If you're not prepared for GDPR, you're not alone
According to the IAPP-EY Annual Privacy Governance Report 2018,
only 44% of companies say they are fully compliant
Organizations spend an average of $3M getting to GDPR compliance.*
GDPR requires data controllers to report rapidly - within 72 hours of data breach discovery.
If an EU resident requests to be forgotten, you must eliminate all individual records that you process or control.**

GDPR Compliance Challenges
Unsure of personal data locations
It can be challenging to locate personal data amongst your organization’s vast sets of data.
Data is dynamic
Data isn't static; it flows through your supply chain, network, endpoints, and into the cloud.
Data classification is not enough
Traditional data classification cannot guarantee visibility or control to all data regulated by GDPR.
Inventory all personal data that you control or process
Going beyond data classification to uncover unknown personal data is key to achieving compliance. Forcepoint GDPR solutions inventory personal data, providing insight on who accessed it and when. We can help you get started today.
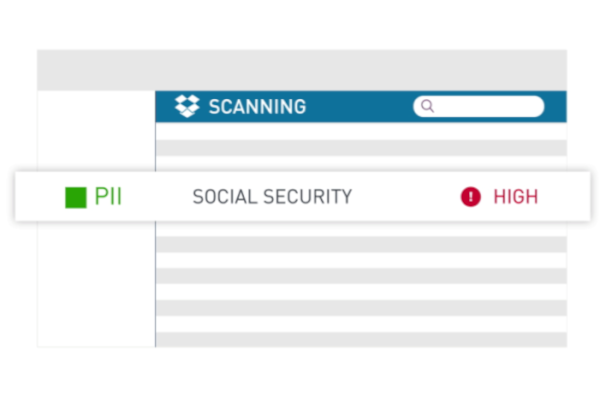
Discover where your data is with our pre-defined GDPR policies that can locate all personal data on premises, on your network, and on endpoint devices.
Uncover personal data in hard-to-find places, with OCR capabilities to detect text within images, and identify it as personal data.
Identify personal data not labelled by your existing data classification system, enable broad visibility.

Map, manage, and control personal data flows - wherever they are
Data is constantly moving—not only within your organization, but in and out of environments and networks you don't control, such as your partners and suppliers. A comprehensive strategy will enable you to:
Empower your personal data management strategy with tools that manage data movement across endpoints, as well as to and from cloud-based applications.
Define and adjust policies for your dynamic environment.
Control and encrypt your data when it moves externally
Respond and recover from incidents
GDPR requires organizations to react swiftly when personal data breaches occur. Our offerings enable you to focus on rapid and comprehensive remediation. Forcepoint GDPR solutions can:
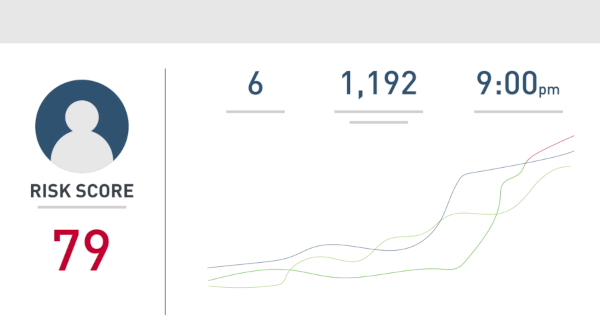
Review large data sets, leveraging all structured and unstructured data sources in your organization.
Provide visibility into events and timelines involved in a data breach.
Analyze and investigate activities and individuals putting the organization at risk.
Learn More About GDPR Compliance
* IAPP-EY Annual Privacy Governance Report 2018
** Unless in accordance with law




