Forcepoint DLP: At A Glance
Data Loss Prevention (DLP) software is synonymous with the name Forcepoint. Analysts regularly recognize Forcepoint DLP as a top pick for its broad security coverage, robust policy management, streamlined compliance auditing and in-depth reporting and forensics. Deployable on-premises, in the cloud or hybrid, and part of a unified data security platform, Forcepoint DLP is built to secure how modern data moves.

80+
Countries’ Regulations Covered

31%
Gain in Operational Efficiency (IDC)

1,800+
Policy and Classifier Templates

15+
Years of Experience

12K+
Global Customers
Secure Data Everywhere with Forcepoint DLP
Simplify data security across AI, cloud, web, email and endpoint with unified, real-time protection—leveraging pre-defined policies and ARIA to deploy the right controls in seconds based on industry, region and live risk signals.

Unify Policy Enforcement
Consolidate policies across devices, channels and regions to minimize operational complexity.

Streamline Global Compliance
Build policies for industry-specific and regional compliance with pre-defined templates and an AI assistant.

Adapt Protection Based on Risk in Real Time
Apply intelligent risk-aware controls based on user behavior and context to stop data loss before it occurs.

Data Security. Everywhere.
Get visibility and control over data, anywhere it goes. Enforce one policy everywhere data goes to prevent loss or misuse in the cloud, on the web, within AI, through email, at the endpoint or in the network.
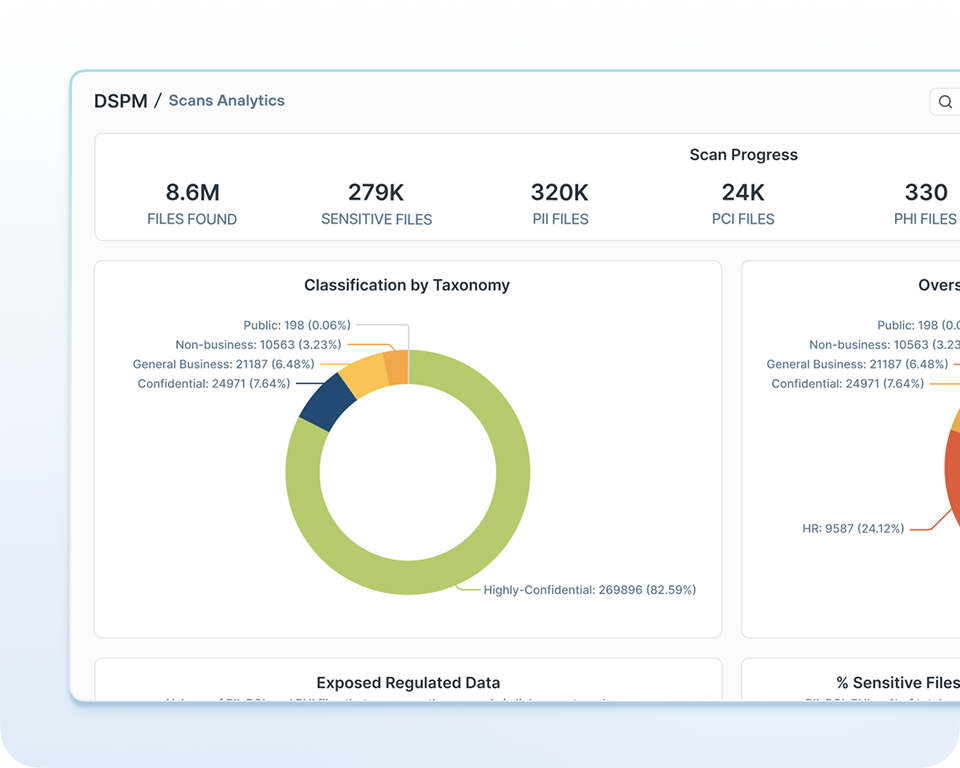
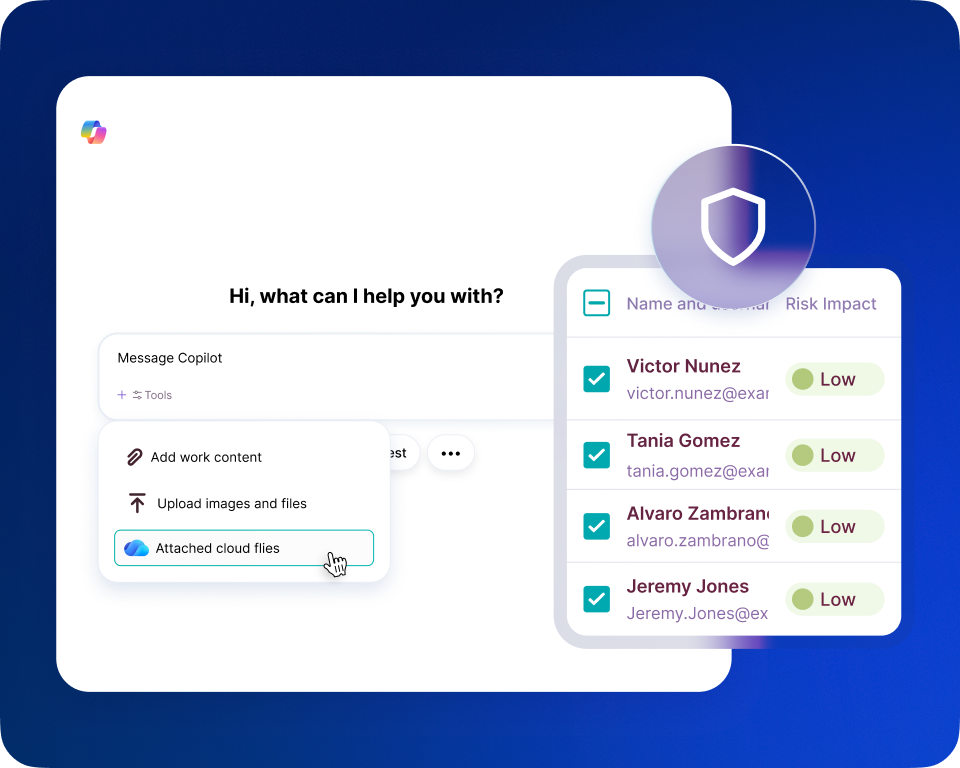
DLP and DSPM: Better Together
Combine AI Mesh-powered discovery and classification of structured and unstructured data with industry-leading DLP enforcement. Identify where sensitive data lives, prioritize risk and automatically apply protection to close the gap between visibility and control.

