
The Cyber Mentality with Katie Arrington (Part 1)
Share
Podcast
About This Headline
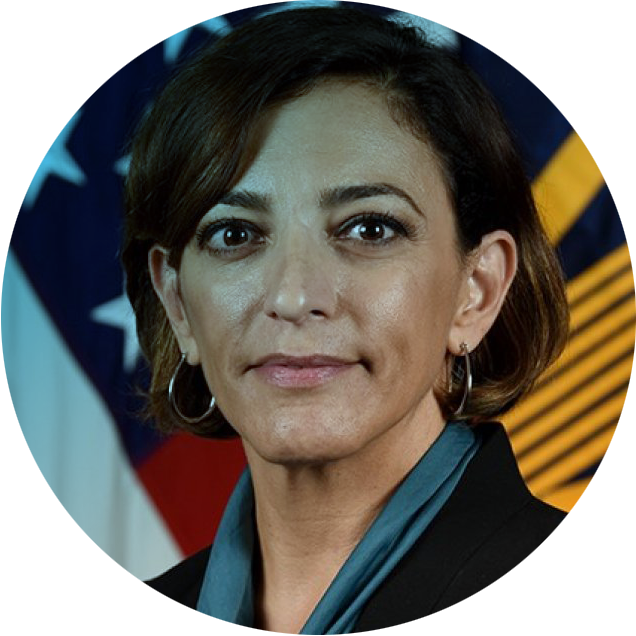
Joining the podcast this week is Katie Arrington the founder of LD Innovations, LLC Cybersecurity and the former Chief Information Security Officer for Acquisition and Sustainment (CISO(A&S)) to the Under Secretary of Defense for Acquisition and Sustainment (USD(A&S)). We cover many interesting themes in our lively discussion including Cybersecurity Maturity Model Certification (CMMC), the impact of a cyber mentality and culture, the National Cybersecurity Strategy, the CHIPS Act, risk reduction strategies, the future of cybersecurity, China’s 100-year plan, Huawei, MITRE, Paperwork Reduction Act, and so much more.
And for movie fans, there are more than a dozen movie references you’ll want to hear. Plus, many book recommendations as well - some you might be surprised to learn!
Podcast
Popular Episodes

35 mins
The War on Data, Cyberspies and AI with Eric O'Neill - Part I
Episode 352
January 6, 2026

22 mins
How AI and Third-Party Risk Are Transforming Healthcare Cybersecurity with Ed Gaudet - Part I
Episode 339
October 1, 2025

24 mins
The Evolving Cyber Threat Landscape in Healthcare: Insights from Fortified Health Security’s Russell Teague - Part I
Episode 332
August 11, 2025

44 mins
From Battlefield to Boardroom: Ricoh Danielson’s Lessons on Cyber Warfare and Digital Forensics
Episode 327
May 27, 2025
Podcast
The Cyber Mentality with Katie Arrington (Part 1)

[0:50] Understanding Cyber Mentality
Rachael: Please, welcome to the podcast, Katie Arrington. She is the Founder of LD Innovations, LLC Cybersecurity and the Former Chief Information Security Officer for Acquisition and Sustainment to the Undersecretary of Defense for Acquisition and Sustainment. Welcome, Katie.
Katie: Well, thank you so much. I'm excited to be here with you both today in this lovely virtual environment that Petko was referring to as we were 10 minutes prior to recording, cracking our own selves up. There's a lot of inside jokes we're not telling you.
Petko: I guess they don't have a need to know. Katie, they don't have a need to know, do they?
Katie: Oh, no. Come on, it's America. No, we're not going to tell them. What's the point? Today, I want to talk about all the fun stuff that people don't really want to say, but it's the truth. Rip the Band-Aid off, at least then we can start healing at some point.
Rachael: Absolutely. Where would you like to start? There are so many pathways for discussion, but I do know one of the hot buttons is Cybersecurity Maturity Model Certification. This is one that keeps circling and circling.
Katie: Well, it's not even a maturity model anymore. Rachael, they broke it. They put me on a timeout in the government. They gave me my administrative leave. By the way, thank you, US taxpayers. I was on a gag order. I couldn't talk for 10 months, but I renovated a house. Thanks. But what they did to that, they took it from a maturity model and they took all the maturity out of the damn model.
The Maturity Model of Cyber Mentality
Katie: The original CMMC was to help mainly small businesses and medium-sized figure out the roadmap, how to get from nothing, zero, to 110, and to do that with restraints. Understanding cybersecurity is something that is a mentality. It is a culture. It's an awareness. It's not a bunch of boxes you check. You have to grow into the maturity of it and that's what the original maturity model did.
