1.2万社以上のお客様に利用されています










































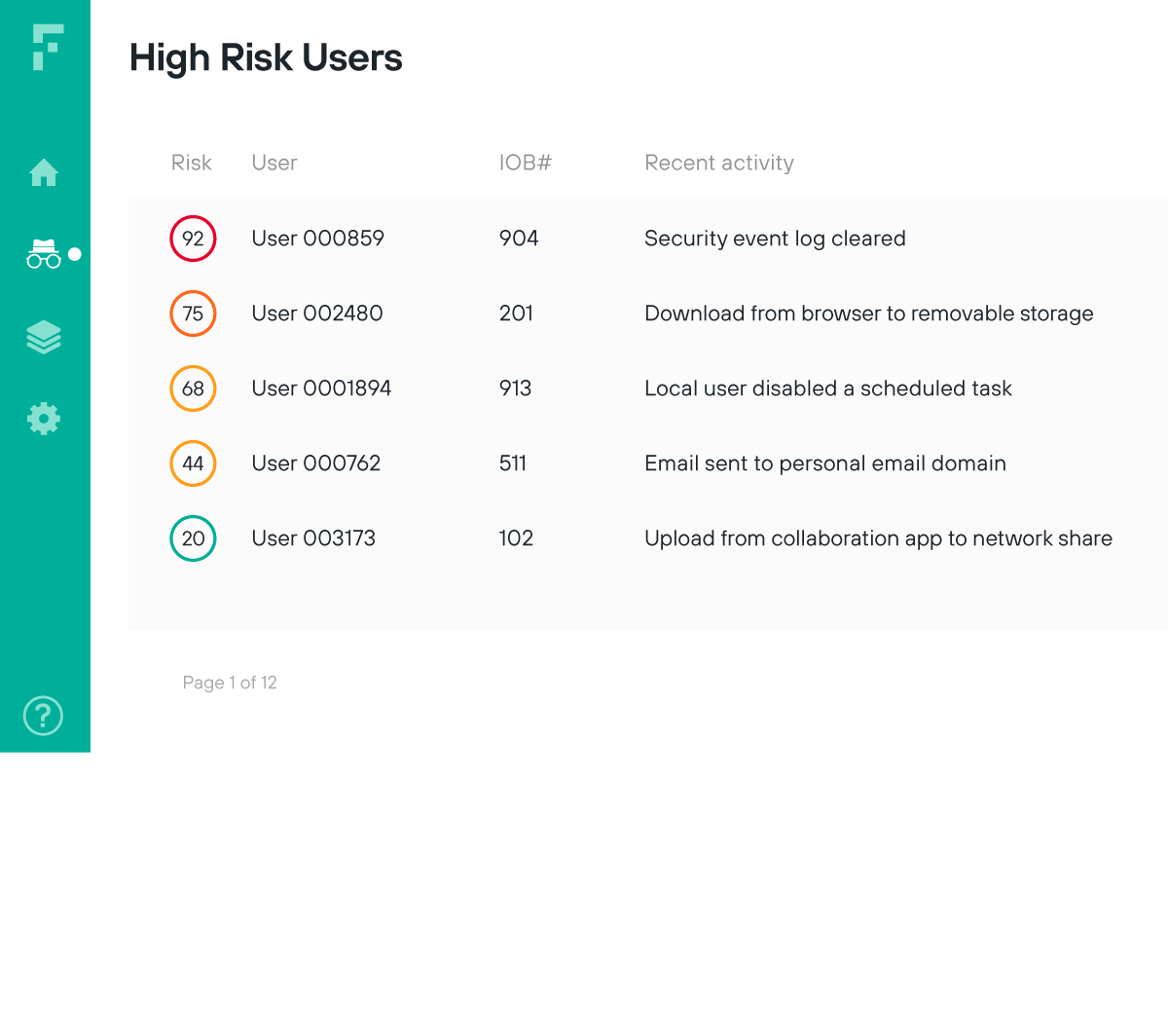
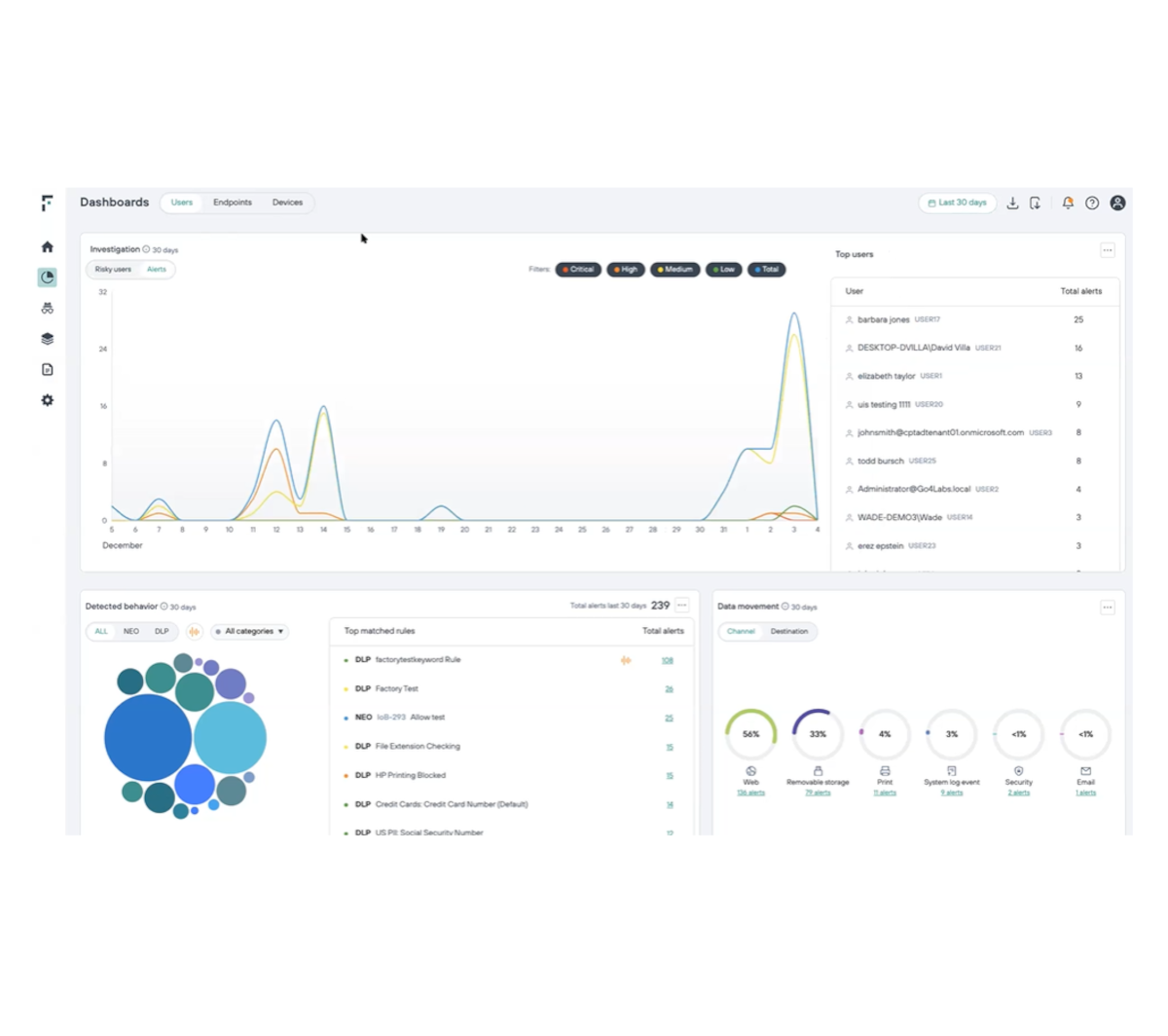
最も早い段階で内部リスクを検出
ユーザーと重要なデータのやり取りを可視化
リスクのある盲点を排除し、ユーザーがリスクの高い行動につながる傾向を完璧に把握します
常に最新のリスクスコアリングでユーザーの行動と意図を理解
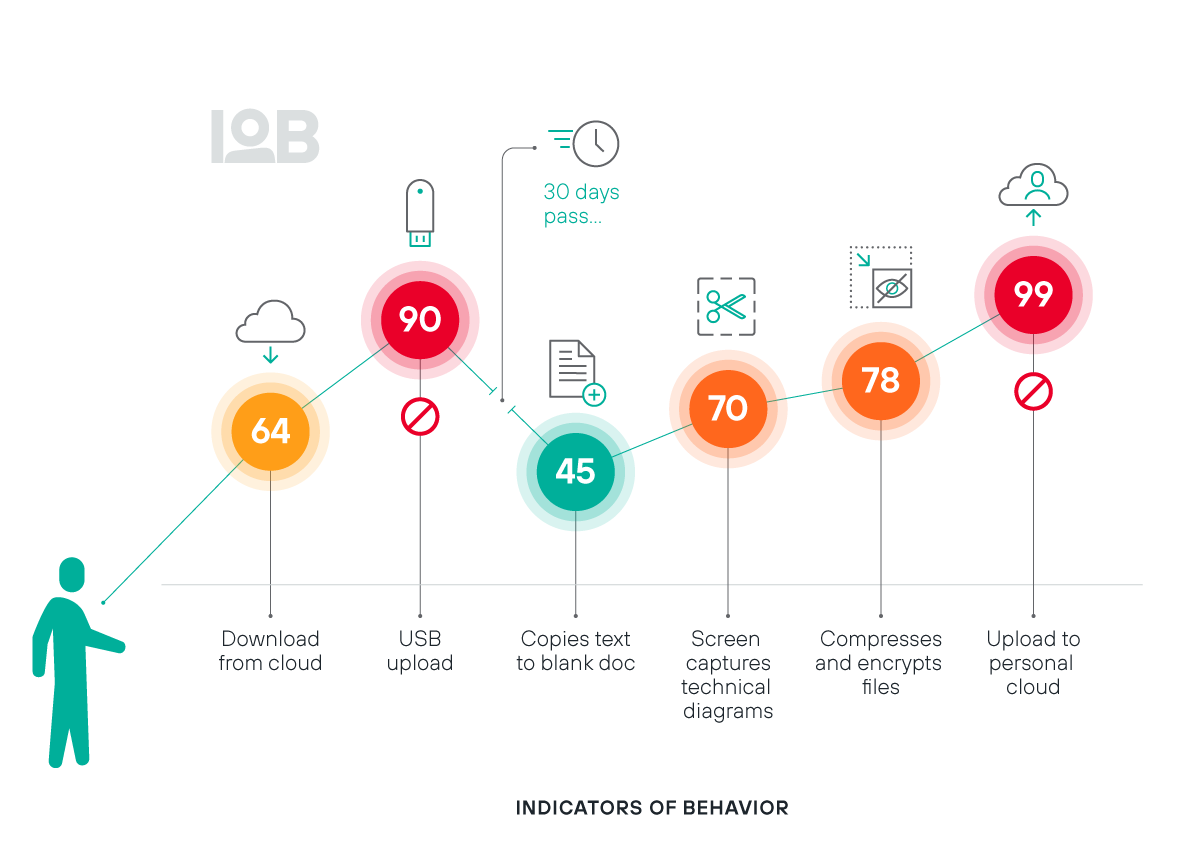
150 以上のIndicators of Behaviors(IOB)によって広範な監視機能を提供
DATASHEET
継続的なユーザー検証によりゼロトラストモデルを実現
