Forcepoint Data Security Cloud
Data Security Designed
for the AI-Powered Enterprise
AI has fundamentally changed how data is created, shared and exposed.
Data protection now demands a unified and adaptive approach.
Secure AI Without Compromise
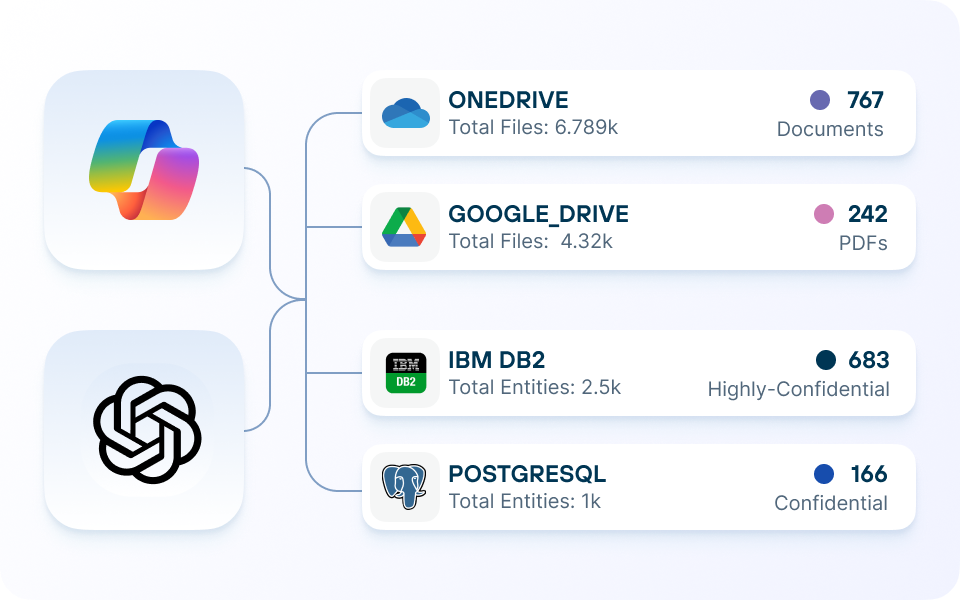
Continuous Data Discovery
Combat data sprawl and the risks that come with it by continuously discovering new data sets across your digital estate, ensuring every file is accounted for.
Highly Accurate Classification
