Forcepoint DSPM: At A Glance
Data Security Posture Management (DSPM) solutions help organizations tame explosive data sprawl and the risks that accompany it. Forcepoint DSPM puts accuracy above all else with its unique approach to data discovery, classification and tagging – its AI Mesh classification architecture. Deployable on-premises and in public or private clouds, and part of a unified data security platform, Forcepoint DSPM closes the gap between visibility and control of your data – whether that data is structured or unstructured, in the cloud or on-premises.
Consistently Identify Sensitive Data Everywhere
Powered by Forcepoint’s proprietary AI Mesh, Forcepoint DSPM automates data discovery and sensitive data classification while enabling remediations for sensitive data risks across the enterprise. Eliminate blind spots with comprehensive visibility from on-prem servers to cloud services, across structured and unstructured data.

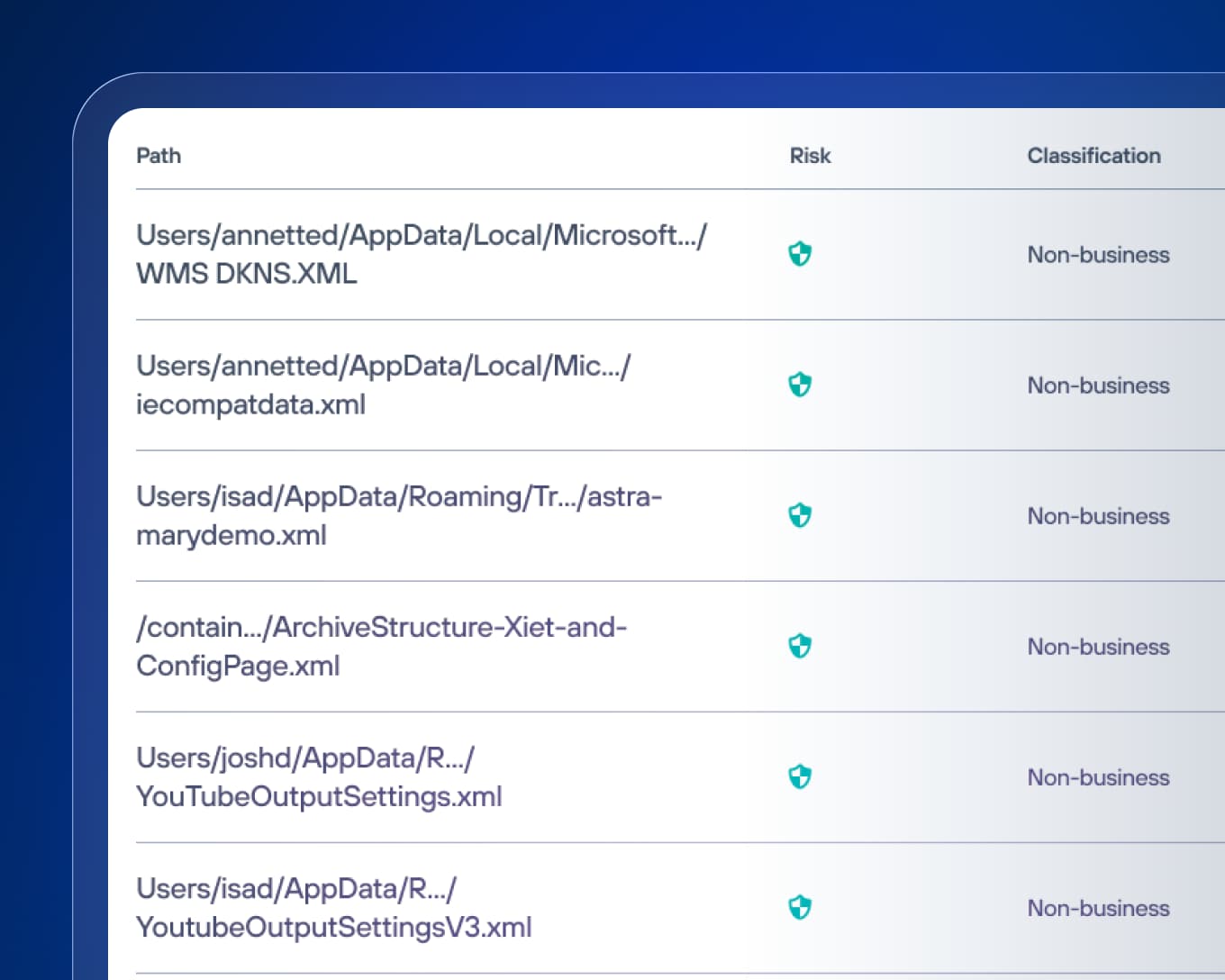
Proactively Reduce Risk
Identify sensitive data that is shared too broadly and adjust permissions or move files from risky locations while leaving a file stub to maintain workflows.