Level one was equal to the far, the 17 things you should do no matter where you are. Level two was if you want to start going after contracts that are going to require now CUI, which we'll get into the whole how I regret CUI, getting prepared. Because you'd need to go to your board. You'd need to decide, am I going to do this organically or am I going to outsource this? Do I have enough money? Our government programs are not set up in a fashion that benefits small and medium-sized businesses. People, when I say that, they're like, "Yes, we know." I'm like, "No, you don't know what I'm talking about."
If you get a small business loan and you use it for something other than what it's prescribed to do, that's a no-no. You can't grow. They hold the limit. The fact that the NAICS codes hold you back is scary. The whole thing is you want to grow, but you can't grow because of your NAICS code and you're not going to be prepared. The maturity model was more in helping those small and medium-sized businesses figure out, is it really worth trying to go and become large. Because this is what you're going to have to take on.
How Cyber Mentality Affects Businesses
Katie: I say I'm a unicorn. Way back, because we're not going to talk about how old I am, but when Jesus Christ was around with me, we were friends, I worked as a GS employee in Army daycares. I was a GS employee a bazillion years ago, I wrote Army Regulation 608-10, which is around morale, welfare, and recreation, and ran the daycare programs in Hawaii.
I've been a salesperson, I've been a legislator, I've run my own companies, I've worked at large defense contractors and medium contractors, and I've worked in the government. There isn't an aspect of what we're talking about I don't have some element to say this is why you should do it.
The small businesses are the ones I worry about the most because they don't understand their value. They don't know they're a target, they don't know that the adversary knows that they're easier to get into. They think they're some small, unimportant cog in a big machine that's called the Department of Defense, and they couldn't be any more wrong.
We need to help them to ensure our national security. The bottom line is, if I don't have them going, the Lockheed Martins and the General Dynamics of the World are great, but they sub a tremendous amount of that workout. And that's where the adversary's getting it.
The F-35 and the J-20 in China is not a coincidence, kids. When the F-35 took off, six months later, the J-20 took off. Obama did the right thing as a US President. He said, "We need to not have this happen again. Create a standard." The challenge is, with the CMMC, even what the new National Cybersecurity Strategy, they're still talking about self-attestation.
A Strategy on Cyber Mentality
Katie: But what kills me is we don't allow self-attestation for security. For physical security, we don't allow it. For machine line security, you have to be like ISO 9,000. If you're going to do manufacturing, you get third-party audited constantly. But they don't want to pull that button on cyber, but everything now depends on cyber. I'm still perplexed.
This new National Security Cyber Strategy that came out, it's not a strategy at all. I want to write a strategy. A strategy is, we're going to do all of these things because this is how we're going to get here. I'm sorry, Rachael and Petko. I wrote this op-ed in The Wall Street Journal about the CHIPS Act, and you can rule it and read it. I said, "It's just sending money out into the abyss without a strategy."
But the CHIPS Act, I would've said that any manufacturer that buys a US-made chip gets a tax deduction.
We sell the chips at a lower cost than China is, or Taiwan, as a matter of fact, so that we get more people buying our chips. And then we focus the EPA on new technologies to make the core part of the chip manufacturing that we can't do here. And that's silicone. People don't realize to get the silica, to make the wafer, you have to take sand and pound it to make silicone.
The offset on why China and India make that is because it causes cancer. It's sicalis and it's basically the dust that makes a fine lining around the lungs and eventually, you drown in your own lungs.
[8:35] The Thrill of Cyber Mentality
Katie: Why not take a strategy of, how can we manufacture this? Because our adversaries are doing it, but they don't care about the human condition. Why? There was no strategy behind that CHIPS Act and our National Cybersecurity Strategy isn't a strategy at all. It's nothing more than documenting self-assessments and reactive measures.
For us to win this war, we have to be proactive, not reactive. Spending the money to tell me that an event happened, an incident happened, it's already done and over. Let me spend the money to make sure it doesn't happen.
Petko: I see it like when you go to a restaurant, you have a cook there, someone who operates the kitchen, same as someone who's operating cyber. But they've got health inspectors that go in there and say, "Do you have the right hygiene?" I, personally, when I go to a restaurant, don't want the health inspector and the cook to be the same person. Because then I'm going to be like, "Hmm, I might be in a Third-World country.