Intelligently tag structured and unstructured data with AI Mesh, a highly networked classification architecture that provides fast and efficient classification.
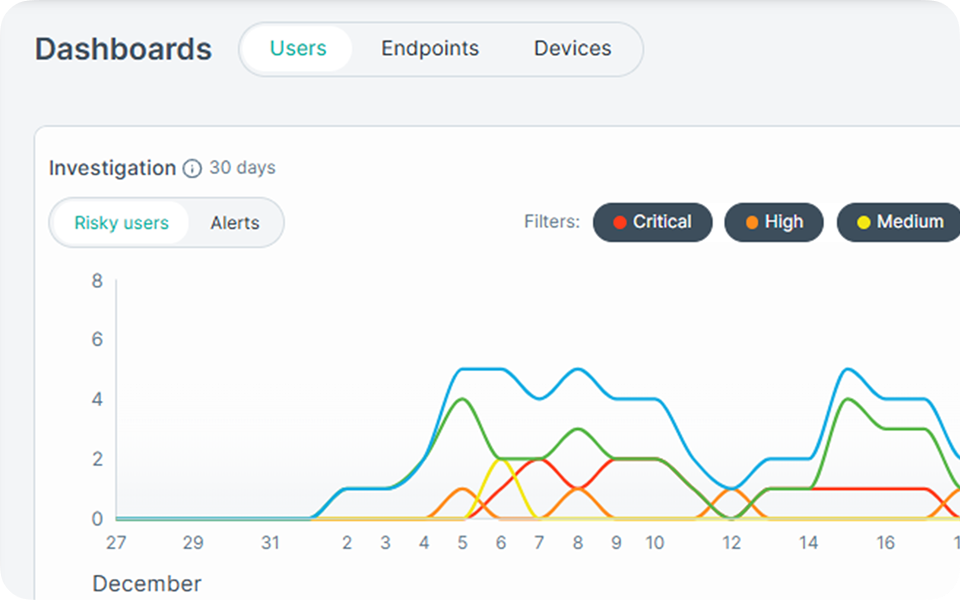
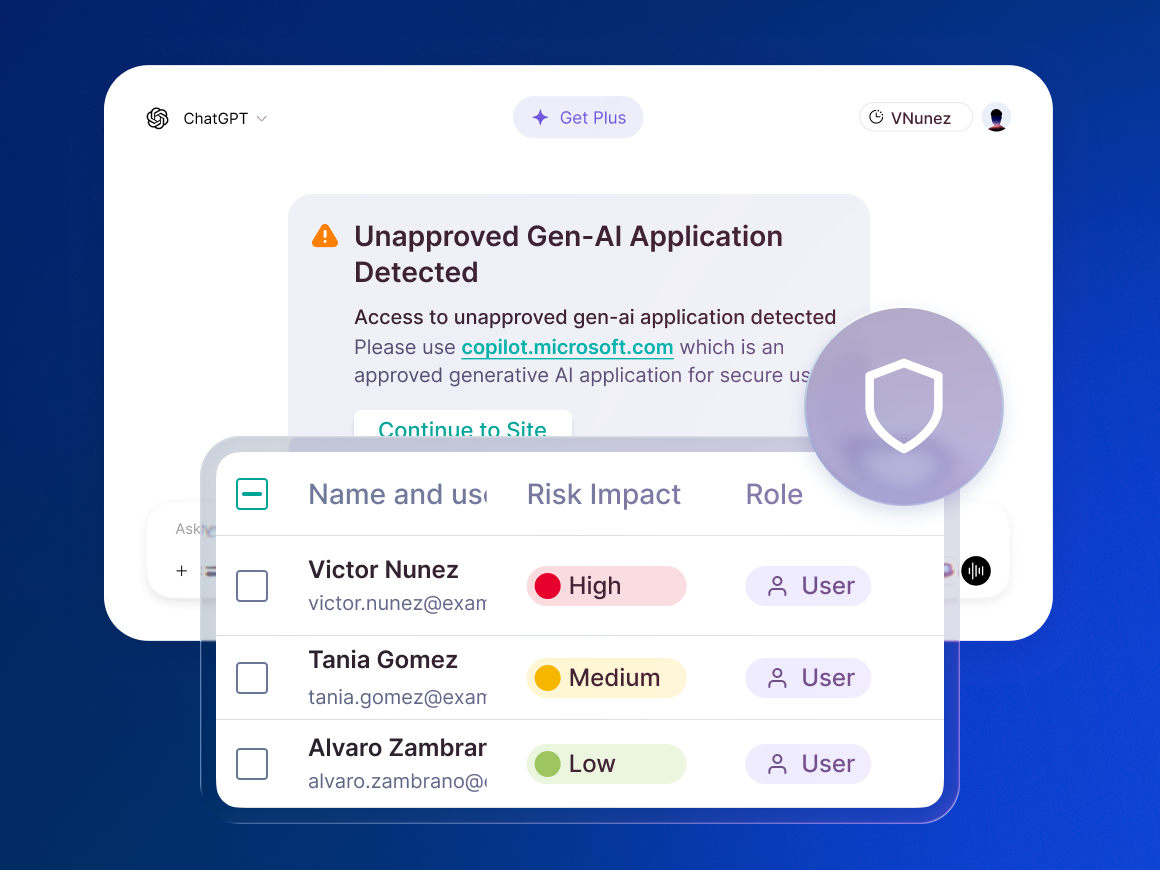
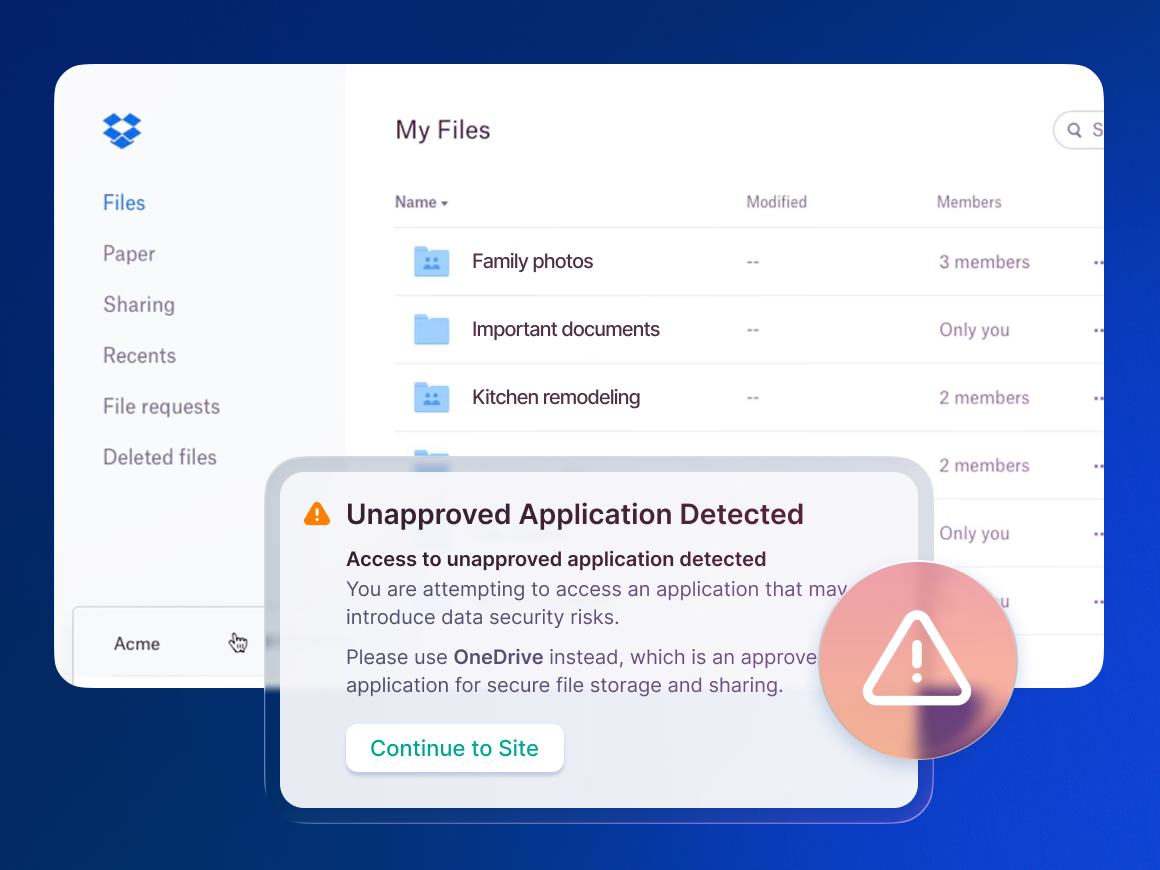