Automate Data Hygiene
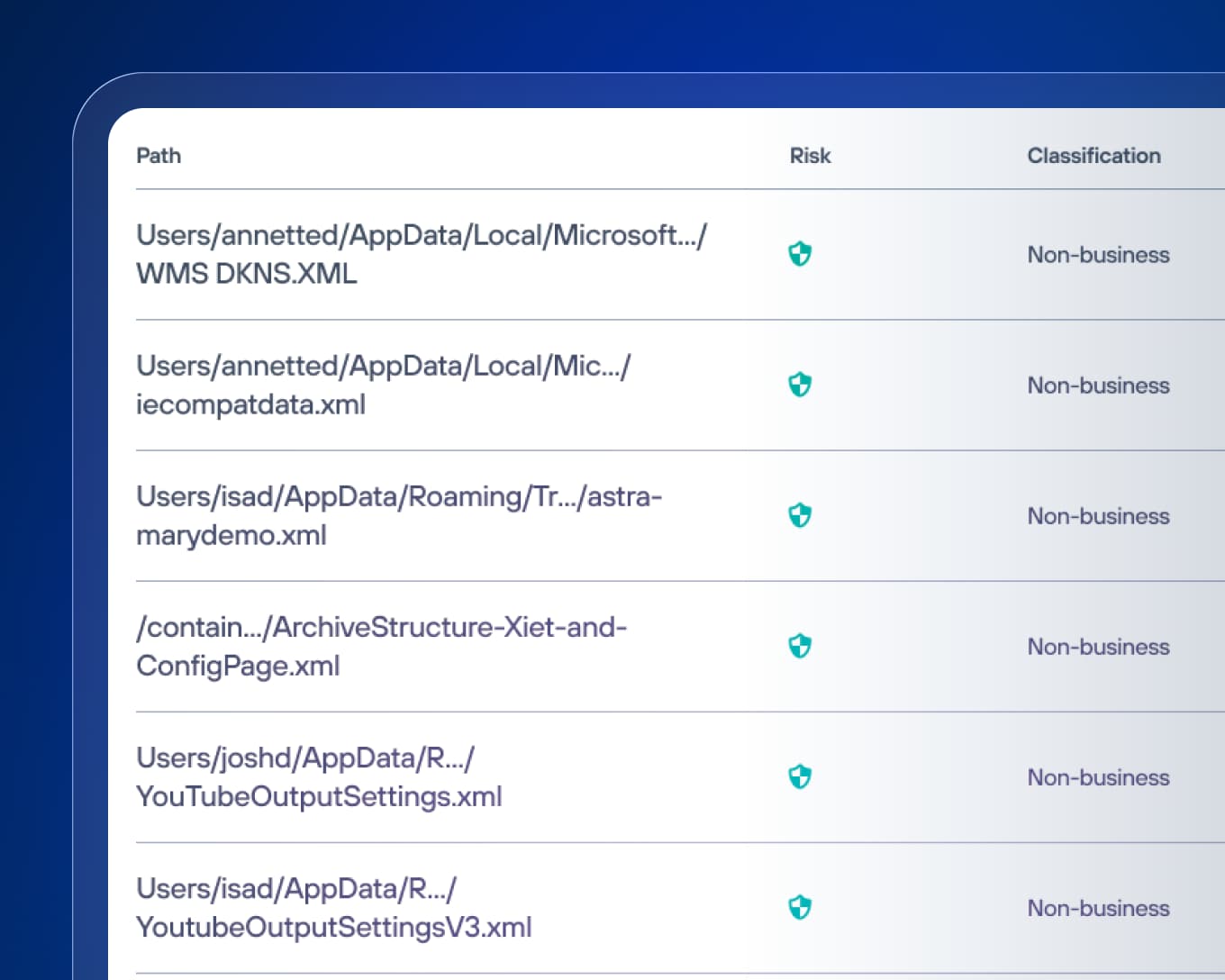
Regularly scan for Redundant, Obsolete or Trivial (ROT) data and enforce data lifecycle policies to shrink your attack surface.

