12K+ customers couldn't be wrong










































Apply industry-leading data security to your emails in minutes.
Get agentless control over outbound emails and prevent exfiltration where it's needed most. Forcepoint DLP for Email delivers industry-leading control over the top vector for data theft.
Why Forcepoint DLP for Email
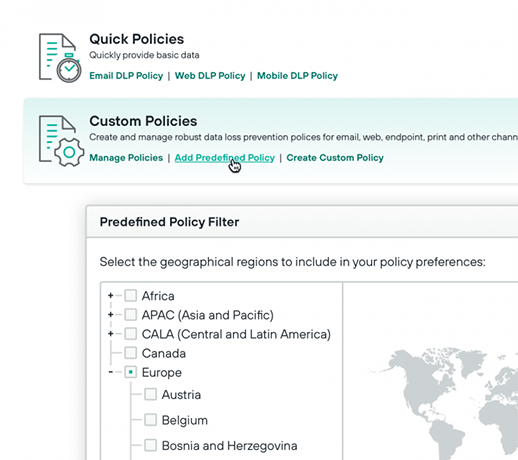
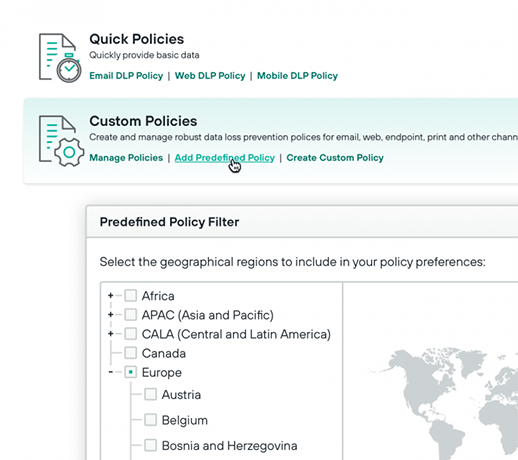
Eliminate multiple DLPs with one console. Configure and deploy policies from a single user interface across email, web, cloud and endpoint from the Forcepoint Data Security platform.
Easily deploy on major email providers such as Microsoft Exchange, Gmail for Business and others. Configure and publish policies in less than five minutes.
Deploy from and save emails on on-premises or the cloud, with no sensitive data storage in the cloud necessary. Take advantage of existing Microsoft encryption capabilities to better protect your data.
Forcepoint DLP for Email runs in the AWS cloud, providing 99.99 percent uptime with no scheduled downtime so your data stays secure at any time of day.
DLP Deployment:
In the Cloud or On-Premises
Deploy Forcepoint DLP in the cloud (SaaS) or on-premesis. With implementation support from the Forcepoint professional services team, your organization can see time-to-value in as few as six weeks!

IDC Marketscape: DLP Vendors 2025
Forcepoint was named a Leader in the IDC MarketScape: Worldwide DLP 2025 Vendor Assessment. Discover which criteria Forcepoint DLP excelled in by downloading the full report.
Analyst recommended.
User approved.
Forcepoint is consistently ranked among the top Data Loss Prevention software and data security software providers by users and industry analysts.
Forcepoint has been named a Leader in the IDC MarketScape: Worldwide DLP 2025 Vendor Assessment.
Forcepoint named the 2024 Global DLP Company of the Year for the second consecutive year by Frost & Sullivan.
Forcepoint recognized as a Strong Performer in The Forrester Wave™: Data Security Platforms, Q1 2025.
Frequently Asked Questions
What is Data Loss Prevention (DLP) for Email?
A DLP for Email helps organizations prevent sensitive data within email from being lost, leaked, misused or accessed by unauthorized individuals. It monitors outbound messages, and it searches for any content or attachments that may be sensitive, confidential, private or protected by regulation. When a message that contains sensitive data is found, email DLP systems may flag it, block it or delete it based on security policies.
Why is DLP for email important for organizations?
Since email is a predominant form of business communication, DLP for email is now considered an essential data security technology. DLP for email solutions are designed to help address the many potential causes of data leaks and loss, including cyberattacks, malicious insiders, security negligence and human error.
What are the key features of a DLP for email solution?
Some key features of Forcepoint DLP for Email are:
- Managing policies from one dashboard
- Effortlessly integrating with Microsoft and Gmail
- Maintaining data sovereignty and integrity
What are the benefits of a DLP for email solution?
With a DLP for email solution, such as Forcepoint DLP for Email, organizations can get control over data by extending policy coverage to outbound emails. More specifically, it provides agentless control over outbound emails and prevents exfiltration where it's needed most.
How does DLP for email work?
DLP for email works by inspecting messages and attachments to look for content that may represent a potential data threat. Techniques to identify sensitive information and then take action may include the following:
- Rule-based searches
- Exact matches
- Pre-built categories
- Flagging the situation
- Blocking the action
- Deleting the message
What types of email threats does DLP for email protect against?
Email messages and attachments may contain a variety of sensitive material, including Social Security numbers, credit card information, intellectual property, financial data and more. Given the importance of safeguarding sensitive information in emails, DLP for email helps protect data against threats such as the following:
- Inadvertent leaks
- Insider threats
- Cybercriminals
Can Forcepoint DLP for Email integrate with Microsoft and Gmail?
Absolutely. With Forcepoint DLP for Email, organizations can easily deploy on major email providers such as Microsoft Exchange, Gmail for Business and others.
What is a secure email gateway?
A secure email gateway helps protect your business from malicious content contained within emails by preventing them from reaching their intended recipient.
Why is a secure email gateway important for organizations?
Secure email gateways offer protection against malicious messages and attachments. By using robust email security solutions, organizations can dramatically reduce the number of successful and attempted attacks against their business.
How does a secure email gateway work?
A secure email gateway offers a robust framework of technologies that protect against email-borne threats. Most secure gateways offer a minimum of four security features: virus and malware blocking, spam filtering, content filtering and email archiving.

