NIS2: Effective Incident Management Will Save You Precious Time
Part 3 of our NIS2 Series
0 dakika okuma

Arjuna Ranaweera
In the previous blog post, we discussed how risk management plays a critical role with complying with NIS2. Now, with this third post in our NIS2 series, we turn our attention to incident management and discuss how Incident management and data security are closely connected aspects of complying with NIS2.
NIS2 requires organizations to have incident management procedures in place to ensure that they can quickly and effectively detect, respond to, and recover from cyber incidents.
NIS2 focuses on enhancing the cybersecurity and resilience of critical infrastructure and services, and effective incident management is critical for responding to and mitigating cybersecurity incidents while maintaining data security.
A strong incident management process can assist organisations by:
- Reducing the impact of cyber incidents: By having a clear and well-defined incident management plan, organizations can quickly contain and mitigate the impact of cyber incidents. This can minimize the costs associated with downtime, lost productivity, and reputational damage.
- Saving time with robust incident reporting: NIS2 outlines in articles 7 (crisis management framework to address incidents and crises), article 8 (designation of competent authorities as the primary point of contact for cybersecurity incidents) and article 9 (establish computer security incident response teams or CSIRTs). Overall NIS2 requires organizations to report incidents to the National Centre of Cyber Security within 24 hours of becoming aware of a significant incident. Organisations are expected to provide a final report no later than one month after the initial Incident Notification. An effective Incident management procedure will help organizations to ensure that they can meet these reporting requirements.
How can Forcepoint help?
Forcepoint has been a leader in empowering organizations to secure their data and key to this is enabling companies to remain compliant with regulations globally. With Forcepoint Data Security Everywhere strategy (and Data-first SASE), we provide a greater visibility and control of the most critical data to an organisation, wherever it resides.
NIS2 requires organisations to implement security procedures for employees with access to sensitive or important data, including policies for data access. As ever-growing consumption of cloud applications and organisations continuing to embrace hybrid working, it is imperative to deploy a data security solution that covers all the channels, wherever the users are.
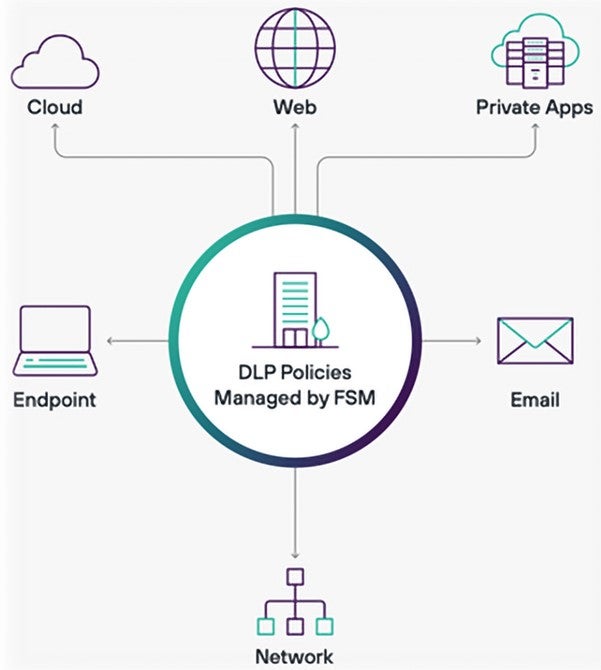
- Forcepoint Data Security Everywhere can easily manage global policies across every major channel, whether its endpoint, network, cloud, web, private applications, or email all from a single incident reporting user interface.
- We can simplify your work with the most pre-defined templates, policies, and classifiers of any DLP provider in the industry. This can dramatically streamline your incident management so you can focus on what’s most important, eliminating risk so that your people can be increasingly productive.
- Through our Forcepoint ONE Data-first SASE platform, we can extend data security controls to cloud applications using our integrated CASB technology. Agentless data security can empower organisations to encourage usage of BYOD in a secure manner.
What about Incident Management?
Forcepoint Data Security Everywhere includes a robust incident management console with forensic evidence of data exfiltration attempts for all channels. This is highly important during any incident investigation, where you can filter and extract the relevant information quickly from a single reporting console.
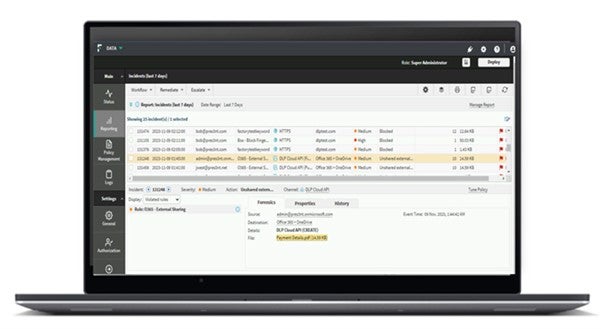 Risk-based DLP Incident Ranking enables organisations to correlate multiple data security incidents into meaningful data security cases and assign a risk score to each case. This enables organisations to reduce the alert noise and focus on the high priority incidents.
Risk-based DLP Incident Ranking enables organisations to correlate multiple data security incidents into meaningful data security cases and assign a risk score to each case. This enables organisations to reduce the alert noise and focus on the high priority incidents.

Through Exposed Rest APIs, organisations can automate incident management workflows and support business processes relying on data security incidents through automation and service tools. This provides the ability to handle large scale deployment easily using customer in-house grown tools and can integrate with most kind of 3rd party systems, such as ServiceNow.
Stay tuned for our fourth and final blog in the NIS2 series coming soon. In it, we will uncover the secrets of the human factor and how addressing it wisely can be of pivotal importance in terms of NIS2 compliance.
In case you missed them, here are the previous posts in our NIS2 series:

Arjuna Ranaweera
Daha fazla makale oku Arjuna RanaweeraArjuna Ranaweera is a member of the EMEA Solution Architects team at Forcepoint, with over 17 years of experience in Cyber Security. Arjuna has held various technical roles across Vendors, Channel Partners and End customers, helping him to gain in-depth experience across several security domains such as Cloud Security, Data Security and Network Security.
- Understanding NIS2
Makalede
 Understanding NIS2Read Part 4
Understanding NIS2Read Part 4
X-Labs
Get insight, analysis & news straight to your inbox

Konuya Gel
Siber Güvenlik
Siber güvenlik dünyasındaki en son trendleri ve konuları kapsayan bir podcast
Şimdi Dinle








