1.2万多客户的选择不会错










































难以查看云端数据?
很多人有同样的困扰。市场上有超过 800,000 个云应用,传统的数据安全工具在应对 SaaS 策略管理的复杂性和 AI 导致的数据泛滥时已不堪重负。
的组织经历过
严重的云安全事件*
的企业数据存储在
云端*
的企业缺乏对
AI 智能体可访问数据的可见性***
使用 CASB 查看并保护 SaaS 和 GenAI 应用中的数据
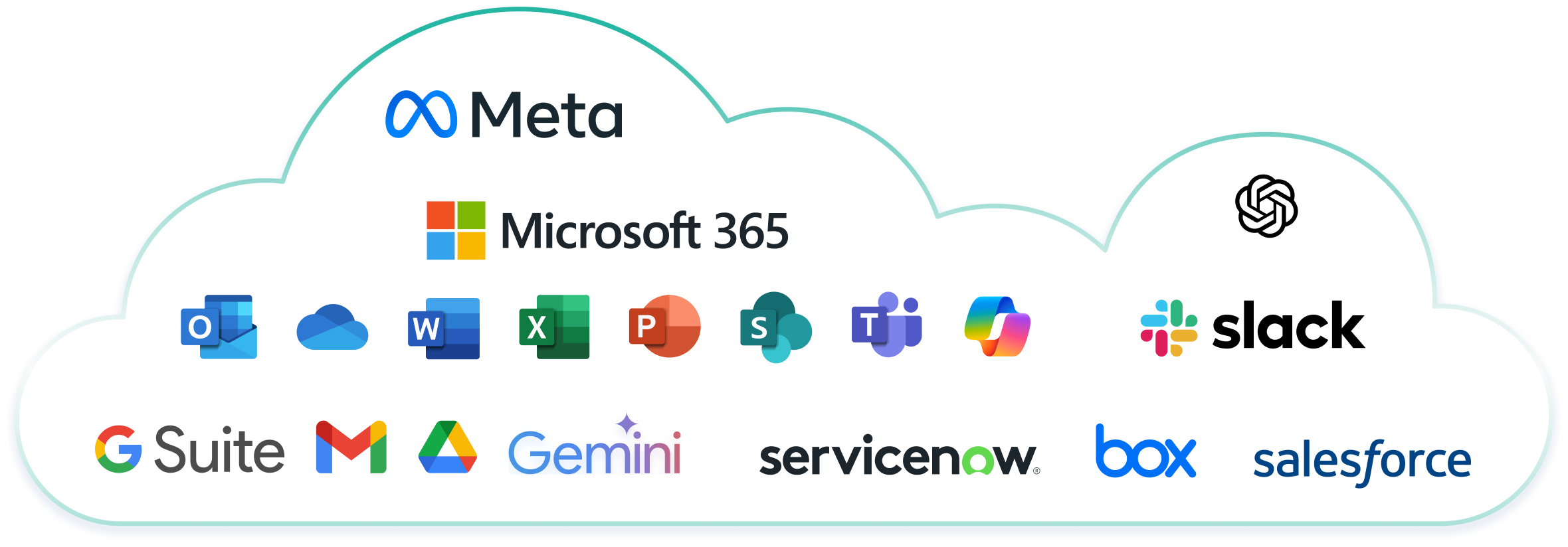
Forcepoint CASB 确保对全球最流行的 SaaS 应用(如 Microsoft 365、Google Workspace 和 Salesforce)的访问安全。该解决方案会扫描企业批准的应用中的静态敏感数据,并通过与 Forcepoint Data Loss Prevention (DLP) 软件的集成提供对数据的真正可见性和控制。
Forcepoint CASB 解决方案对比竞争对手
Forcepoint | 传统安全供应商 | 传统网络供应商 | |
Cloud Access Security Broker (CASB) 功能
| |||
数据安全功能
|
免责声明:产品比较基于截至 2023 年 3 月 1 日同一供应商提供的产品内功能和跨产品组合集成。产品比较不包括与第三方供应商的集成。 功能比较基于截至 2023 年 3 月 1 日各供应商发布的最新版本。信息来源于截至 2023 年 3 月 1 日从公共网站、论坛、分析师文章和产品资料表中收集的数据。
确保 SaaS 安全的 CASB 关键功能
深入了解 SaaS 数据
全面了解 SaaS 应用中的数据。预构建且可定制的仪表板使安全、合规和审计团队能够通过直观的洞察快速采取行动。
保护数据并简化合规
将业界一流的 DLP 扩展到 CASB 以防止云端数据泄露。通过 1,700 多个分类器和策略模板简化策略配置和合规管理。
确保从任何设备进行安全访问
使混合型员工能够从任何设备和地点,通过零信任机制安全地访问 SaaS 应用。无代理部署模式使用户保持高效并保护数据。

自动威胁补救
自动检测并响应 SaaS 应用中的 SaaS 威胁,如恶意软件、数据过度暴露和策略违规,最大限度地降低泄露影响。
为亚太地区客户优化的卓越性能
- 全新新加坡 CASB API 节点,为区域工作负载提供最高 5 倍的扫描速度提升。
- 借助专用 API 节点,SharePoint 扫描能力现已超过每小时 50,000 个站点。
- 更低延迟,确保更快的运行效率,并为亚太地区客户带来更优质的用户体验。


Closing the SaaS Security Gap: A Practical Guide for CISOs and CIOs
