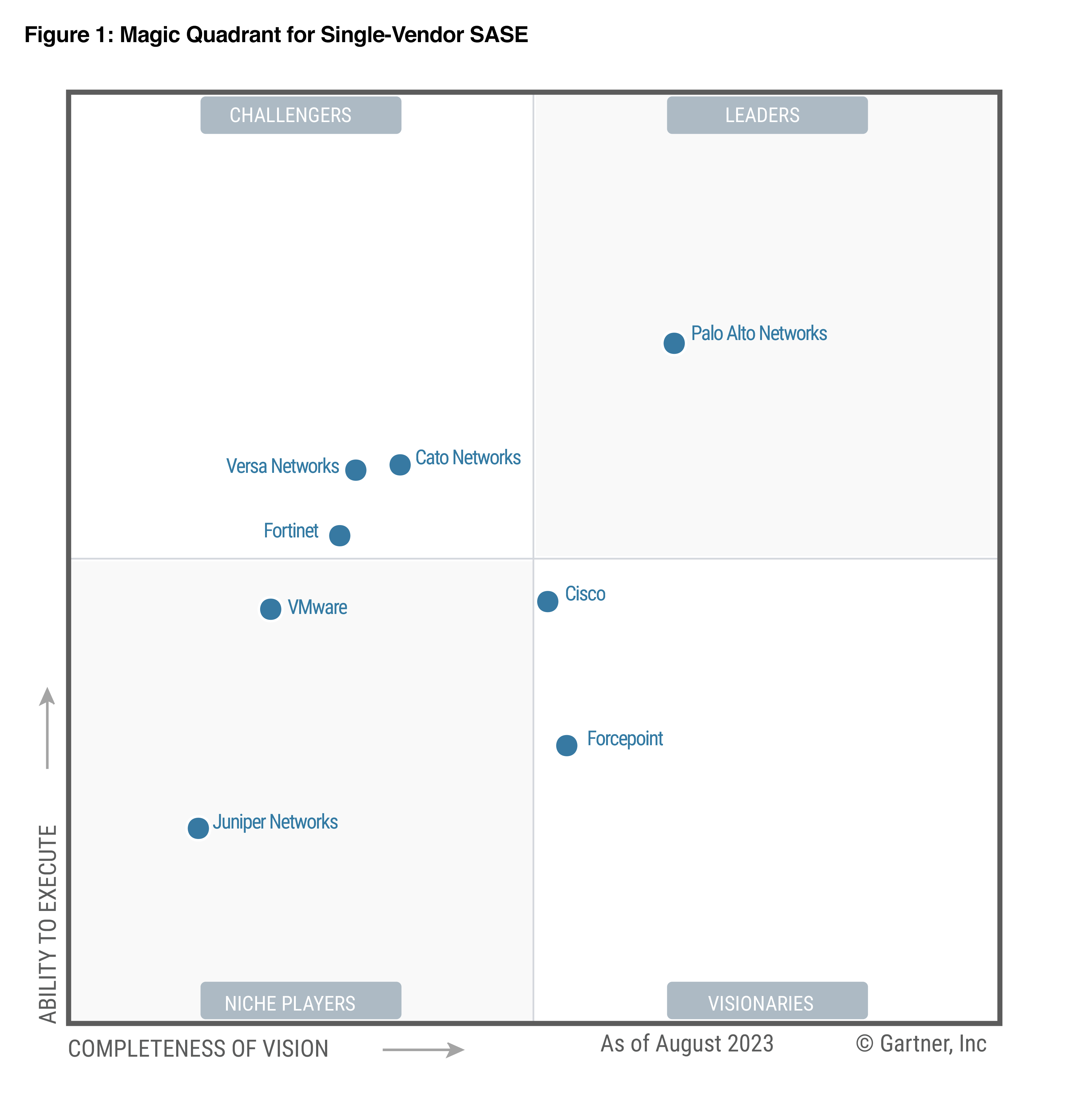
Forcepoint recognized by Gartner® as a Visionary in first-ever Magic Quadrant™ for Single-Vendor SASE
0 min read

