X-Labs
Get insight, analysis & news straight to your inbox

How to Architect an Effective Insider Risk Program

Tim Herr
January 14, 2026

Essential Guide to Insider Risk: Detect, Prevent and Respond

Lionel Menchaca
January 13, 2026

9 Top AI Cloud Security Solutions for Guarding Sensitive Data

Tim Herr
January 10, 2026

AI Security Best Practices: How to Protect Sensitive Data in GenAI Tools

Lionel Menchaca
January 8, 2026

How Does Forcepoint DSPM Compare to Varonis?

Tim Herr
January 6, 2026

X-Labs
2025 Holiday Scams: Docusign Phishing Meets Loan Spam


Mayur Sewani & Ben Gibney
December 22, 2025

PII Data Classification: Main Data Types and Tools to Catalog Them

Lionel Menchaca
December 21, 2025
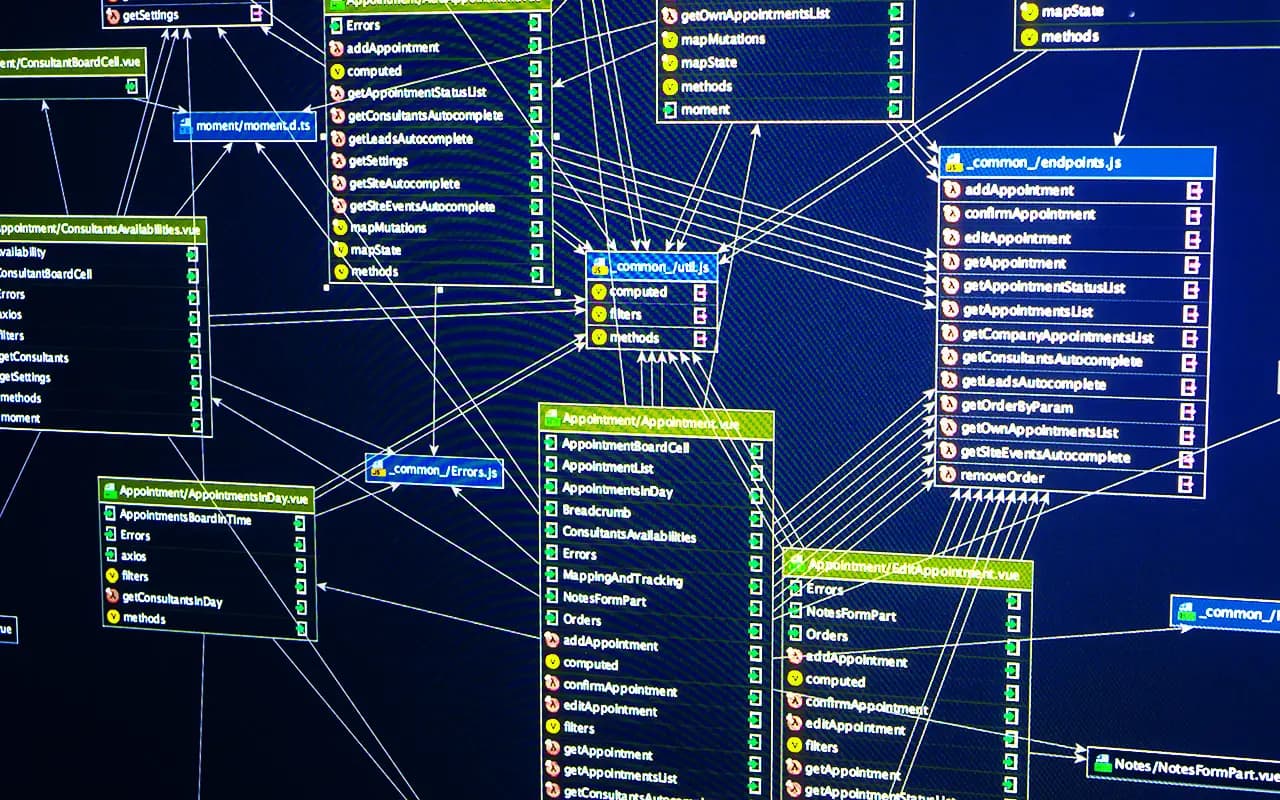
SQL Data Discovery and Classification for Database Security

Tim Herr
December 20, 2025

6 Best PII Data Discovery Tools to Ensure Compliance

Lionel Menchaca
December 19, 2025

PCI Data Discovery: Strategies and Tools for Compliance

Tim Herr
December 19, 2025

Structured vs. Unstructured Data: Differences, Use Cases and Best Practices

Tim Herr
December 18, 2025