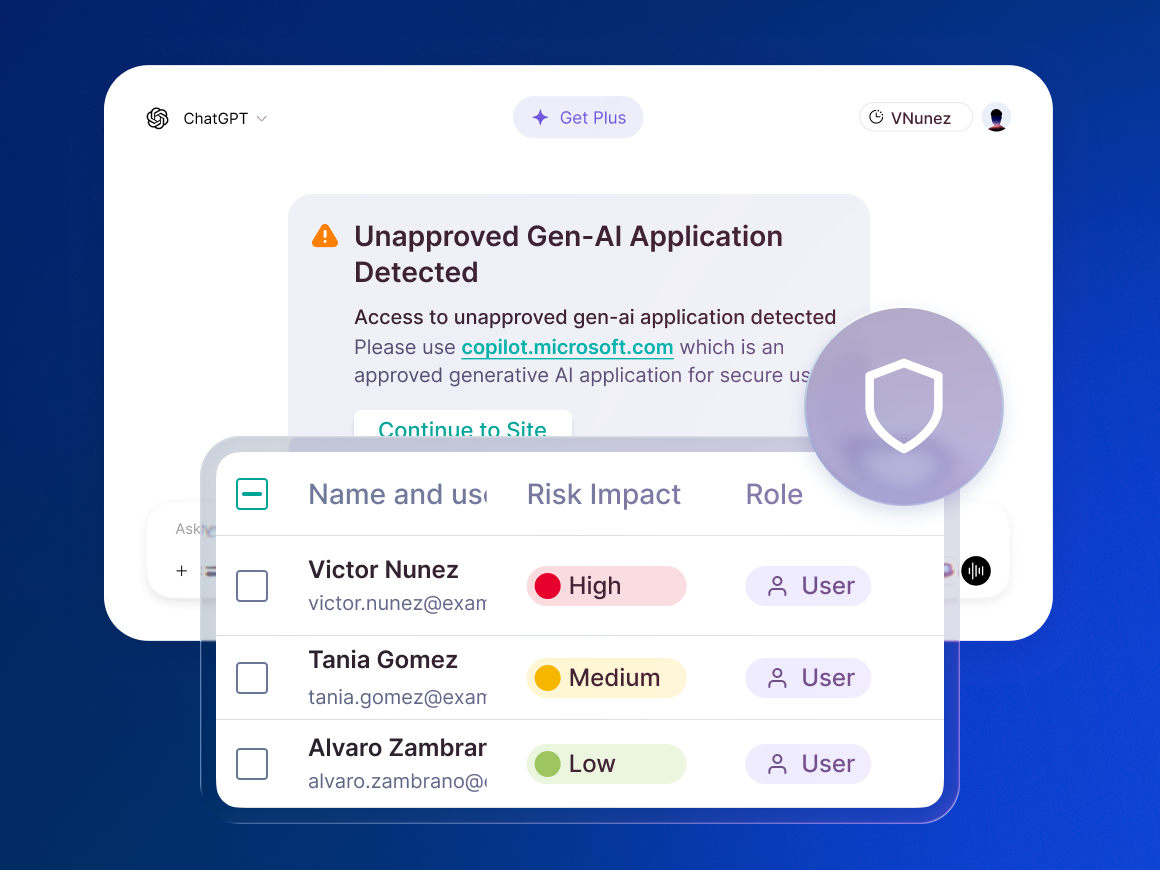
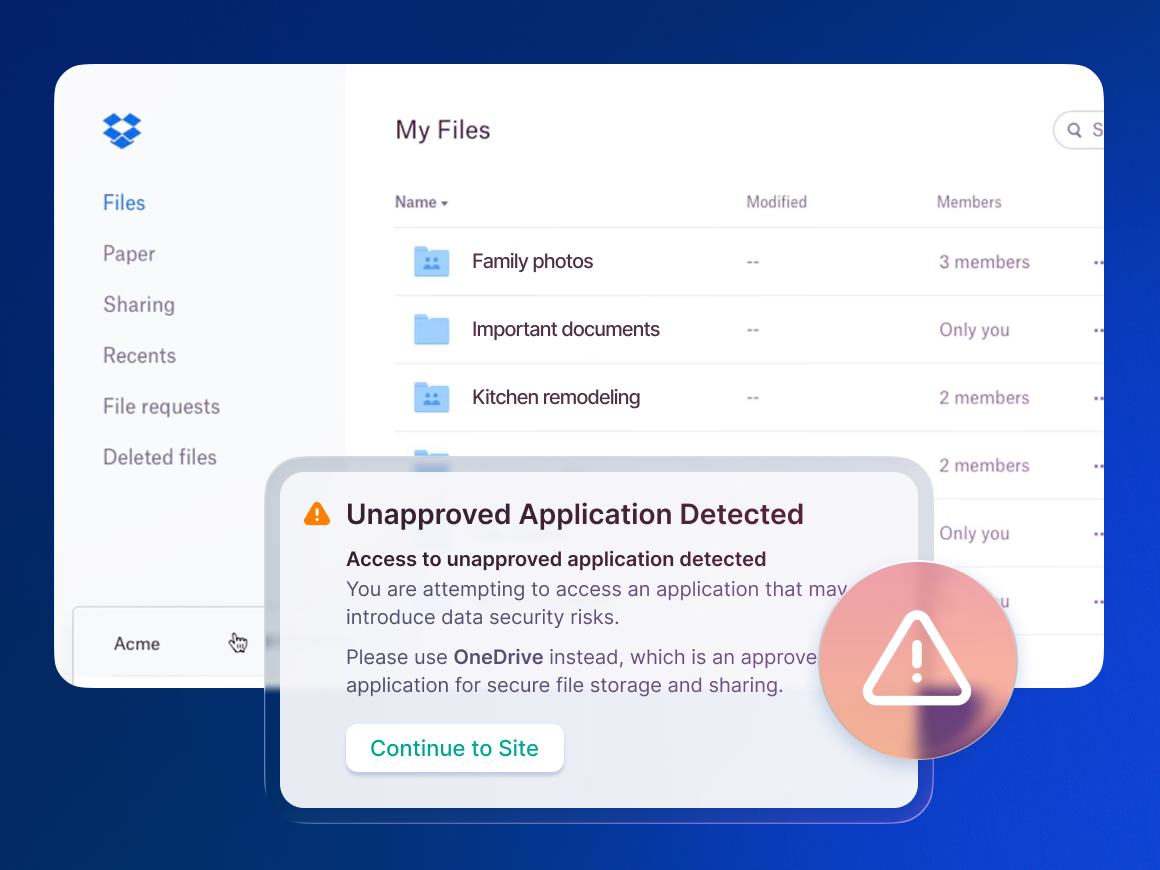
Risk-Adaptive Policy Controls
Apply context to policy enforcement to allow productive users to work securely and mitigate risky incidents as they unfold in real time.