A Modern, Adaptive Approach
Safely enable AI, protect against insider risk and secure hybrid work with Forcepoint Data Security Cloud – a unified platform that discovers data, understands risk and applies real-time protection with the help of ARIA, an embedded AI assistant.
Why Companies Choose Forcepoint DLP
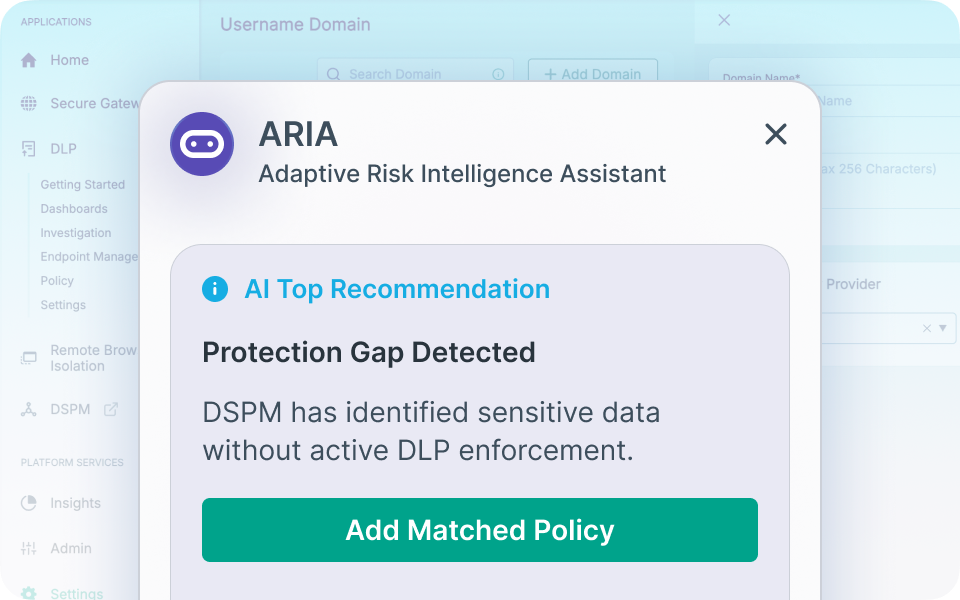
Respond Faster with ARIA
ARIA (Adaptive Risk Intelligence Assistant) is an always-on integrated AI assistant that surfaces insights, recommends protection and deploys policies directly from the chat interface.
Streamline Compliance Worldwide
Streamline policy configuration and management with 1,800+ classifiers and policy templates to identify and secure PII and other types of sensitive data.
Adapt to Risk in Real Time
Contextualize user behavior to forecast risk and automatically adjust policies to prevent security incidents as they occur.
Turn Insight into Action
Surface the most critical, actionable data risk insights with an executive-level dashboard that tracks trends over time and reports regularly to measure performance and demonstrate value.