認可済みユーザーからのリスクを公開し、検出の最も早い段階で異常な行動としてアナリストにアラートを通知。真のゼロトラストアプローチを実現します
侵害を示唆する異常なユーザーアクティビティに基づきアクセスを制限
ユーザーとデータの進行中のやり取りをリアルタイムでモニタリングし、ユーザーのリスクを検証
INFOGRAPHIC
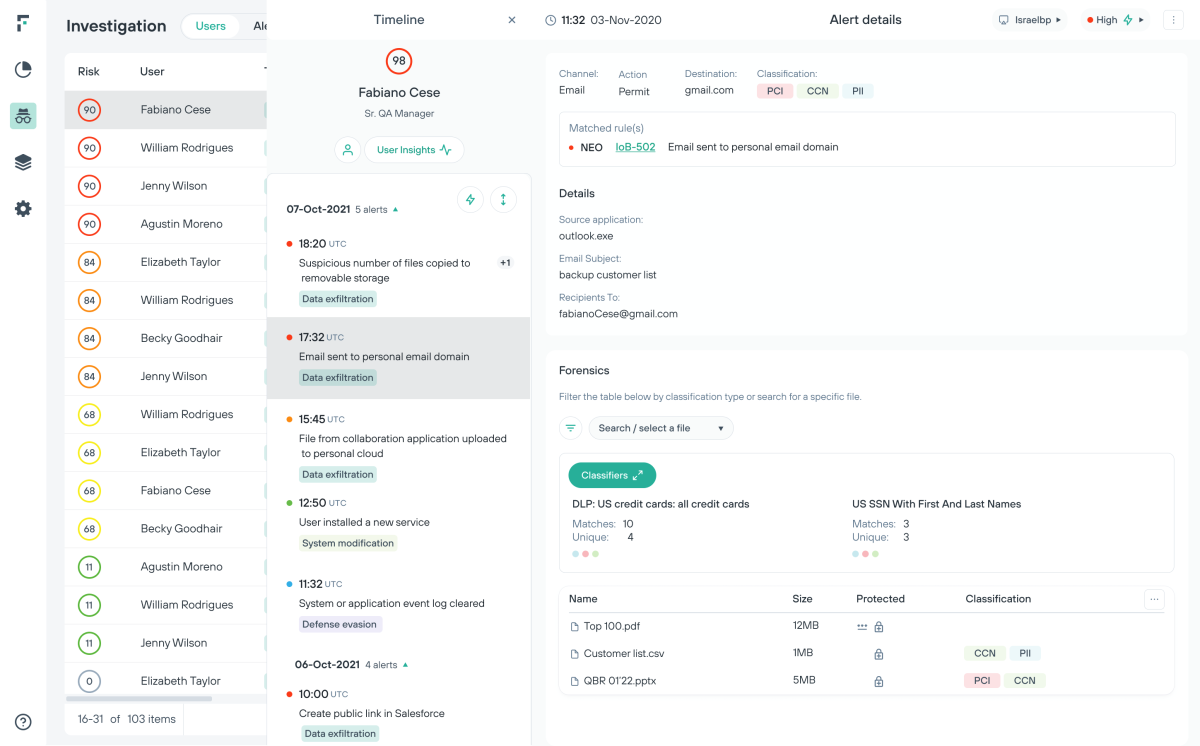
セキュリティアナリストの効率性を最大限に高め、過剰なアラートによる疲弊を低減
Risk-Adaptive Protectionは、イベント中心のアプローチからリスクアプローチに組織のデータセ中心のキュリティ対策を移行させるソリューションです。
ユーザーレベルでポリシー調整を行うことで、データ流出に事前に対処
調査の効率を高め、学習能力をアップ