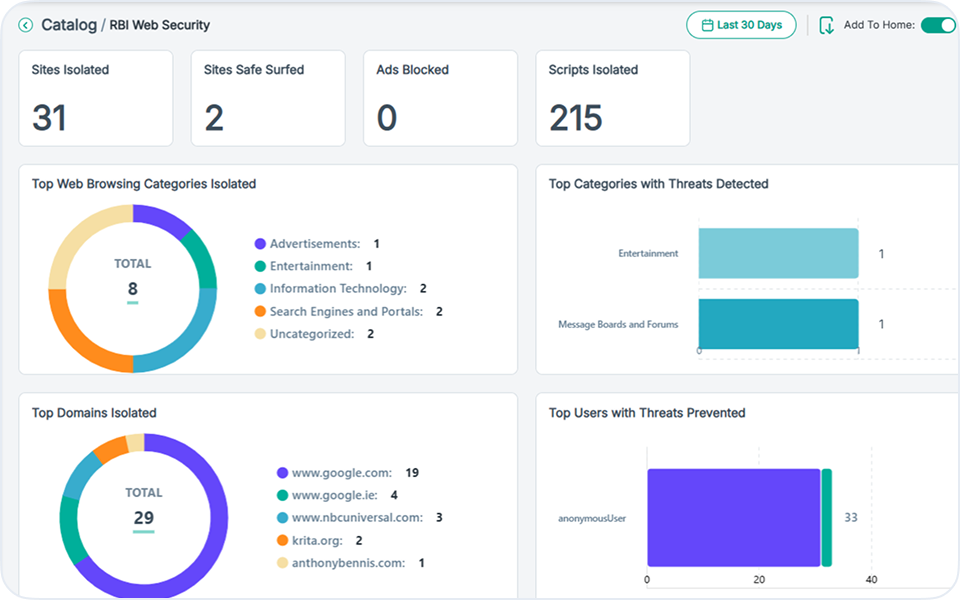
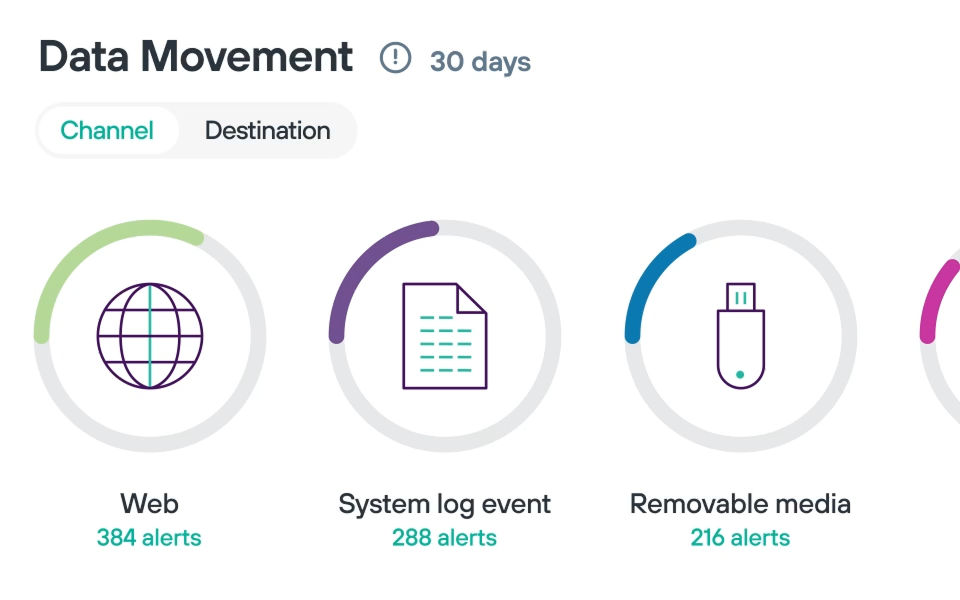
Unified Coverage for Every Channel
Centralize policy administration to configure once and enforce everywhere data goes—across AI, web, cloud, endpoint, network and email—with just a few clicks.