Gartner has recognized Forcepoint as a Visionary in its inaugural Magic Quadrant™ for Single-Vendor SASE. In this report, Gartner defines single-vendor secure access service edge (SASE) solutions as ones “that deliver multiple converged-network and security-as-a-service capabilities, such as software-defined WAN, secure web gateway, cloud access security broker, network firewalling and zero trust network access.”* We are honored to be positioned as a Visionary.
As a company, we are doubling down on what we call Data-first SASE and see SASE emerging as one of the dominant architectures for businesses and government agencies.
Here’s how Gartner describes the Magic Quadrant:
"A Gartner Magic Quadrant is a culmination of research in a specific market, giving you a wide-angle view of the relative positions of the market’s competitors.”
To us here at Forcepoint, this Magic Quadrant is a key milestone in the growth of the SASE industry.
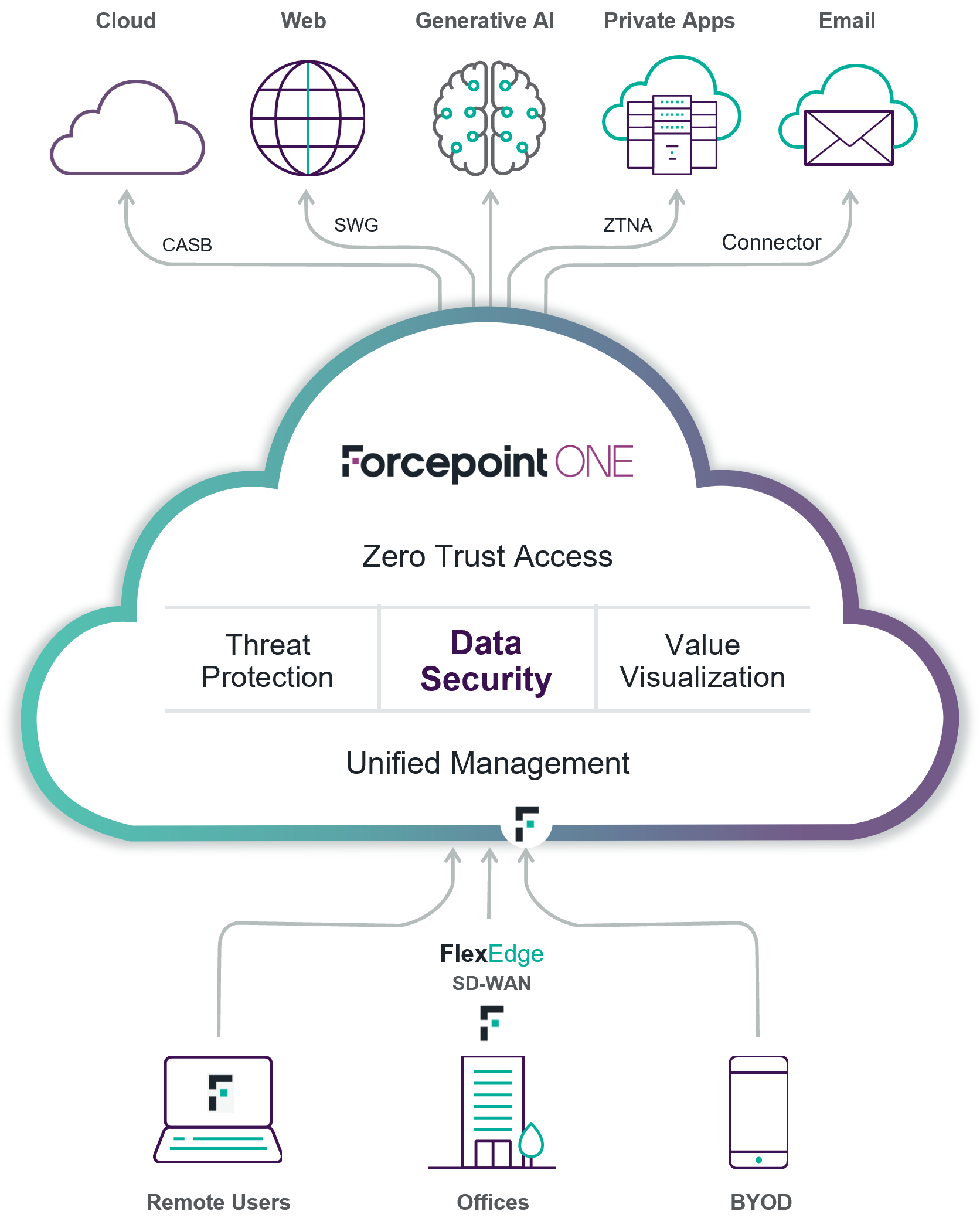
Forcepoint’s Data-first SASE solutions—which combine SD-WAN networking, security service edge (SSE) protections, and our renowned data security technology—connect and protect people and data around the world. Customers choose Forcepoint because we’re able to provide a simpler, more unified way to make remote, office-based, and hybrid workforces more productive, reduce operations costs, stop attackers, and keep control of sensitive data.
While all single-vendor SASE vendors provide the baseline capabilities of SD-WAN connectivity and secure access for cloud, web, and private applications, we see that as just the starting line. Our “Data-first” SASE adds advanced data security so that sensitive information can be protected wherever it is used, stored, and transmitted—from the endpoint through the cloud and everywhere in between.
- Cloud Access Security Broker (CASB)
- Secure Web Gateway (SWG)
- Zero Trust Network Access (ZTNA)
- Software-Defined Wide Area Networking (SD-WAN)
- Data Security Everywhere
From there, we extend the traditional notion of SASE with our unique distributed enforcement architecture that applies centrally managed policies close to users and data wherever they are—in the cloud, at the network edge, and even on the endpoint. This multi-tier approach enables customers to deliver their own best combination of security, cloud/web application performance (esp. in remote locations), and user experience. We’ll be digging into these and other ways that our Forcepoint ONE platform is different in subsequent blogs. And, we have a lot of exciting new innovations coming, so stay tuned!
To read why Gartner has positioned as a Visionary in Single-Vendor SASE, please download the report.
###
*Gartner, Magic Quadrant for Single-Vendor SASE, Andrew Lerner, Jonathan Forest, Neil MacDonald, Nat Smith, Charlie Winckless, 16 August 202 This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from: https://www.forcepoint.com/resources/industry-analyst-reports/2023-gartner-magic-quadrant-single-vendor-sase GARTNER is a registered trademark and service mark, and MAGIC QUADRANT is a registered trademark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings. Gartner research publications consist of the opinions of Gartner's research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.

Jim Fulton
Read more articles by Jim FultonJim Fulton serves as VP Product Marketing & Analyst Relations, focused on SASE, SSE and Zero Trust data security. He has been delivering enterprise access and security products for more than 20 years and holds a degree in Computer Science from MIT.
In the Article
X-Labs
Get insight, analysis & news straight to your inbox

To the Point
Cybersecurity
A Podcast covering latest trends and topics in the world of cybersecurity
Listen Now