Reliably Manage Compliance
Automatically track compliance against global and industry-specific regulations and create audit-ready reports.
Safely Enable AI with DSPM
Run regular data discovery and classification scans to tag sensitive data appropriately. Identify overpermissioned and ROT data before users share it with AI applications such as Claude, ChatGPT and Copilot, or unknowingly give AI agents access. Maintain visibility into interactions on sanctioned AI platforms with API integrations.
Prevent Data Loss with DLP
Combine superior visibility of sensitive data with the expert control that Forcepoint Data Loss Prevention (DLP) delivers. Configure and deploy policies in minutes with over 1,800 pre-defined templates and classifiers for a range of countries and highly regulated industries.

Scale and Unify with a Modern Approach
Secure AI activity, protect against insider risk and power hybrid work with Forcepoint Data Security Cloud – a unified platform that discovers data, understands risk and applies real-time protection with the help of ARIA, an embedded AI assistant.
Why Organizations Choose Forcepoint DSPM
See Everything. Miss Nothing
Gain complete visibility into structured and unstructured data across the cloud and on premises, from SQL and Oracle to Databricks and Snowflake.
Classify with Unparalleled Accuracy
Utilize advanced AI Mesh technology that learns from your business and industry to efficiently and accurately classify data with minimal configuration, reducing false positives and enhancing incident alert accuracy.
Find Hidden Risk Before Danger Strikes
Actionable insights empower you to enforce least-privileged permissions, move sensitive data from over-exposed locations, and address data sovereignty issues.
Effortlessly Maintain Compliance
Simplify compliance processes with automation to ensure consistent and continuous alignment with evolving regulations, reducing manual effort.


Trial DSPM on OneDrive
A data risk assessment proactively discovers threats to your data, whether it's unclassified sensitive files or over-permissioned users. Start a free data risk assessment of your OneDrive in as few as five minutes to trial Forcepoint DSPM on your own.
Strengthen Your Data Posture



Rapidly and precisely identify sensitive data at rest with AI Mesh technology paired with Forcepoint’s proven DLP classifiers for maximum efficiency.

Extend visibility and control to all your regulated data, eliminate gaps and generate automated reports to demonstrate compliance.
Gain a centralized view of your data and where it lives, and enforce Principle of Least Privilege across cloud, SaaS and on-prem systems for effective governance.





"The customer-friendly UI paired with its easy way to retrieve information and make them readable is a huge benefit."
Manager, IT Security and Risk Management, Mar. 24, 2026
Analyst recommended.
User approved.
Forcepoint recognized as a Strong Performer in The Forrester Wave™: Data Security Platforms, Q1 2025
Forcepoint DSPM has a 4.6 rating from 24 reviews on Gartner Peer Insights (May 2026).
Implement Data Security Posture Management Best Practices
Stay up to date with recent trends, expert insight and analysts analysis for Data Security Posture Management
Gartner®: Market Guide for Data Security Posture Management
Build a Future-Proof Data Governance Strategy for the AI Era
Forcepoint Data Risk Assessment Solution Brief
Forcepoint Data Security Posture Management Datasheet
Forcepoint AI‑native DSPM and DDR: A Full On-Demand Demo
Forcepoint DSPM Works Well With
Frequently Asked Questions
What is Data Security Posture Management (DSPM)?