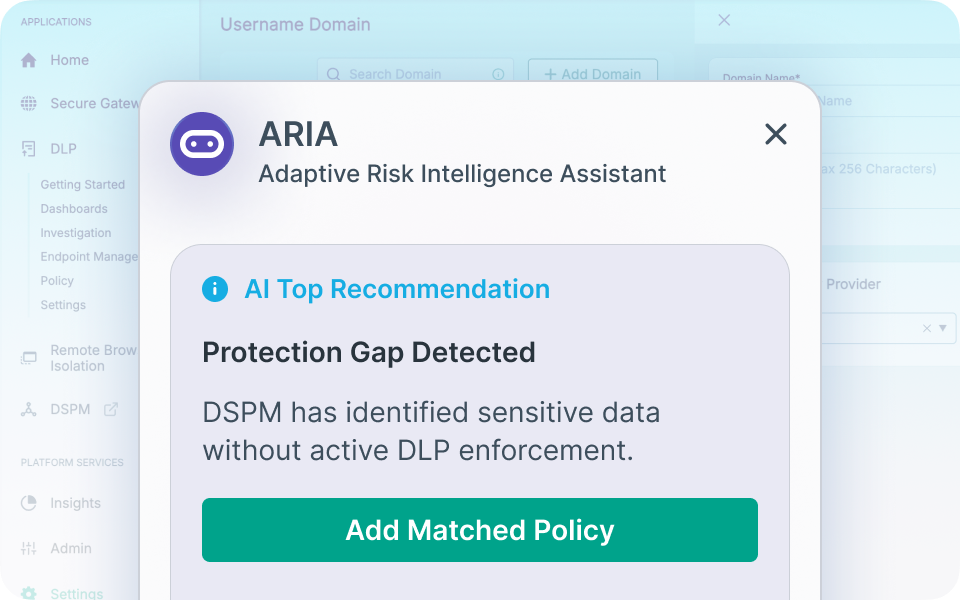
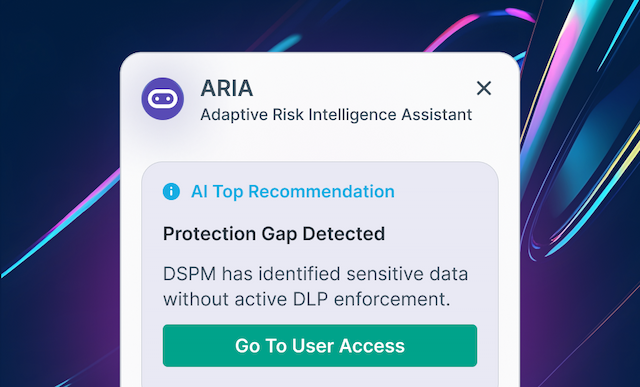
Always-On AI Expert
Forcepoint ARIA is an intelligence layer in Forcepoint Data Security Cloud that correlates cross-solution risk signals and behavioral insights to spot security gaps and deploy protection in seconds.