The Practical Executive's Guide to DLP
Discover how DLP software solutions work with our Practical Executive's Guide to DLP. Find out what DLP excels at, explore the eight critical steps to implementing DLP software and get unique insights on how to generate value quickly from your newly adopted DLP.
Forcepoint DLP Sets the Standard
Forcepoint DLP boasts mature capabilities, an extensive classifier and template library and a modern approach to policy management. Download the chart to see how Forcepoint compares to other DLP vendors.
Data Protection
Forcepoint
100%
Legacy Vendors
52%
Limited DLP Vendors
42%
Prevent Data Loss Where It Matters Most



Prevent users from copying and pasting sensitive information into ChatGPT.
Bolster Microsoft Purview capabilities with enhanced security coverage across the Microsoft 365 family of apps.

Get visibility and control over data that interacts with generative AI applications and AI platforms.
Enforce Compliance and Reduce Risk




Spot signs of malicious intent early and prevent accidental data loss before it becomes an incident.

Classify and enforce compliance for structured and unstructured data across data stores.

Enforce data loss prevention policies in outbound emails to prevent phishing or accidental data loss.
DLP Deployment: In the Cloud or On-Premises
Deploy Forcepoint DLP in the cloud (SaaS) or on premises and get expert support to help you get up and running quickly and realize value faster.

Get up and running fast with simple, hardware-free deployment and no complicated setup.
Unified Protection Across Channels
Prevent data loss across endpoints, SaaS apps, web, and email from a single, intuitive cloud-delivered platform.
Rapid Deployment with No Infrastructure Overhead
Go live quickly without managing appliances, databases or patch cycles—freeing teams from ongoing operational maintenance.
Always Up-to-Date with Automatic OTA Updates
Receive continuous enhancements, policy improvements and security updates automatically, without manual upgrades or downtime.
Global Availability and Enterprise Reliability
Delivered on AWS with 99.99% uptime and resilient regional coverage for always-on protection.
Elastic Scalability for Any Organization
Scale seamlessly to tens or hundreds of thousands of users without adding hardware or redesigning your environment.

Get up and running fast with simple, hardware-free deployment and no complicated setup.
Unified Protection Across Channels
Prevent data loss across endpoints, SaaS apps, web, and email from a single, intuitive cloud-delivered platform.
Rapid Deployment with No Infrastructure Overhead
Go live quickly without managing appliances, databases or patch cycles—freeing teams from ongoing operational maintenance.
Always Up-to-Date with Automatic OTA Updates
Receive continuous enhancements, policy improvements and security updates automatically, without manual upgrades or downtime.
Global Availability and Enterprise Reliability
Delivered on AWS with 99.99% uptime and resilient regional coverage for always-on protection.
Elastic Scalability for Any Organization
Scale seamlessly to tens or hundreds of thousands of users without adding hardware or redesigning your environment.