Data Security Posture Management is a security solution that continuously scans data repositories, automatically classifies sensitive data, maps user access permissions, flags risks to your data security posture and facilitates remediations of these risks. DSPM solutions can identify risks such as sensitive files in exposed locations, over-permissive access permissions, or the spread of ROT (Redundant, Obsolete, Trivial) data. DSPM solutions provide for the means to secure these risks by moving file, deleting files and changing access permissions. Forcepoint’s AI-native DSPM follows this same model: it continuously inventories structured and unstructured data, uses AI Mesh technology to accurately classify that data across file storage, cloud apps and on-prem locations, and assesses whether any of that data is at risk through a variety of lenses.
How do DSPM solutions work?
Most DSPM platforms follow a recurring lifecycle: discover data (structured and unstructured across multiple clouds and on-prem), classify it by sensitivity and business context, assess and prioritize risks (such as overprivileged access or mislocated data), remediate misconfigurations or unsafe access and then monitor continuously to keep data classification and security posture current. Forcepoint DSPM implements this with AI Mesh, an AI classification architecture using small language models and deep neural networks.
Forcepoint DSPM will scan integrated data sources, identify and categorize high-risk data, and recommend next steps for remediation so the team can adjust permissions, move misplaced data, clean up Redundant, Obsolete or Trivial (ROT) data and fix sovereignty issues instead of stopping at reports. Forcepoint DSPM sees beyond files into enterprise databases and data lakes, so the same discovery, classification and adaptive enforcement model covers both structured and unstructured data in a single, unified platform alongside Forcepoint DDR and DLP.
How does DSPM’s data discovery capabilities work?
DSPM continuously discovers data across cloud, network and on-premises storage to uncover and classify sensitive data no matter where it may be hiding. Finding sensitive data is the crucial first step in protecting it. DSPM solutions scan your entire data ecosystem such as:
- Cloud platforms (AWS, Azure, GCP)