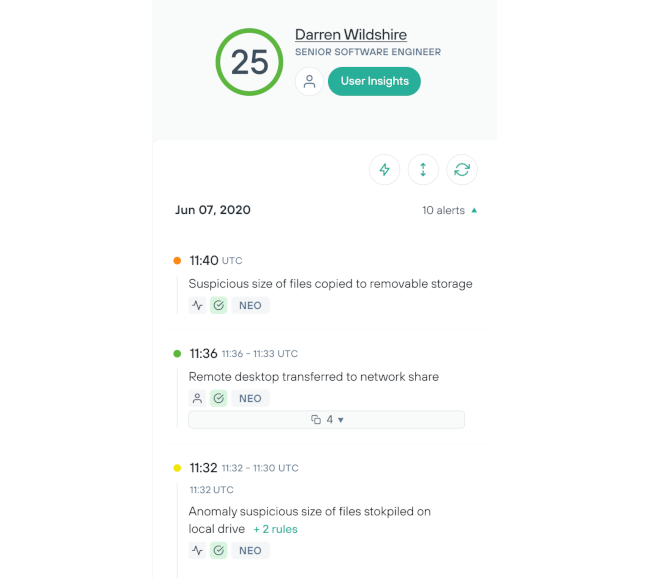
容易かつ効率的に内部リスクを調査
スムーズな実装プロセスとカスタマイズされた自動化のにより、マニュアル操作を低減します。
自動化と誤検知の削減により、ユーザーを調査するアナリストの生産性を向上
メンテナンスの簡単なクラウドのインフラと、30秒で完了するエージェントインストールにより、スタッフの負担を軽減
新たに浮上する脅威にリアルタイムで対応
セキュリティポリシーを自動的に適応させて、ユーザーによるリスクの高い行為をブロックすることで、データ流出を防止します。
アラートの誤検知を減らして、インシデント分析に費やした時間を取り戻します。
リスクの低いユーザーが、潜在的な脅威を避けながら必要な情報にアクセスできるようにします。
ユーザーアクティビティの継続的な監視を通じて、リアルタイムでデータセキュリティを自動化します。

