Forcepoint Named a ’Leader’ in Forrester™ Wave: Data Security Platforms, Q1 2023 Report
0 分钟阅读

Forcepoint is honored to be recognized as a “Leader” in Forrester’s recent report "The Forrester Wave: Data Security Platforms, Q1 2023."
"Organizations seeking a strong technology partner for enabling a Zero Trust approach and risk-adaptive data security controls should consider Forcepoint.
- The Forrester Wave™: Data Security Platforms, Q1 2023
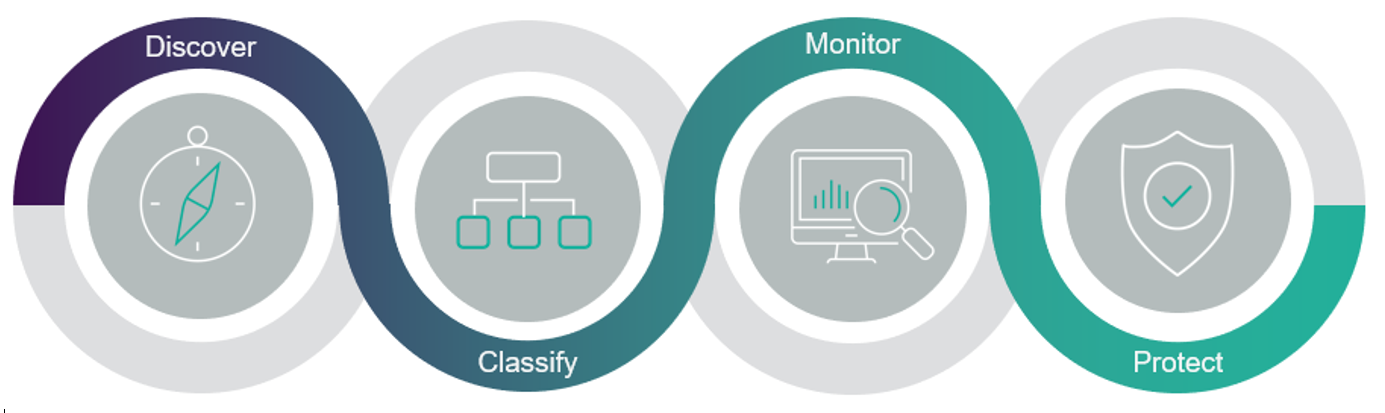
In our view, the report accurately acknowledges and addresses the rapid changes in the security environment that have impacted where data is stored and how it is used. We feel this report validates the vision that Forcepoint has been working toward - building a comprehensive data security strategy where the key pillars of discover, classify, monitor, and protect are vital. We continue to build according to these pillars as we strive to be the premier security solution provider for distributed businesses that need to safeguard data everywhere it is used—on the endpoint, in the cloud, and everywhere in between.
We’re proud that the changes we've made in the last two years have propelled us ahead of traditional DLP competitors as well as a new generation of cloud-first vendors. We’re building a truly holistic data security platform that brings together a unique set of technologies:
- Forcepoint ONE. One of the most common overall customer requests we hear is the need to simplify security. And that’s one of the main reasons we built Forcepoint ONE—a cloud-native Security Service Edge (SSE) platform. It’s the foundation of our “Data-first SASE” Zero-Trust platform for security, offering strong DLP SaaS capabilities for cloud (CASB), web (SWG) and private application (ZTNA) channels. It also includes outstanding data encryption, data masking and digital rights management. Coming soon, we will be adding some exciting new capabilities for our on-prem DLP customers that will allow them to take advantage of the best-of-class capabilities from the Forcepoint ONE data security platform.
- Exposure Management. Last year we released Forcepoint Data Classification and Forcepoint Data Visibility powered by Getvisibility. These solutions focus on exposure management—leveraging an artificial Intelligence/machine learning powered cloud model to deliver highly precise classification predictions, high-performance data discovery along with strong data access governance. All of this helps customers to shrink the "blast radius" of a potential data breach, dramatically reducing both data exfiltration risk and non-compliance risk.
- Risk-Adaptive Protection. While other competitors are just beginning to offer a basic "adaptive protection" solution, we've been delivering true Risk-Adaptive Protection for data loss prevention for several years. We now have over 150 customizable Indicators of Behavior (IoBs) that automate policy enforcement actions based on the exact level of risk individuals bring to the organization at any moment.
- Forcepoint Insider Threat. This cutting-edge user activity monitoring solution can provide DVR-like capabilities that enable properly authorized security teams to see actual user behavior surrounding a policy incident.
- Zero Trust Content Disarm and Reconstruction (ZT CDR). This is a relatively recent addition for Forcepoint data security that helps protect organizations from inbound attacks or outbound data theft (steganography) hidden in documents and images.
We encourage you to look at Forcepoint’s placement as a Leader and to read more in the Forrester report. If you have any questions, please don’t hesitate to reach out to your channel partner or Forcepoint sales representative. You can also request a demo to see our data security approach in action.

Kevin Oliveira
阅读更多文章 Kevin OliveiraKevin serves as Senior Product Marketing Manager for Forcepoint’s Data Security products and solutions. He has over 20 years experience helping enterprises with their data and security initiatives with leadership positions at Dell EMC and IBM.
 The Forrester Wave™: Data Security Platforms, Q1 2023查看行业分析报告
The Forrester Wave™: Data Security Platforms, Q1 2023查看行业分析报告
X-Labs
直接向您的收件箱发送洞见、分析和新闻