- SaaS applications (Microsoft 365, Salesforce)
- On-premises storage and databases
Modern DSPM software maintains continuous visibility as data moves and changes through built-in functionality or solution integrations.
What data classification and risk assessment abilities does a DSPM solution provide?
A mature DSPM solution delivers a chain of capabilities:
- Data discovery and AI-powered classification: automated scanning of cloud, SaaS and on-prem stores, using finely tuned AI to accurately classify structured and unstructured data by sensitivity and business purpose, with tunable models to reduce false positives.
- Data risk assessment plus risk analysis and prioritization: building an inventory of sensitive data, then scoring risk based on exposure, over-permissive access and business impact so teams focus on the most critical datasets first; Forcepoint uses risk scoring and financial-impact estimates to prioritize mitigation.
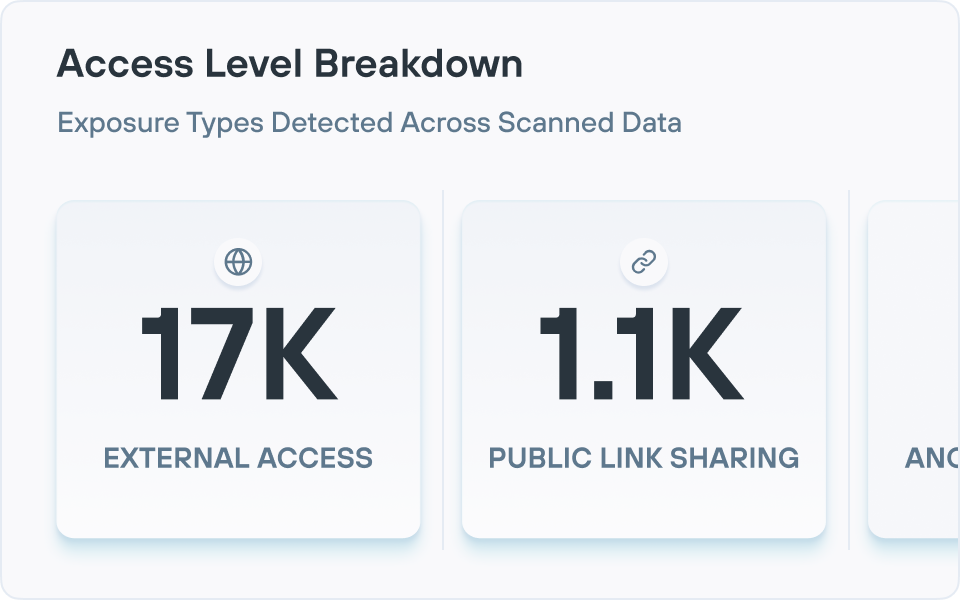
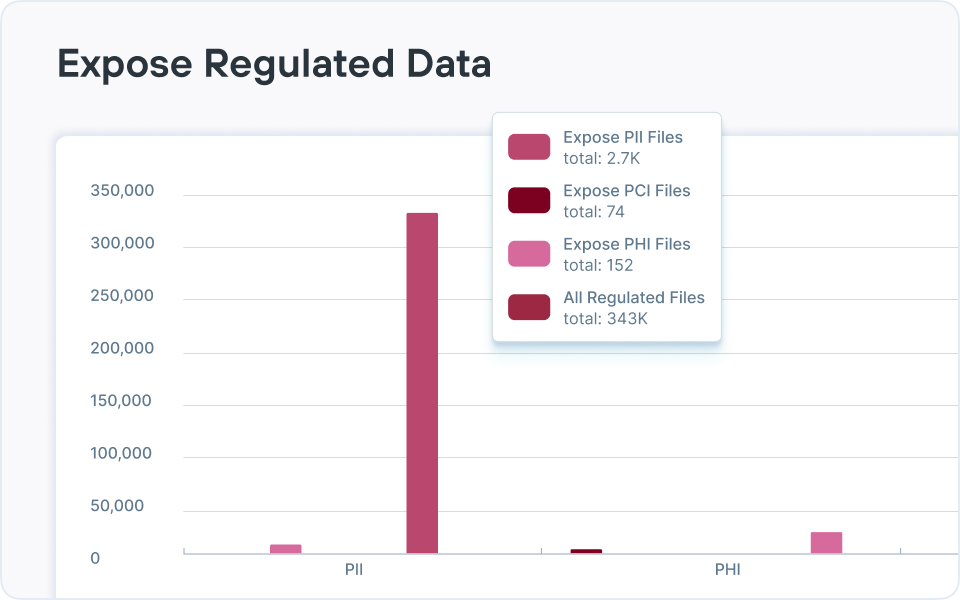
- Access governance: surfacing who has access to which data, highlighting public or external sharing, inactive accounts and overshared folders, with deep visibility into permissions via directory integrations.
- Compliance and reporting: generating dashboards, audit trails and framework-aligned reports (for regulations like GDPR or HIPAA) that map regulated data and simplify audits; Forcepoint adds policy templates, automated reporting and explainable AI classification to streamline demonstrating compliance across hybrid environments.
How does a DSPM platform help organizations manage and remediate risk?
Modern DSPM platforms provide a consistent way to identify sensitive data at scale across the enterprise and map user access permissions. This allows DSPM platforms to identify risks to sensitive data from over-permissioned access rights (which violate the principle of least privilege) including public exposure of regulated data, files stored in improper locations, and ROT (redundant, obsolete, trivial) data risks. Administrators can use the controls from DSPM platforms to delete redundant and obsolete data to reduce the organizations attack surface, as well as move files to more secure locations and change access permissions to align with the principle of least privilege.