データ損失防止のための実践的エグゼクティブガイド
当社のハンズオンガイドで、あらゆる規模の企業向けにData Loss Prevention (DLP)ソフトウェアを実装するための8つのステップを発見してください。
アナリスト推奨。
ユーザーが認める製品。
Forcepointは、ユーザーや業界アナリストから一貫して情報漏えい防止ソフトウェアやデータセキュリティソフトウェアプロバイダのトップにランク付けされています。
Forcepointは、IDC MarketScape: Worldwide DLP 2025 Vendor Assessmentで「リーダー」に選出されました。
Forcepointは、Frost & Sullivanから2年連続で2024年のグローバルDLPカンパニー・オブ・ザ・イヤーに選ばれました。
Forcepointは、2025年第1四半期のThe Forrester Wave™: Data Security Platformsで、 強力なパフォーマー に認定されました。
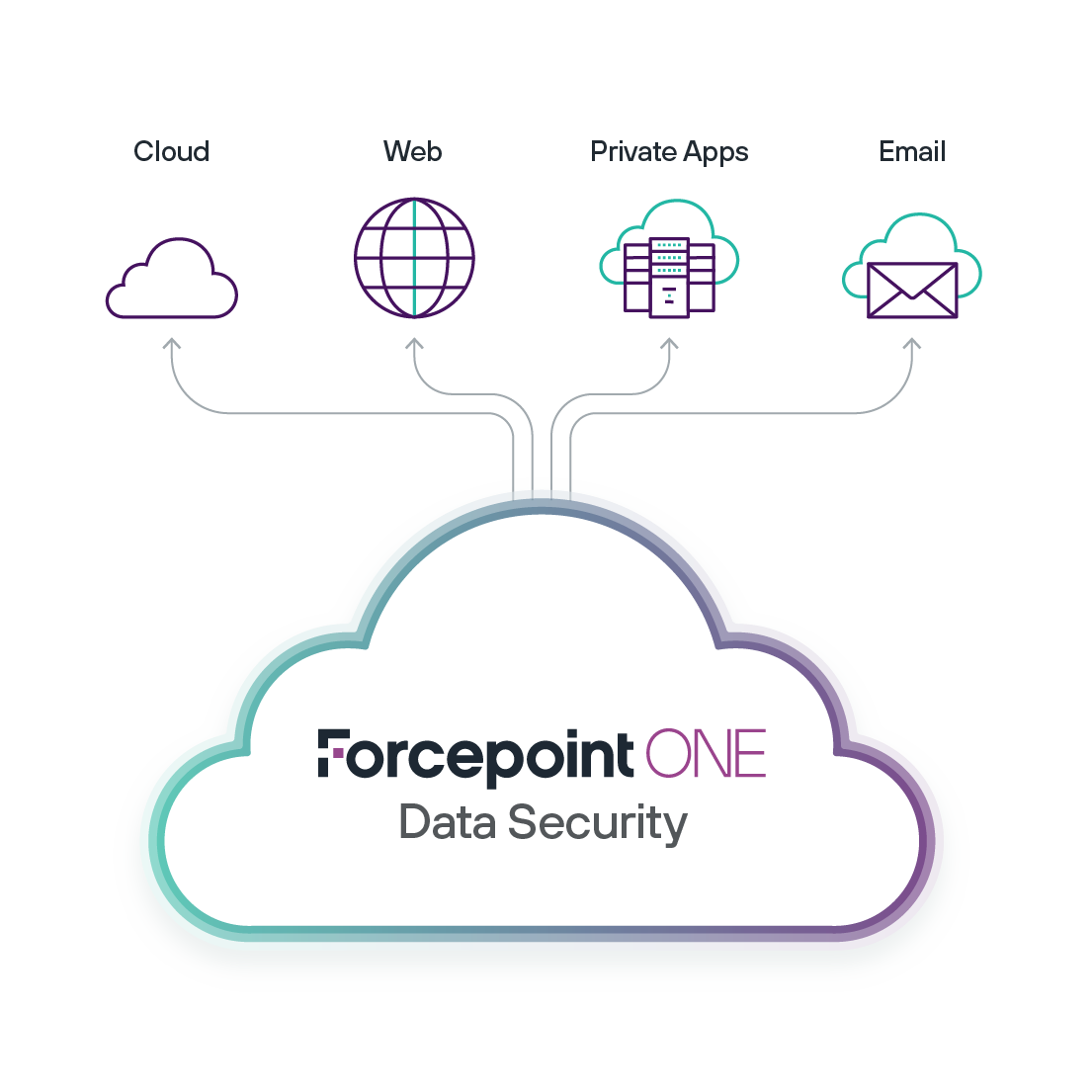
次世代のデータセキュリティ
Forcepointでどこでもデータを保護します。 AIを使用してデータの検出と分類を強化し、ポリシー管理を統合し、リアルタイムでリスクに対応することで、侵害を防ぎコンプライアンス順守を簡素化します。
Enterprise DLP: 使いやすい一元化プラットフォームから、データ保護ポリシーを設定、拡張、自動化します。
Forcepoint Data Visibility: 組織全体の非構造化データを俯瞰的に把握します。
Data Classification: AIと機械学習(ML)を活用し、データ分類の精度と効率性を高めます。