Complete Control Across All On-Premises Servers
Full Data Sovereignty Within Your Infrastructure
Keep sensitive data entirely within your network, ensuring complete control and security without third-party dependencies.
Ensure Compliance with Local Data Controls
Maintain regulatory compliance by storing and securing data on-prem, where you dictate access, encryption and retention policies.
Performance Designed for Your Environment
Process and enforce DLP policies directly within your network for fast, consistent and predictable performance.




Globaltek Security Protects Critical Digital Assets
Globaltek Security is a long-time partner of Forcepoint and uses DLP to help companies across South America protect their most sensitive data: the digital crown jewels.

Analyst recommended.
User approved.

Forcepoint has been named a Leader in the IDC MarketScape: Worldwide DLP 2025 Vendor Assessment.

Forcepoint earns Leader status in Data Security and Data Loss Prevention, recognized by real customer reviews on G2.
Forcepoint recognized as a Strong Performer in The Forrester Wave™: Data Security Platforms, Q1 2025.
The Latest in Data Loss Prevention
Stay up to date with recent trends, expert insight and analysts analysis for Data Loss Prevention software.
Forcepoint Data Loss Prevention (DLP) Brochure
IDC MarketScape: Worldwide DLP 2025 Vendor Assessment
Gartner®: Implement AI Security in the Generative AI Workflow
Forcepoint DLP: A Full On-Demand Demo
Shut Down Shadow AI Risk
Forcepoint DLP Works Well With
Frequently Asked Questions
What is Data Loss Prevention (DLP)?
Data Loss Prevention (DLP) refers to a set of technologies and strategies designed to prevent sensitive data from being lost, misused or accessed by unauthorized users. Forcepoint DLP protects data in motion, at rest and in use—across endpoints, networks and cloud environments—to ensure your critical information stays protected. Our solution combines advanced analytics and policy enforcement to help stop data breaches.
How does DLP work?
Data Loss Prevention (DLP) tools tag and monitor sensitive data to enforce policies that prevent it from being lost, stolen or misused. DLP scans data at rest (file shares, SharePoint, OneDrive), in motion (email, web, SaaS uploads) and in use (copy/paste, printing, screen capture) to detect regulated data like PII, PHI, PCI and intellectual property, such as images and blueprints. DLP allows organizations to create policies that cover certain types of data, applications or sets of users and limit potentially risky actions that could lead to a data leak or breach. DLP solutions vary in enforcement depending on the severity of the incident, including blocking, quarantining, encrypting or coaching users when policies are violated.
What is a DLP policy?
A DLP policy is a set of conditions that define how sensitive data should be handled within an organization. These policies help prevent unauthorized access, accidental leaks or intentional data exfiltration. With Forcepoint DLP, you can create customizable policies tailored to your business needs, ensuring data is protected across endpoints, networks and cloud environments.
How do DLP policies work?
DLP policies define how data should be handled based on its sensitivity, user roles and regulatory requirements. With Forcepoint, policies are customizable. Our policy engine also helps with maintaining global compliance standards like GDPR and CCPA.
What is DLP software?
DLP software is a security solution that helps organizations prevent the loss of sensitive and valuable information by ensuring that data assets are adequately protected, stored and used.
What is a DLP system and how do they work?
A DLP system is a comprehensive solution that helps prevent data breaches by monitoring, detecting and blocking the unauthorized movement of sensitive data. Forcepoint uses artificial intelligence to discover, classify and monitor structured and unstructured data with highly accurate enforcement that reduces false positives and adapts based on context and user behavior. Forcepoint’s unified approach to policy enforcement ensures consistent protection across all data channels.
What are the capabilities of DLP?
DLP can help your organization stay ahead of evolving threats, ensure regulatory compliance and protect sensitive data effectively and efficiently. Capabilities include policy creation and enforcement, incident response and reporting, compliance and regulatory support and more.
Do organizations need DLP?
Absolutely. If your organization handles Personally Identifiable Information (PII), Protected Health Information (PHI), Payment Card Information (PCI), intellectual property or operates in a BYOD environment, DLP is essential. Forcepoint DLP helps you prevent accidental leaks, insider threats and external attacks—protecting your brand, customers and bottom line.