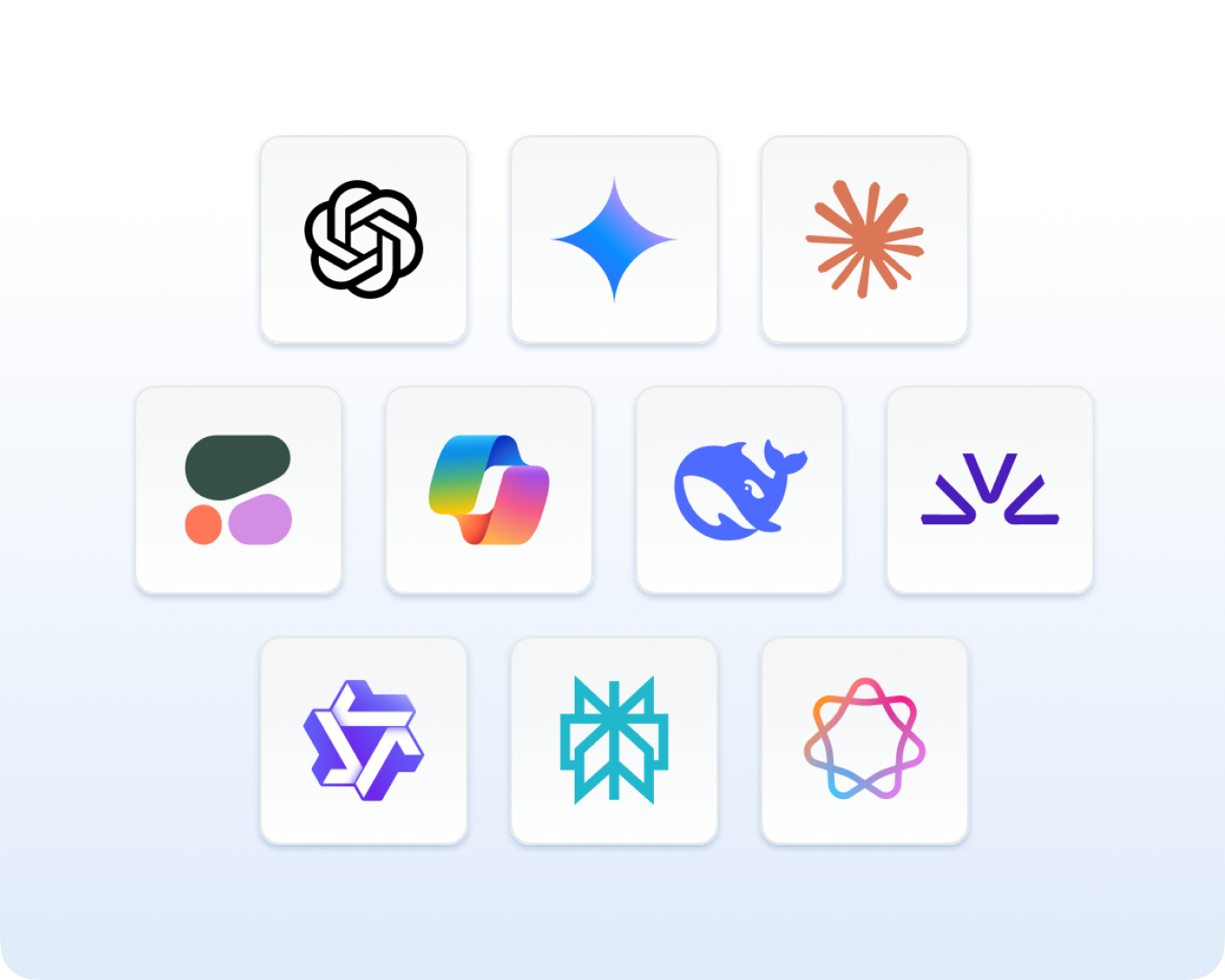
How does reporting and analytics work within DSPM software?
DSPM solutions include reporting and analytics capabilities that provide visibility into an organization's overall data security status. These reporting capabilities typically feature dashboards showing where sensitive data exists across environments, highlighting specific risk factors such as ROT (redundant, obsolete, trivial) data, over-permissioned files, mislocated information and duplicated content. Security teams can use these insights to track metrics over time and prioritize remediation efforts where they'll have the greatest impact.
Is Forcepoint DSPM deployed on-premises or in the cloud?
Forcepoint DSPM can be deployed locally on-premises, in private clouds or as a SaaS service.
