Accelerate Zero Trust—Data is the key
Data security is the heartbeat of Zero Trust
0 dakika okuma

Kevin Oliveira
Continuing our Activating Zero Trust series, today, I wanted to spend some time looking at data security. If you missed earlier posts, check out the first post on web security and the second post that covers the secure SD-WAN piece.
Zero Trust has become a strong driver in security efforts everywhere. First championed by Forrester in 2010, it started off with a strong focus on the network. It then evolved to include discussion about applications with lots of “zero trust” products that came out to address both the network and underlying applications. One important principle to emerge from the ongoing discussion on Zero Trust is a clear focus on what Zero Trust is ultimately supposed to do.
Put simply, Zero Trust is designed to keep data secure—it’s all about the data.
Here's what Forrester said in The Zero Trust eXtended Ecosystem: Data report in August 2021:
"Data security is a key pillar of Zero Trust, and a daunting task due to its scope."
"Security leaders must continuously assess and mature the organization’s competence when it comes to enabling the appropriate controls for data security and protection."
"Your foundation for controls is based on identifying what “data” and value is for your organization and gaining context about users, their data access and behaviors, and data use activity.”
The true value of Zero Trust is in data security
Data is often talked about in terms such as PII (Personally Identifiable Information) and PHI (Personal Health Information). Looking beyond the privacy and regulatory realms, data that represents anything of value to the organization also must be protected. This broader definition includes business strategies, financial documents, resumes, POs, “confidential” files, many types of unstructured data and much more.
It can even include files such as images and video. Many of these files contain “sensitive” information such as PII and PHI but if it represents value (even if it is not currently being used or part of any current business process) it needs to be protected. All business data is at the center of what needs to be effectively defended when considering what defines a complete Zero Trust solution.
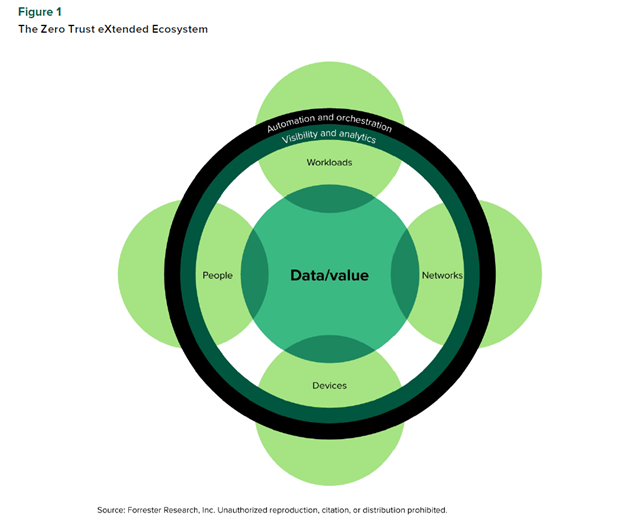
Forcepoint takes data seriously. That’s why we champion the concept of Zero Trust with “Data-first SASE.” We recognize that data is central to a Zero Trust approach. With Data-first SASE, we provide a security framework that focuses on Zero Trust data protection, regardless of where it is located or how it is accessed.
Earlier this year Forrester recognized Forcepoint as a leader in the Forrester Wave™: Data Security Platforms, Q1 2023. In the report, Forrester pointed out that, “Forcepoint delivers on a data-centric approach for Zero Trust.”
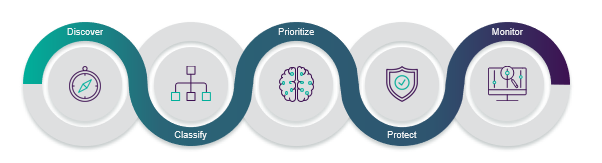
We do this by taking a holistic approach to data security that includes a broad set of products and solutions which keep data secure. We focus on helping customers discover, classify, prioritize, protect and monitor their valuable data. In our view, that’s a comprehensive Zero Trust approach to data security.
For more information on Forcepoint’s Zero Trust Data Security approach – read the eBook “Modernize Your Data Security Strategy”.
Also check out more information on Forcepoint Data Security solutions at https://www.forcepoint.com/use-case/data-security-software-solutions.

Kevin Oliveira
Daha fazla makale oku Kevin OliveiraKevin serves as Senior Product Marketing Manager for Forcepoint’s Data Security products and solutions. He has over 20 years experience helping enterprises with their data and security initiatives with leadership positions at Dell EMC and IBM.
- Modernize Your Data Security StrategyE-kitabı Oku
X-Labs
Get insight, analysis & news straight to your inbox

Konuya Gel
Siber Güvenlik
Siber güvenlik dünyasındaki en son trendleri ve konuları kapsayan bir podcast
Şimdi Dinle