What is data leakage?
Data leakage is the unauthorized or unintentional transmission of sensitive data outside your organization. This can happen through email, cloud apps, removable media or even printed documents.
What are best practices for implementing DLP?
Forcepoint recommends the following best practices: Identify and Assess: Identify where your sensitive data resides and how it flows. Classify Data: Use automated tools to label data based on sensitivity and compliance needs. Establish Policies: Define clear rules for how data can be accessed, shared and stored. Centralize Oversight: Avoid fragmented DLP efforts by unifying policy management across departments. Train Employees: Educate users on data handling best practices and reinforce with real-time coaching.
What is the difference between network, endpoint and cloud DLP?
When people talk about the different types of DLP, they typically mean network DLP, endpoint DLP and cloud DLP. Network DLP monitors and controls data in motion across the network Endpoint DLP protects data on individual devices Cloud DLP secures data stored in or moving through cloud services such as Microsoft 365 or Google Workspace The main differentiator for Forcepoint DLP is that it unifies all three types of DLP under a single policy engine and console. The same classifiers and policies can be applied across endpoints, on-prem networks and cloud apps, including SaaS and GenAI environments, via Forcepoint CASB API integrations. This gives you consistent rules, incident views and risk scoring across web, email, endpoint and cloud channels, instead of managing three separate DLP systems.
What is endpoint DLP?
Endpoint DLP is Data Loss Prevention software that runs directly on user devices (laptops, desktops, sometimes mobile) to protect data in use and data at rest on the endpoint. It can see and control activities like copy/paste, save-as, printing, screen capture and writing to USB or other removable media - and Forcepoint DLP works even when the device is off the corporate network. Forcepoint DLP is designed specifically to stop data loss that originates at the endpoint, whether accidental or malicious. It monitors real-time traffic and user actions inside applications, applies centrally-defined DLP and discovery policies, and can block, encrypt, quarantine or require justification when users attempt risky actions such as copying sensitive files to external drives or posting them to the web.
What is network DLP?
Network DLP monitors data in motion across your organization’s network. It identifies and blocks risky behavior—whether from insiders or external threats—before data can leave your environment. Forcepoint DLP offers deep visibility and control over data transfers, helping ensure compliance and reduce the risk of breaches.
What is cloud DLP?
Cloud DLP safeguards data stored in and moving through cloud services. Forcepoint DLP can augment and enhance platforms like Google Workspace and Microsoft 365.
Can Forcepoint DLP protect data on cloud applications like Google Workspace and Microsoft 365?
Absolutely. Forcepoint DLP can augment and enhance Google Workspace and Microsoft 365.
What are the key features and functionalities of DLP?
The key features and functionalities of DLP include: Data discovery across on-prem and cloud Data classification and labelling Advanced content inspection Predefined policies and templates for compliance Unified policy based enforcement for all channels Device control and endpoint protection Real-time monitoring and alerting Incident management and investigation Reporting, analytics and audit-ready compliance evidence Integration and deployment flexibility
What are the most common use cases for DLP?
Typical DLP use cases include preventing data breaches and accidental leaks, protecting intellectual property, and meeting regulatory compliance obligations. Common scenarios may include stopping unauthorized uploads of PII/PHI/PCI data, blocking exfiltration of source code and trade secrets and enforcing regional privacy rules like GDPR and CCPA using pre-built policy templates. Modern deployments also focus heavily on cloud, hybrid work and GenAI. Common Forcepoint DLP use cases include securing data in Microsoft 365 and other SaaS apps, controlling data movement from unmanaged/BYOD devices, reducing insider risk by monitoring high-risk user behavior, and inspecting prompts and responses for generative AI tools. Together, these use cases map back to a single goal: keep sensitive data where it belongs without slowing users down.