Overpermissioned files. Misplaced sensitive content. Documents owned by employees who left six months ago. Unmanaged AI tools like Copilot or ChatGPT absorbing corporate knowledge. These are the new frontiers of data risk. Discover the hidden SaaS data security risks in your organization and learn how to mitigate them in this comprehensive guide.
客户为什么选择 Forcepoint CASB 解决方案
客户为什么选择 Forcepoint CASB 解决方案
"Very good experience in getting visibility into and protection of cloud application, policy enforcement and user behavior."
Read the Review常见问题
Forcepoint CASB 如何与众多云应用集成?
Forcepoint CASB 使用基于 API、反向代理和正向代理方法的组合,与超过 800,000 个云应用集成。 这种混合方法使我们能够监控和保护几乎任何 SaaS、IaaS 或私有云环境中的数据,无论用户如何访问这些应用。
- 基于 API:最适合深入了解 Microsoft 365、Salesforce 或 Google Workspace 等受到认可的应用。它使我们能够审计用户活动、检测威胁和实施 DLP 策略,甚至可追溯。
- 反向代理:非常适合在线保护来自托管设备的云流量。它支持实时会话控制,例如阻止下载或应用升级身份验证。
- 正向代理:在保护非托管设备或 BYOD 场景时非常有用。它通过 Forcepoint 的代理将出站流量路由到云服务,从而在数据到达应用之前便可实施策略。
Cloud Access Security Broker (CASB) 解决方案?
Cloud Access Security Broker (CASB) 是充当云用户和云提供商之间的中介的安全解决方案。 它可以阻止恶意软件并通过加密保护数据,使数据流无法被未经授权方读取,从而保护组织免受网络攻击。CASB 为 SaaS 应用提供数据安全和访问管理,确保云使用的安全和合规。
CASB 如何运作和功能?
CASB 软件通过实施组织的安全策略,确保内部 IT 架构和云供应商环境之间的数据安全流动。 它管理用户与云应用及其内部数据的交互,确保对云资源的安全且合规的访问。
CASB 的目的是什么?
CASB 的主要目的是确保托管和非托管云应用中的数据安全。 它允许组织创建策略来管理数据使用,从而降低数据泄露等风险。CASB 还通过识别和管理未经授权的 SaaS 应用来应对影子 IT 的挑战。
云访问安全代理 (CASB) 如何增强云安全?
CASB 通过提供对云应用使用情况的了解、实施数据安全策略和防范威胁来增强云安全。 它监控用户活动、检测异常并确保符合监管标准。通过充当用户和云服务之间的安全检查点,云访问安全代理 (CASB) 有助于防止数据泄露和未经授权的访问。
云访问安全代理 (CASB) 如何帮助实现合规性?
