A Buyer’s Guide to Behavior-based Cybersecurity
0 min read

We are strong advocates of behavior-based cybersecurity here at Forcepoint. We realize the significant advantages that adopting a risk-based approach focusing on behaviors of users and devices can bring as organizations embark on their digital transformation and data protection maturity journeys. We also realize that adopting a new paradigm in regard to security can be tricky to navigate not just from a terminology perspective, but from understanding the tremendous advantages of implementing those in reality.
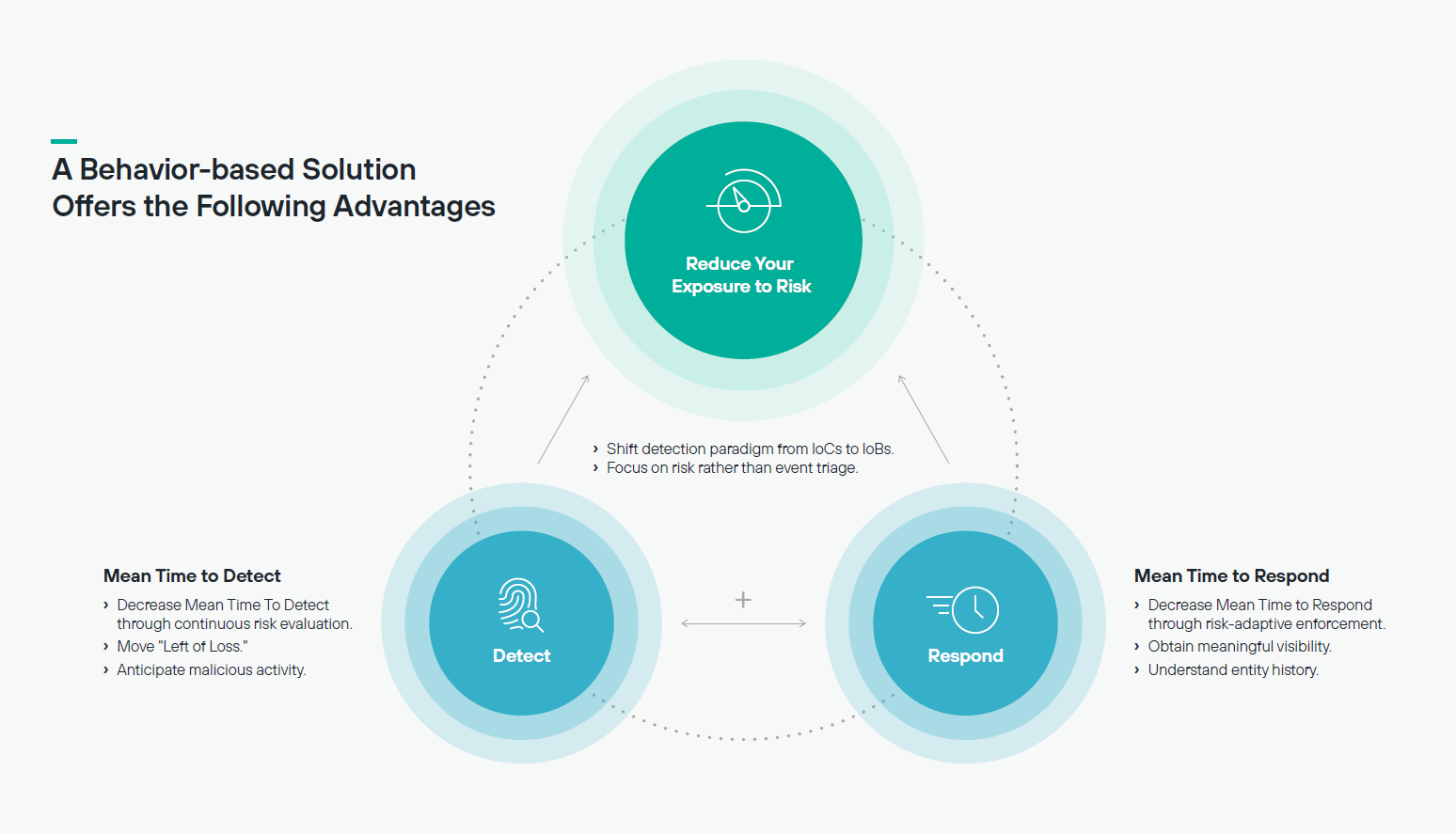
If the constant cat and mouse game played out between attackers and defenders keeps you up at night it seems right to pursue a different path. A behavior-based approach offers the opportunity to see actions in your environment through a risk lens; no more binary allow/deny but a considered approach appropriate to the context of the user’s actions. Through continuous evaluation of the risk presented by employees in your environment it is possible to drive down the Mean Time To Detect incidents. Expanding that into response, through an automated response based on risk, it is then possible to drive down Mean Time To Respond.
In short, a behavior-based solution offers the following advantages:
In our buyer’s guide to behavior-based cybersecurity we can help organizations navigate this journey towards a proactive risk-based approach. In the guide, we cover:
- A definition of behavior-based cybersecurity and how it is different to a threat-centric approach.
- We introduce Indicators of Behavior (IoBs) and why are they foundational for behavior-based cybersecurity.
- The benefits of behavior-based security and how to build a business case which includes optimizing your current security stack, and achieving greater efficiencies in your incident detection and response
- We list the top 5 capabilities that you should look for in a behavior-based security solution.
- Finally, we advise how to prepare your organization for a behavior-based approach.
We hope you find this guide useful. It is now available for download. Click the green Read the Whitepaper button to the right to do so.
- A Buyer's Guide to Behavior-Based Cybersecurity
In the Article
 A Buyer's Guide to Behavior-Based CybersecurityRead the Whitepaper
A Buyer's Guide to Behavior-Based CybersecurityRead the Whitepaper
X-Labs
Get insight, analysis & news straight to your inbox

To the Point
Cybersecurity
A Podcast covering latest trends and topics in the world of cybersecurity
Listen Now