
12K+ customers couldn't be wrong










































Protect the network from advanced threats.
Forcepoint Next-Generation Firewall delivers industry-leading network security at scale. Deploy from anywhere in the world through the Secure Management Console (SMC) and unify policy management, incident response and reporting under one console.
Explore Forcepoint NGFW Models

3500 Series
Ideal for large enterprises, campus networks and data centers.
Up to 66 interfaces
Firewall throughput up to 600 Gbps
IPS & NGFW throughput up to 140 Gbps

3400 Series
Ideal for campus networks and data centers.
Up to 67 interfaces
Firewall throughput up to 200-300 Gbps
IPS NGFW throughput up to 15-35 Gbps

2300 Series
Ideal for mid-sized and large offices.
Up to 30 interfaces
Firewall throughput up to 145 Gbps
IPS NGFW throughput up to 37 Gbps

2200 Series
Ideal for mid-sized and large offices.
Up to 25 interfaces
Firewall throughput up to 120 Gbps
IPS NGFW throughput up to 13.5 Gbps

1200 Series
Ideal for mid-sized and large offices.
Up to 17 interfaces
Firewall throughput up to 65 Gbps
IPS NGFW throughput up to 5 Gbps

350 Series
Ideal for remote sites and branch offices (desktop design).
Up to 13 interfaces
Firewall throughput 40 Gbps
IPS NGFW throughput 2 Gbps (N352) or 4.1 Gbps (N355)
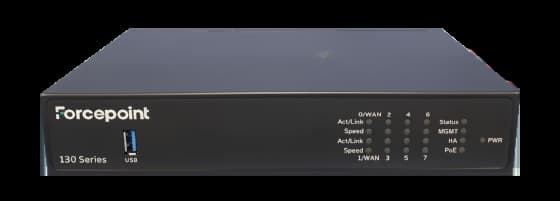
130 Series
Ideal for remote offices, branches and stores.
Up to 8 interfaces
Firewall throughput 8 Gbps
IPS NGFW throughput 1,600 Mbps

120 Series
Ideal for brick-and-mortar locations and branch offices.
Up to 8 interfaces
Firewall throughput 4 Gbps
IPS NGFW throughput 450 Mbps

60 Series
Ideal for remote offices, branches and brick-and-mortar locations.
Up to 4 interfaces
Firewall throughput 4 Gbps
IPS NGFW throughput 700 Mbps
Forcepoint Next Generation Firewall (NGFW) Datasheet
Read more about Forcepoint NGFW specifications, including platforms, features, threat protection and integrated SD-WAN functionality.
Cloud Images:
- Unified Forcepoint NGFW software
- Amazon Web Services (AWS)
- Microsoft Azure Solutions
- Secures both north-south communication in/out of cloud and SDN east-west traffic
Virtual Appliances:
- Unified Forcepoint NGFW software
- Available for KVM and VMware ESXi and NSX
- Scales to 64 CPUs
- Automates network microsegmentation
- Can be clustered with physical firewalls