云访问安全代理 (CASB) 通过监控云使用情况并实施符合 GDPR、HIPAA、SOX 和 PCI DSS 等行业法规的策略,帮助实现合规性。它们提供详细的报告和审计来证明合规性,帮助组织避免罚款和法律问题。云访问安全代理 (CASB) 还确保数据按照地区数据保护法律进行存储和处理。
CASB 如何应对影子 IT 的挑战?
CASB 通过发现和监控组织内使用的未经授权的云应用来应对影子 IT 的挑战。 它们提供对所有云服务的可见性,评估其风险级别并实施安全策略,以管理和控制这些云服务的使用。这有助于组织降低与未经批准的云应用相关的风险。
为什么 CASB 对于使用 SaaS 应用的组织非常重要?
CASB 对于使用 SaaS 应用的组织至关重要,因为它们提供全面的安全和合规管理。 它们帮助组织获得对云端数据的控制,防范网络威胁,并确保云使用符合监管要求。CASB 还通过识别和管理未经授权的云应用来解决影子 IT 的挑战。
有效的 CASB 有哪些支柱?
可见性:企业需要了解云应用使用情况,包括用户帐户、部门、位置和设备,以确保信息资产受到控制并符合治理流程。
数据安全:CASB 通过监控云文件存储和防止未经授权的数据共享来增强 Data Loss Prevention (DLP),而传统的 DLP 产品可能会忽略这些方面。
威胁防护:CASB 检测可疑的内部行为,并降低前员工可能仍然访问包含敏感信息的云应用所带来的风险。
合规性:CASB 帮助组织遵守 SOX、HIPAA、PCI DSS、NIST、CJIS、MAS 和 ISO 27001 等地区法规,确保数据隐私和安全。
自带设备、影子 IT 和云使用增加:CASB 为托管和非托管设备实施精细的访问策略,解决自带设备策略、SaaS 应用和影子 IT 带来的挑战。
CASB 解决方案有哪些主要功能?
CASB 解决方案的主要功能包括:
可见性:监控并报告云应用使用情况。
数据安全:加密数据并实施 Data Loss Prevention (DLP) 策略。
威胁防护:检测并缓解基于云的威胁。
合规:确保符合行业法规和标准。
访问控制:管理用户对云应用和数据的访问。
CASB 解决方案有哪些优势?
CASB 为使用 Microsoft 365、Workspace 和 Salesforce 等流行 SaaS 应用的企业改善数据安全。 主要优势包括:
增强对 SaaS 应用中数据的可见性和控制。
防范基于云的威胁。
确保对众多 SaaS 应用的安全访问。
更好地遵守行业特定和全球数据隐私法规。
如何计算 CASB 节省的成本?
部署 CASB 解决方案可以通过以下方式降低运营成本:
高效管理:从单一平台为所有云服务实施安全策略,减少对庞大安全团队的需求。
提高敏捷性:安全的云采用可提高生产力、加快业务应用交付、简化并购活动并减少技术债务。
更高程度的自动化:自动化的发现、分类、策略实施和补救可最大限度地减少云安全管理所需的资源。
消除冗余云应用:识别并删除不必要的云应用,降低云服务总体成本。
提高利用效率:全面的云服务清单有助于 IT 团队优化支出并减少利用不足的情况。
CASB 与 DLP 有何不同?
CASB 结合各种技术来保护云应用和数据,充当用户和云服务之间的防火墙、过滤器和代理。 它们执行发现云应用、评估风险和实施安全策略等功能。 CASB 使用网关、日志数据、端点代理和 API 来监控和分析云活动。
DLP 解决方案采用各种技术来监控 IT 环境中的数据流动,检测潜在的泄露或滥用,并阻止用户操作,以保护数据。
将 CASB 与 DLP 集成有哪些优势?
将 CASB 与 DLP 集成具有多项优势:
覆盖范围更广:云端全面的 DLP 覆盖。
更强大的保护:增强云迁移期间的数据安全。
统一策略:利用云端和本地基础设施的现有 DLP 策略。
更深入的洞察:更好地了解云端的用户行为和数据使用情况。
* Snyk
** Exploding Topics
*** SailPoint