Katie: Yes. You're using the example that I actually last week used. It was the restaurant. I live in South Carolina and DHEC inspects our restaurants. If DHEC came and said, "From now on, you have to have your water at 110 degrees, and instead of a hand-washing station every 20 feet, you needed every 10 feet." There would be no amount of money, no crying from the industry.
"This is too hard. We don't want to do it." But in this realm, only in working for the government can you say, "Oh, it's too hard." It's too hard? You're in the wrong damn business. Go find another place to go. You're trusted with national secrets. If it's too hard, go work someplace else.
Fixing the Pieces of Cyber Mentality
Katie: People say, they get on me and they're like, "Oh, we're already struggling for businesses." I said, "It's not the requirements that people get crazy with. It's how long it takes to start a business with the DOD." You've got to get an ATO. You've got to get a PM to sponsor you, You've got to fill out all these documents. You've got to have the cost and accounting systems. The cyber part of it is so minimal compared to all the other stuff, but it's like they're afraid to say it. The valley of death doesn't happen because NIST 171 is a requirement.
The valley of death happens because generally what happens is, we have innovation and capability and we try to throw it on OTAs or SIPRs or STTRs with no acquisition strategy behind it. There's no additional money. It's a one-time deal. It's a one-shot wonder. It is unbelievable to me, in this day and age that we're at, that we haven't put those pieces of the puzzle together yet. That's an easy puzzle to fix, reciprocity on an ATO. If you are a software company and you get an ATO from the Navy, what makes it any damn different playing the Army? And then, why in the hell do you have to pay to go and have it all done again?
Petko: Because I can.
Rachael: I love it.
Petko: Right?
Rachael: I love it.
Katie: Entitled to.
Petko: Katie, it's all because I can.
Katie: The thing is, the DAAs, the people that actually sign the ATOs, they're assuming risk. But if you have a standard amount of requirements for the building capability and you test it once, every network is different.
Precautions and Measures Needed for Cyber Mentality
Katie: There's got to be some assumed risk no matter what, but a provisional ATO, let it go into the field and protect it. A bazillion years ago, I worked at a company called SCRA, South Carolina Regional Alliance. I begged them to build basically a cyber range that was DOD equivalent. So the companies that were developing software could go and test on this cyber mentality range and get a provisional. They've been tested for X, Y, and Z and cut down on the government's expense on having to do it.
Because it shouldn't be the government's expense. You should come and say, "Here's my validated testing." They wouldn't do it. Everybody says it's so hard. It's really not, it's just people have to change. It's like, who moved my cheese? People have to be open to risk, which should not be a bad four-letter word, the connotation is risk is a bad thing. It's not. Risk is something we have every day. You just have to have risk-reduction strategies to be successful. Rachael, when you get up in the morning and you go to get in your car and go to work, do you put your seatbelt on?
Rachael: I do, Katie.
Katie: Is that a risk? Now, are you terrified to drive your car because the likelihood you could get killed is bad?
Rachael: No, it's a risk I take. That's right.
Katie: You just need to know what precautions and measures you need to do before you get into that vehicle of death.
Rachael: Exactly.
We Don’t Talk About Cyber Mentality
Katie: It, to me, is mind-boggling when you think about the world and the adversaries that are piled up against us. We now have a community of interest that have all said, "We don't like America. We're going to change the currency. We're going to change the global economy." Iran, Russia, China, India, Venezuela, and Brazil. And we are arguing publicly about how hard it is.
This is the thing, the one that just makes me giggle. You have all these countries that have come together to say, now, think about this. Both of you, sit back. Everybody listening, sit back.
All of these countries, in less than a year, have come together and figured out how to do a currency that they all can agree on, all the terms. Remember, Brexit went on for how many years before the UK dipped out? These guys came in one year in bricks and figured it all out. You've got to think of all the different disparity challenges there is for that. And then you have us, companies.
We have the leaders of the National Defense Industry Association and the Aeronautics Industry Association go and testify before Congress about how hard the NIST 171 is.
Every time a company comes up in an event and they say it's hard, it's like the adversary just sits there and like, "Did they just say that was hard? Oh, okay. What's the company name again? I'm going in after them." Remember when I used to talk publicly? Like, "Don't talk about Fight Club? We don't talk about Fight Club."
I just am struggling, the struggle bus, and I am trying to still motivate people to do it because there's nothing in this world that is not, we'll go back to one of my old jokes.
[16:21] The Risks that Come with Cyber Mentality
Katie: When Al Gore created the internet, he didn't know what he was creating. I'm 52 years old, and I know that when I got my first RAZR flip phone, I didn't understand the risk associated with it. I didn't think at whatever age I was, I know I had two kids and I did get the pink RAZR flip bone. I had my Noritake one. Do you remember? But when we first started to text, it was like you had to press A several times on the keypad to get the letter you wanted.