Deep Platform Integrations
Data Security Cloud serves as a single control plane for the Forcepoint security suite, including Data Loss Prevention, Data Security Posture Management, Data Detection and Response and more.
Data Security Cloud delivers Self-Aware Data Security
Know
your data and its risks
Adapt
controls when risk changes
Protect
sensitive data everywhere

The Stakes Are Only Getting Higher






Failure Is Not an Option

140+
Countries With Privacy and Security Regulations
Companies must be able to enforce and audit their compliance with industry-specific and global regulations

200+
Days to Identify a Breach on Average
Inconsistent visibility of data and incidents delays organizations' abilities to detect breaches

$4.88M
Cost of a Data Breach on Average
A lack of control over file movement and permissions results in costly cyberattacks
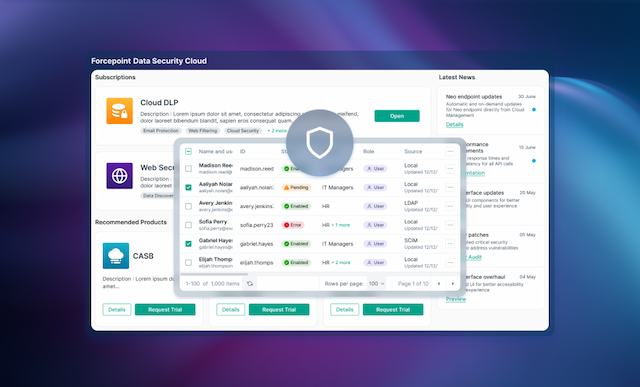
Forcepoint Data Security Cloud:
Uniting Visibility and Control
AI-Powered Assistant
CISO Dashboard Insights
Unified Identity Management
Forensics and Risk Analysis
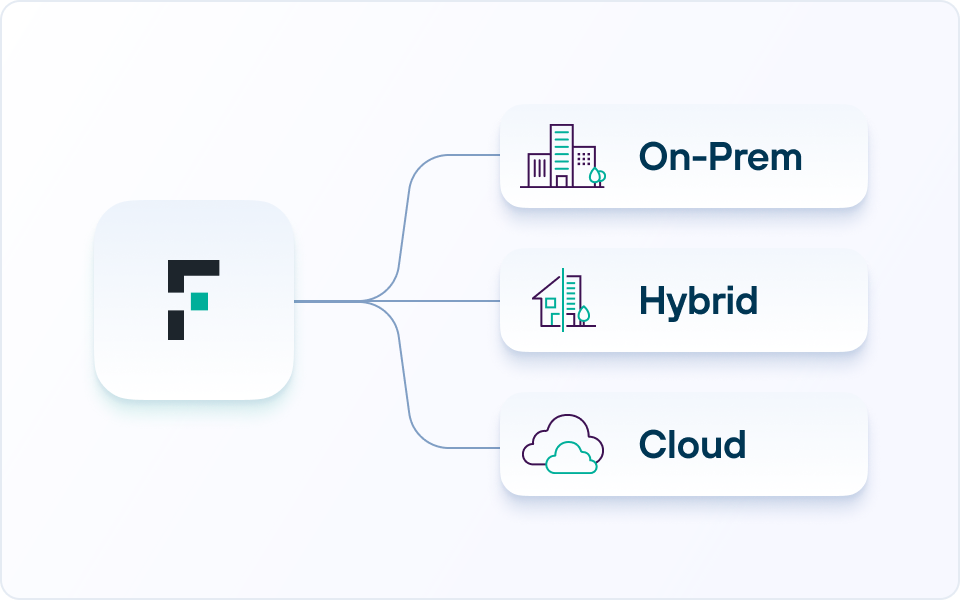
Flexible Cloud Deployment
Coverage for AI-Driven Workflows
Turn Data Security into a Business Advantage


Everything You Need to Know
About Data Security

SOLUTION BRIEF
Forcepoint Data Security Cloud
BROCHURE
A Unified Approach to Protecting Data, Users and AI Workflows
WEBCAST
Forcepoint Data Security Cloud: A Full On-Demand Demo
VIDEO
Forcepoint ARIA: Turn Business Intent into Protection in Seconds
