Secure M365 and Copilot
Secure Collaboration. Streamline Compliance.
Enable AI Adoption.
Auto-Remediate Misconfigurations
Scan SharePoint and OneDrive for risky sharing and access misconfigurations
Classify files and apply Microsoft Purview sensitivity labels, triggering protections for critical data
Automatically remediate excessive user permissions with policy-driven controls
Safeguard Data in Copilot
Gain visibility and control sensitive data in Copilot prompts and responses
Enforce granular, context-driven access controls
Provide audit trails for Copilot interactions
Unchecked Microsoft 365 and Copilot usage turns
productivity into risk
Over 80 percent of data breaches involve data stored in the cloud,
making the largest cloud collaboration platform a potential data risk.
Overshared files and excessive permissions expose sensitive data
Uncontrolled Copilot access introduces new data leakage paths
Lack of context-aware data protection policies leads to data loss via risky users and devices
AI and malware expand the Microsoft 365 attack surface
Microsoft 365 and Copilot: Protect Data and Govern AI
Secure business-critical data and govern AI interactions with deep visibility, AI-powered classification and unified data controls.
Audit and remediate Microsoft 365 permissions
Analyze and remediate overshared permissions across OneDrive and SharePoint to reduce unintended data exposure to Copilot assistants or insider threats.
Secure data in Copilot
Gain visibility into Copilot prompts, responses and file access. Apply DLP controls to prevent sensitive data from being used in prompts and audit AI-generated responses.
Prevent data exfiltration via Microsoft 365 apps
Enforce consistent data protection across Microsoft 365 apps and Copilot to prevent sensitive data from being accessed, summarized or exfiltrated by users or AI-driven workflows.
Reduce the Malware Attack Surface
Continuously identify, classify and reduce exposure of sensitive data across Microsoft 365 to limit what malware and AI-driven attacks can access or exploit.
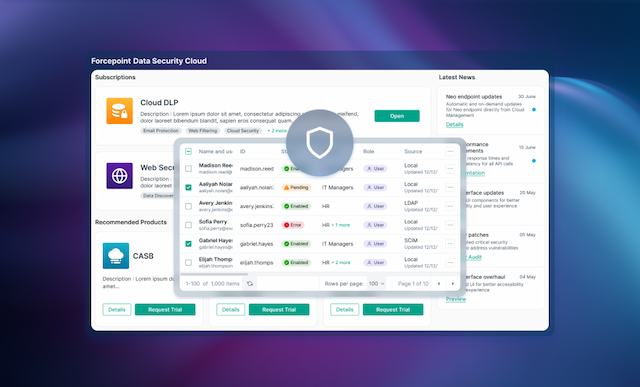
M365 and Copilot Security Solutions
Analyst recommended.
User approved.
Forcepoint data security solutions are consistently ranked among the top in the industry by analysts and customers alike.

Forcepoint has been named a Leader in the IDC MarketScape: Worldwide DLP 2025 Vendor Assessment.

Forcepoint named the 2024 Global DLP Company of the Year for the second consecutive year by Frost & Sullivan.
Forcepoint recognized as a Strong Performer in the Forrester Wave™: Data Security Platforms, Q1 2025.
Everything You Need to Know About
Securing Microsoft 365 and Copilot
WEBCAST
Forcepoint Data Security Cloud: A Full On-Demand Demo

BLOG
Top 5 Data Risks of Using Microsoft Copilot

WEBCAST
A CISO Guide to Securing Copilot and the Future of Work

BLOG
How to Secure Microsoft Copilot Data with Forcepoint’s Unified Security Platform