Rachael: So much work.
Petko: T9.
Rachael: Yes.
Katie: But I didn't. As human beings, and as we evolve, we learn. What we didn't understand then was, if you can take it with you and it can find you anywhere, they can find you anywhere.
Rachael: Exactly.
Katie: That risk didn't dawn on me, and that's why this whole conversation about CUI has gotten out of control. I think if I could go back in time, I really wish we would take that whole classification out. I think it's doing more harm than good, and here's my thought. Because I am the worst offender in everything. I don't speak from a place of I'm holier than now.
I have literally made every mistake in the book. I've learned from it. I learned you fail early, fail often and you get up. When I was at PM back in the day, I was running a program in Northern California, Cal ISO. And this is when they were first saying that Northern California had to present 20% of your energy from a natural green resource. I was working on the transponder technology, how to regulate that and to make it known within the grid system.
The Importance of Cyber Mentality in Security
Katie: At the same time, I was also a PM over weather surveillance radar WSR-88 Doppler. Of all the Dopplers in the country, the company that I worked for was the only one that could build or repair them. I was over the watershed for the East Coast. Now, each of those programs, none of those programs were technically classified. But if the adversary got into my laptop, man, they got a lot of info.
That's what I wish companies would start thinking about and saying, "Oh, I don't need to get CMMC certified and the NIST doesn't apply to me." If you value your business, it sure hell does. Because on your network, now whether you think you are carrying classified or unclassified, or CUI. Your employee's information on your network, your banking information on your network, your intellectual property on your network, everything that is in your network is CUI.
You should protect it. There should be nobody working on a CMMC level one, not even the landscaper who mows the lawns at the bases. Because I've said to people a thousand times, "How do you think they calculate the bid?" They give them the AutoCAD layout of the military base. They give them all of the information about where the critical infrastructure is, where the electricity is, and where the security is. We used to play Six Degrees of Kevin Bacon. Tell me, somebody, in the DOD that is so unconnected or disconnected from another entity within the DOD that you shouldn't be. And it's not just DOD.
Society’s Dependence on Cyber Mentality
Katie: You go into your doctor's office and for any of the health information exchanges, the HIEs, and for a doctor, you have to join one. The hospitals have them. Do you think that doctor just walks in and says, "Hey, I'm going to use Epic, Cerner, Accenture, whatever." And they don't come and do a cyber audit of that doctor's office and do extensive training on how to use the systems and be involved in it, and send them pre-programmed iPads, laptops, et cetera?
Because they understand the value of what they're doing. It just floors me that the Department of Defense is like, "It's too hard." The financial system, it isn't too hard. The health system, it's not too hard. Aviation, it's not too hard.
They're looking for money. Unless as a group, the entirety, look at the authorizers and the appropriators and the authors of the NDAA and say, "This is the sins of our past, 2015. I can't go back and redo time. How can I make it better?" I lobbied for Congress to give $10 billion a year to the DOD over the course of five years.
" I was, "Let's stop talking about CUI. Let's stop talking about levels one, two, or three. Because it's for the taxpayer. Ultimately, everything that's built, it's your tax dollars doing it. Today, quick, add this up, we're losing $200 million a day in the DOD, in the defense industrial base, in IP loss, ransomware, and straight-up theft. $200 million a day.
Rachael: A day?
Katie: A day.
Petko: 73 billion a year?
Keeping Cyber Mentality Secure Is Everyone's Duty
Katie: In a year. We lose, globally, $6 trillion a year in cyber attacks, and espionage. When I said to Congress this 10 billion over five years, get everybody the level set, a rising tide will raise all boats, and I'm one voice. I can only do so much. If we care, we're losing more than we will ever spend on it. It's sadly turned political, and this should be a bipartisan issue.
This is not an issue that should be one or another. It shouldn't be large businesses or small businesses complaining. It's everybody, and that's why I've taken a different approach.
Now, I just talk to the people that are with contracts, under contracts with the government, and saying, "So when do you expect your false claims to be levied? Because now, the federal government says anybody can level them. I know all the secrets so, who wants to be the first one I go after and say this is what you've reported?" Because when we started doing the SPR scores, guys, John Ellis, bless his heart.
One of the best human beings, and why he is not an SES is beyond me over at DCMA. And Dave Bassett, General Bassett.