How does Forcepoint DSPM use AI and automation?
Automation enables continuous, large-scale data discovery and classification across enterprise environments. Artificial intelligence's primary value lies in delivering highly accurate data classification while reducing false positives. AI brings the precision needed to confidently distinguish between truly sensitive data and benign information that might trigger traditional rule-based systems. For DSPM solutions to confidently incorporate these capabilities, modern solutions must handle a wide range of file types, from PDFs to CAD, as well as understand an even broader array of data fields to assign correct classifications and adjust for compliance requirements. This includes leveraging GenAI capabilities, deep neural network classifiers and other predictive AI technologies working together.
What are the key benefits organizations could get from implementing a DSPM platform?
The benefits of Data Security Posture Management can boil down to four outcomes:
- Reduce risk
- Streamline compliance
- Increase productivity
- Cut costs
Does DSPM integrate with other security technologies?
DSPM rarely operates in isolation. Most organizations integrate it with complementary security technologies to create a comprehensive data protection strategy. The insights DSPM software provides about data location, sensitivity and risk naturally enhance other security tools such as:
- Data Detection and Response (DDR)
- Data Loss Prevention (DLP)
- Cloud Access Security Broker (CASB)
- Identity and Access Management (IAM)
How does DSPM differ from legacy data classification tools?
Unlike traditional tools that work with known data repositories using predefined rules, DSPM continuously discovers both known and unknown data across environments, leveraging AI for more accurate classification and providing context about access patterns and security controls.
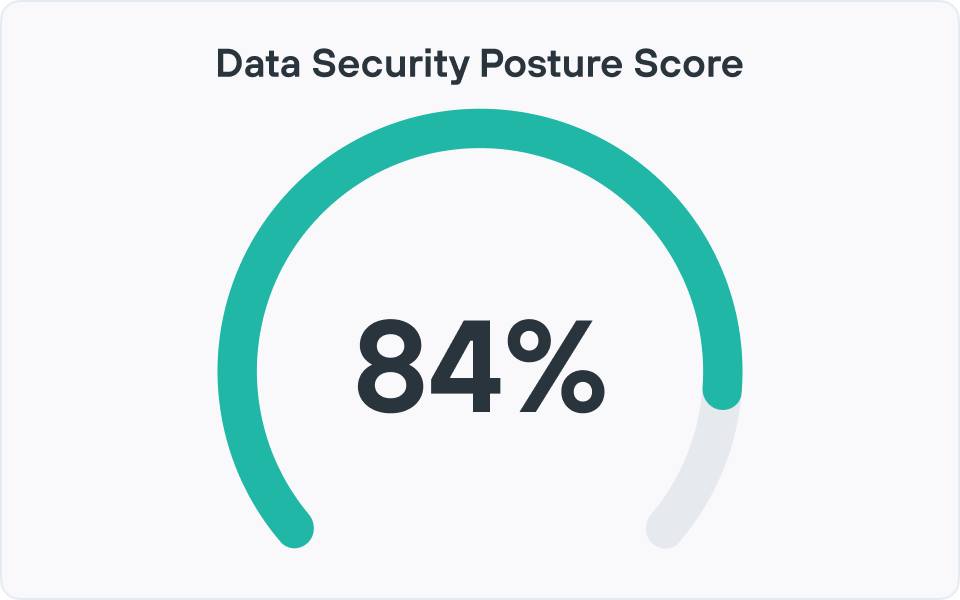
How does DSPM help assess security posture?
Data Security Posture Management (DSPM) assesses security posture by continuously discovering where sensitive data lives (cloud, SaaS, on-prem), classifying it by sensitivity and mapping who has access to it.
Forcepoint DSPM uses its AI Mesh engine plus broad connectors to inventory structured and unstructured data. It highlights overexposed files, ROT data and risky permissions, and correlates them into a data risk assessment.
It then provides high-performance monitoring and analytics to show how much sensitive data is at risk, which locations and business units drive the most exposure, and how changes over time impact overall data risk. These insights are surfaced through detailed dashboards and reporting, giving security and compliance teams a current, measurable view of their data security posture instead of point-in-time audits.