Global Network
20+
Countries
45+
Cluster Nodes
Clustering In a Way No One Else Can Do
Christian Keller, CISO at Huber + Suhner, lists reliability, clustering and ability to navigate global compliance requirements among the top benefits of Forcepoint NGFW.
Why Forcepoint NGFW?
Centralize Management with the SMC
Manage network policies, identify and prevent security incidents in real time, and review the performance of appliances and applications through the SMC.
Protect the Network from the Unknown
Pair industry-leading security with trusted network management through zero trust network access controls, Advanced Malware Detection and Protection (AMDP), intrusion prevention and other controls.
Deploy Appliances from Anywhere
Automate, orchestrate and scale the network anywhere in the world with a broad range of physical and virtual appliance.
Customize and Scale with Modular Network Interfaces
High-end, rack-mounted Forcepoint NGFW appliances accept a range of extensible network interfaces, providing flexibility and adaptability for new network infrastructure.
Balance Network Demands and Prevent Downtime
Build strong network resiliency and scalability through load balance clustering and multi-ISP support load balancing with application-aware routing, including the ability to update software and appliances without service breaks.
Why Customers Choose Forcepoint NGFW
Why Customers Choose Forcepoint NGFW
"Our costs - both for the project and maintenance - are going down because we don't need resources locally, we have centralized everything. If we want new service on a train, we define the policy then give the hardware to the operator, who installs it."
VR Group
Frequently Asked Questions
What is a firewall?
A firewall is a network security device that monitors incoming and outgoing network traffic and permits or blocks data packets based on a set of security rules. The purpose of a firewall is to establish a barrier between your internal network and incoming traffic from external sources (such as the internet) in order to block malicious traffic like viruses and hackers.
How does a firewall work?
Firewalls guard traffic at a computer’s entry point, called ports, which is where information is exchanged with external devices. Firewalls carefully analyze incoming traffic based on pre-established rules and filter traffic coming from unsecured or suspicious sources.
Why are firewalls important for organizations?
Firewalls help protect your network from threats. Forcepoint NGFW delivers industry-leading network security at scale. Deploy from anywhere in the world through the Secure Management Console (SMC) and unify policy management, incident response and reporting under one console.
What are features of a NGFW?
Features of a NGFW include:
Deep packet inspection: NGFWs inspect data at each of the four TCP/IP communication layers – application, transport, IP/network and hardware/datalink. This enables next-gen firewalls to operate with application awareness, an understanding about which applications are receiving and generating traffic and the types of user and application behavior that may be expected in those traffic patterns.
Automation and orchestration: NGFWs enable automatic deployment and instant updates that reduce the administrative burden on IT teams.
Intrusion detection/prevention: Next-gen firewalls detect and prevent cyberattacks by inspecting traffic at higher TCP/IP layers and monitoring for potential attacks based on anomalous behavior or specific attack signatures.
Application control: NGFWs provide real-time visibility into users and data interacting with applications, enabling high-risk applications to be identified and blocked when necessary.
Distributed Denial-of-Service (DDoS) protection: NGFWs are stateful technologies that check the characteristics of each connection to detect the many different types of illegitimate requests that may comprise a DDoS attack.
Unified threat management (UTM): NGFW solutions offer comprehensive security services that include antivirus, content filtering, malware infection and mitigation.
What are the types of firewalls?
Firewalls can either be software or hardware, though it’s best to have both. A software firewall is a program installed on each computer and regulates traffic through port numbers and applications, while a physical firewall is a piece of equipment installed between your network and gateway. Below are some specific types of firewalls:
Packet-Filtering Firewalls: Packet-filtering firewalls, the most common type of firewall, examine packets and prohibit them from passing through if they don’t match an established security rule set. This type of firewall checks the packet’s source and destination IP addresses. If packets match those of an “allowed” rule on the firewall, then it is trusted to enter the network.
Next-Generation Firewalls: Next-Generation Firewalls combine traditional firewall technology with additional functionality, such as encrypted traffic inspection, intrusion prevention systems, anti-virus and more. Most notably, it includes deep packet inspection (DPI). While basic firewalls only look at packet headers, deep packet inspection examines the data within the packet itself, enabling users to more effectively identify, categorize or stop packets with malicious data.
Proxy Firewalls: Proxy firewalls filter network traffic at the application level. Unlike basic firewalls, the proxy acts an intermediary between two end systems. The client must send a request to the firewall, where it is then evaluated against a set of security rules and then permitted or blocked. Most notably, proxy firewalls monitor traffic for layer 7 protocols such as HTTP and FTP and use both stateful and deep packet inspection to detect malicious traffic.
Network Address Translation (NAT) Firewalls: NAT firewalls allow multiple devices with independent network addresses to connect to the internet using a single IP address, keeping individual IP addresses hidden. As a result, attackers scanning a network for IP addresses can't capture specific details, providing greater security against attacks. NAT firewalls are similar to proxy firewalls in that they act as an intermediary between a group of computers and outside traffic.