I can't say enough about those two folks because General Bassett is like, "What are you all waiting for?" He only has so many people that can go and do inspections and write CARs, corrective action reports. He only has so many people that can do it.
[24:29] Protecting Years of Cyber Data
Katie: But when you, as a US taxpayer, look at all the weapons that China has stolen from us, the R&D, it's the stuff that you don't think about. Building a Navy ship or a boat is 90 years of research and development that the adversary stole. 90 years easy.
Rachael: Wow, that's crazy.
Katie: The F-35, billions of dollars. In the Navy, think about this, the paint that they use, it's not like they just came out and they figured out, "Oh, we'll use this paint to paint this." It was years of trial and error and what was held up the longest. We finally figured out the right chemical compounds and it's a very specific mixture, and how it's applied and when it's applied. Your tax dollars paid for that. Don't you want to protect it?
It's everything that we're doing. This is where, and I'd love your guys' thoughts on this one, I don't want to become like my enemy to win the war. I don't want to give up what makes this great republic. People can't see me because we're on a podcast, but literally, I'm sitting on it. I literally carry. And Rachael, you can see it, right?
Rachael: I love it. Uh-huh. Yes.
Katie: I carry the Constitution everywhere I go.
Rachael: The Constitution.
Katie: Right. It's because this separates us from the rest of the world. This. You do not have lines of people waiting or running across open borders in any other country in the entire world as you do in the United States, and there's a reason why.
The Algorithm of What You Should Become
Katie: Our adversaries are using something called lawfare, and anybody listening to the podcast, there's a great book on it, but it's basically how you use a country's legal system against them. It is lawfare.
What was it, two weeks ago? No, last week, the CEO of TikTok testifies in front of Congress. And the thing that should have gotten every American out of their chair and over to their kid's cell phone was a statement that the CEO made. I sent a whole lot of questions to that committee because I know. They asked him, "Do your children use
TikTok?" And his response was, "No, they're not 13. It's illegal in China for a child under 13 to have a cell phone." Why?
Rachael: Interesting.
Katie: Or to be on TikTok. Because they do social-emotional scoring on a child. Every child in China is born with a score. Your parents, where you live, your family history, what province, you're given a score. And then, as you go through school, they start figuring out what you would be best at doing. And when you turn 13, you're allowed a cell phone. But because they've done the social-emotional scoring on you, they only send you the algorithms of what they want you to do.
Doing the Smart Easy Stuff
Katie: If you're a kid in China and they want you to become an engineer, the TikTok algorithm that you see, the only ones you see are about all these amazing engineering programs and how awesome it would be to be an engineer. They brainwash you into believing that's what you should do. Our algorithm, and he says this.
Petko: Does the same, right? Right, Katie? It does the same.
Katie: It does the same, but ours is stupidity, like eating a pod that you put into the dishwasher. You need to be told dish detergent's not good for you to eat.
Rachael: That is crazy.
Katie: That's why it's so insane to me where we are as a country and all that is happening to us that we could get away from just by doing the simple stuff. Just by doing the smart, easy stuff.
Rachael: We are going to pause today's episode right here. We are having so much fun speaking with Katie Arrington that we're going to bring her back next week for part two. You don't want to miss it. Be sure to subscribe so you can get a fresh episode next week right in your inbox or on your favorite streaming platform. So until next time, be safe.
About Our Guest

Katherine “Katie” Arrington is a former member of the Senior Executive Serves and served as the Chief Information Security Officer for Acquisition and Sustainment (CISO(A&S)) to the Under Secretary of Defense for Acquisition and Sustainment (USD(A&S)). In this position, she served as the central hub and integrator within the Office of the Under Secretary of Defense for Acquisition and Sustainment. (OUSD(A&S)) to align acquisition and sustainment cyber strategy and efforts to enhance cyber security within the Defense Industrial Base.
She led efforts that help ensure a secure Defense Supply Chain through the implementation of Trusted Capital vendors and Supply Chain Risk Management principles, enhanced defense industrial Base security and resilience, and establish a common cyber security standard within Departmental acquisition efforts. She also spearhead the CMMC program and served as an information security officer in the U.S. Department of Defense during the Trump Administration.
Arrington was also the state representative for South Carolina’s 94th district from 2016 to 2018, briefly serving with Mace. Prior to entering politics, Arrington worked in defense contracting and real estate development. She is currently the owner of LD Innovations, LLC Cybersecurity. Arrington continues to use her platform to advocate for proper national security measures and inform the public on critical news. She attended Canisius College and Walden University
Listen and subscribe on your favorite platform