What is the difference between SSPM and CSPM and DSPM?
CSPM (Cloud Security Posture Management) focuses on cloud infrastructure: configurations, network controls, identities and platform services. It finds and helps fix misconfigurations in IaaS and PaaS environments, not the contents of the data itself.
SSPM (SaaS Security Posture Management) focuses on SaaS apps: security settings, access and integrations across services like Microsoft 365, Salesforce and more.
DSPM (Data Security Posture Management) focuses specifically on the data—discovering, classifying, and assessing risk around sensitive information wherever it is stored. It answers, “what data do we have, where is it, who can access it and how risky is that exposure?”
Does Forcepoint DSPM have real-time monitoring and risk detection?
Yes, when it is augmented with Data Detection & Response (DDR). Forcepoint DDR provides near real-time streaming capabilities in addition to DSPM’s regular scans, updating dashboards with exposure levels and file lineage details to automatically flag anomalies and potential breaches in the moment, as events unfold.
How does DSPM enhance cloud security?
DSPM enhances cloud security by giving full visibility into sensitive data stored across cloud storage, SaaS platforms and databases. It shows exactly what data exists, how sensitive it is, where it resides and how it’s shared.
Forcepoint DSPM scans major cloud providers and identity sources to uncover overexposed data, excessive permissions and mislocated sensitive content that traditional cloud tools miss. With this context, security teams can enforce least-privilege access in the cloud, prioritize remediation based on real business and regulatory impact, and integrate DSPM findings with DLP and other controls.
What are the benefits of using DSPM in cloud security?
Using DSPM in cloud environments delivers concrete outcomes: reduced data exposure (through overexposure detection and permission cleanup), fewer blind spots across multi-cloud and SaaS, and better protection for IP and regulated data.
Forcepoint AI Mesh improves the classification accuracy of Forcepoint DSPM, which directly cuts false positives and helps teams focus on real risk.
It also improves operational efficiency via automation, integrated dashboards and reporting. It shortens investigation and remediation cycles, lowers storage and governance costs by addressing ROT data and addresses compliance readiness for audits and data protection regulations.
Does DSPM help with identity threat detection and response?
DSPM is not an Identity Threat Detection & Response (ITDR) platform, but Forcepoint DSPM does detect identity-related risks tied to data. It maps which users and groups can access sensitive files, highlights over-permissioned or high-impact “risky users,” and surfaces suspicious access patterns via analytics and alerts.
These insights let security teams quickly investigate potential identity misuse (e.g., a user with excessive access to critical data) and take targeted actions such as revoking access, tightening sharing, or triggering workflows in existing security tools – strengthening identity-centric data protection without guessing.
How does DSPM detect and evaluate sensitive data exposure?
Forcepoint DSPM uses connectors to scan cloud and on-prem data stores at scale, then applies AI Mesh classification and configurable detectors to identify sensitive data (PII, PCI, PHI, IP, etc.) based on content and context.
It then evaluates exposure by analyzing sharing settings and permissions to flag data that is public, externally shared, overshared internally, mislocated, or associated with risky users, and quantify that risk within dashboards and reports so teams can prioritize remediation.
How does DSPM simplify compliance reporting?
Forcepoint DSPM centralizes evidence needed for regulations like GDPR, HIPAA and other privacy and sovereignty requirements by continuously documenting where regulated data resides and who can access it. Its reporting function and analytics suite show compliance readiness and data risk across popular frameworks.
What dashboards are included in Forcepoint DSPM for compliance teams?
Forcepoint DSPM analytics dashboards include predefined dashboards such as overexposure analysis, ransomware exposure analysis, critical data duplication, risky user detection, data retention, misplaced data, data risk assessment and incident tracking for data control violations.
Compliance teams can also create custom dashboards using built-in widgets (counters, charts, tables, incident views, etc.) driven by DSPM’s query language and export these views as reports to allow them to tailor oversight to specific regulations, business units or data categories without custom development.