Stateful Multilayer Inspection (SMLI) Firewalls: SMLI firewalls filter packets at the network, transport and application layers, comparing them against known trusted packets. Like NGFW firewalls, SMLI also examine the entire packet and only allow them to pass if they pass each layer individually. These firewalls examine packets to determine the state of the communication (thus the name) to ensure all initiated communication is only taking place with trusted sources.
What is an SD-WAN firewall?
An SD-WAN firewall enhances cybersecurity by monitoring and managing inbound and outbound network traffic within a Software-defined Wide Area Network (SD-WAN).
What is network security?
Network security is a combination of rules and configurations that help protect computer networks and data.
How does network security work?
There are many layers to consider when addressing network security across an organization. Attacks can happen at any layer in the network security layers model, so your network security hardware, software and policies must be designed to address each area. Network security typically consists of three different controls: physical, technical and administrative.
What are types of network security?
Network Access Control
Antivirus and Antimalware Software
Firewall Protection
Virtual Private Networks
What is a network attack?
A network attack is an unauthorized action on digital assets within an organizational network. Malicious parties usually execute network attacks to alter, destroy or steal private data. Perpetrators in network attacks tend to target network perimeters to gain access to internal systems.
What are the types of network attacks?
DDoS: DDoS attacks involve deploying sprawling networks of botnets, which are malware-compromised devices linked to the internet. These bombard and overwhelm enterprise servers with high volumes of fraudulent traffic. Malicious attackers may target time-sensitive data, such as that belonging to healthcare institutions, interrupting access to vital patient database records.
Man-in-the-Middle Attacks (MITM): MITM network attacks occur when malicious parties intercept traffic conveyed between networks and external data sources or within a network. In most cases, hackers achieve MITM attacks via weak security protocols. These enable hackers to convey themselves as a relay or proxy account and manipulate data in real-time transactions.
Unauthorized Access: Unauthorized access refers to network attacks where malicious parties gain access to enterprise assets without seeking permission.
SQL Injection: Unmoderated user data inputs could place organizational networks at risk of SQL injection attacks. Under the network attack method, external parties manipulate forms by submitting malicious codes in place of expected data values. They compromise the network and access sensitive data such as user passwords. There are various SQL injection types, such as examining databases to retrieve details on their version and structure and subverting logic on the application layer, disrupting its logic sequences and function.
What are examples of network attacks?
Social Engineering: Social engineering involves elaborate techniques in deception and trickery techniques, such as phishing, that leverage users’ trust and emotions to gain access to their private data.
Advanced Persistent Threats (APT): Some network attacks may involve APTs from a team of expert hackers. APT parties will prepare and deploy a complex cyber-attacks program. This exploits multiple network vulnerabilities while remaining undetected by network security measures such as firewalls and antivirus software.
Ransomware: In ransomware attacks, malicious parties encrypt data access channels while withholding decryption keys, a model that enables hackers to extort affected organizations.
What is packet loss?
When accessing the internet or any network, small units of data called packets are sent and received. Packet loss is when one or more of these packets fails to reach its intended destination. For users, packet loss manifests itself in the form of network disruption, slow service and even total loss of network connectivity.
What are causes of packet loss?
Network Congestion
Software Bugs
Problems with Network Hardware
Security Threats
What is Defense in Depth (DiD)?
DiD is a cybersecurity approach with a series of defensive mechanisms that are layered to protect valuable data and information.
What is the Open Systems Interconnection (OSI) Model?
The OSI Model is a conceptual framework used to describe the functions of a networking system. The OSI model characterizes computing functions into a universal set of rules and requirements in order to support interoperability between different products and software. In the OSI reference model, the communications between a computing system are split into seven different abstraction layers: Physical, Data Link, Network, Transport, Session, Presentation and Application.
What is an Intrusion Prevention System (IPS)?
An IPS is a form of network security that works to detect and prevent identified threats. An IPS is typically configured to use a number of different approaches to protect the network from unauthorized access. These include:
Signature-Based: The signature-based approach uses predefined signatures of well-known network threats. When an attack is initiated that matches one of these signatures or patterns, the system takes necessary action.
Anomaly-Based: The anomaly-based approach monitors for any abnormal or unexpected behavior on the network. If an anomaly is detected, the system blocks access to the target host immediately.
Policy-Based: This approach requires administrators to configure security policies according to organizational security policies and the network infrastructure. When an activity occurs that violates a security policy, an alert is triggered and sent to the system administrators.
How do Intrusion Prevention Systems Work?
Intrusion prevention systems work by scanning all network traffic. There are a number of different threats that an IPS is designed to prevent, including:
- Denial of Service (DoS) attack
- Distributed Denial of Service (DDoS) attack
- Various types of exploits
- Worms
- Viruses
What is branch networking?
Branch networking refers to the elements used to distribute information to, from and among remote sites, stores, branch offices and data centers.
