through multiple channels is key to protecting an organization’s sensitive information. Forcepoint has been recognized as a leader in Data Security Platforms by providing a multi-pronged approach to data security which prevents data exfiltration with powerful data security including the email channel.
- Forcepoint also provides zero trust email security capabilities through two key technologies. The first is Remote Browser Isolation (RBI) – a powerful tool that prevents malware and phishing threats by rending risky sites in a remote virtual container ensuring malicious code does not infect the endpoint. RBI prevents contact between the device and any malware running on a website, completely stopping malware and phishing attacks in email.
The second zero trust product is Zero Trust Content Disarm and Reconstruction (CDR) which sanitizes documents at download and prevents steganographic uploads. Steganography is a technique of hiding secret data within an ordinary, non-secret file or message to avoid detection. CDR literally rebuilds images bit by bit taking out all extraneous information, again effectively preventing malware and phishing attacks. Forcepoint both offers Zero Trust CDR through Forcepoint ONE or through Zero Trust CDR for Mail: M365. Also read this whitepaper on how you can enhance your email security with Zero Trust CDR.
The increased sophistication in phishing and malware attacks along with the changes in the commodity email data hygiene market is changing the way email security is best done. We’ll continue our commitment to making email more secure, and to reducing the risk of sensitive data loss while streamlining the entire process for our customers.
For more information on how Forcepoint can help you with your email data security needs see this website or schedule a demo with one of our email experts.

Kevin Oliveira
閱讀更多文章 Kevin OliveiraKevin serves as Senior Product Marketing Manager for Forcepoint’s Data Security products and solutions. He has over 20 years experience helping enterprises with their data and security initiatives with leadership positions at Dell EMC and IBM.
- Prevent Data Theft with DLP for EmailLearn How
X-Labs
直接將洞察力、分析與新聞發送到您的收件箱










