
We Are the Hacker's Day Job with Adam Levin, Part 1
Share
Podcast
About This Episode
This week we welcome Adam Levin to the podcast to talk about the hacker’s day job. He is a long-time consumer affairs advocate with more than 40 years of experience. He’s the author of the book Swiped, and formerly Chairman and founder of CyberScout as well as co-founder of Credit.com. He joins us at the apex of the consumer security awareness time of year. Holiday shopping, COVID, flu, and other health concerns run rampant in addition to geopolitical security concerns that are ever-present.

He shares insights and stories from his more than 40 years on the consumer affairs advocacy front lines. This frames the security challenges each of us face in our daily lives. Many of which are seemingly innocuous yet can have disastrous consequences and upend livelihoods. Great best practices tips here for both security pros and non-industry folks. Shoring up defenses in places we’ve gotten very familiar in trusting – and they aren’t all that trustworthy after all.
Podcast
Popular Episodes

35 mins
The War on Data, Cyberspies and AI with Eric O'Neill - Part I
Episode 352
January 6, 2026

22 mins
How AI and Third-Party Risk Are Transforming Healthcare Cybersecurity with Ed Gaudet - Part I
Episode 339
October 1, 2025

24 mins
The Evolving Cyber Threat Landscape in Healthcare: Insights from Fortified Health Security’s Russell Teague - Part I
Episode 332
August 11, 2025

44 mins
From Battlefield to Boardroom: Ricoh Danielson’s Lessons on Cyber Warfare and Digital Forensics
Episode 327
May 27, 2025
Podcast
We Are the Hacker's Day Job with Adam Levin, Part 1
[00:34] Consumer Affairs Advocate and Cybersecurity Expert: Adam Levin
Rachael: So I am so excited for today's guest. I think I have been following him on Twitter for years. Not stalking, but just genuinely following. Every time he posts something new, I learn something, get insights, and that's wonderful, particularly on Twitter where it doesn't happen all the time. So please, please give a warm welcome to Adam Levin.
He is co-host of What the Hack podcast. And he co-founded Cyber Scout. He was a Co-Founder of Credit.com. And he is a renowned Consumer Affairs Advocate and nationally recognized expert on cybersecurity, privacy, identity theft, fraud, and personal finance. Super hot topics. He just brings decades of experience on the front lines to today's discussion. I can't wait to jump into it.
Adam: Thank you so much for allowing me to come in and lower your digital property values. I appreciate the invite.
Rachael: It's such a great time to be. Everything that you follow it's like the apex of the time to be following all of these topics. Would you say?
Adam: I would say that things are getting crazier and crazier between disinformation, breaches, hacks, leaks. We're in an interesting time where breaches have become the third certainty in life behind death and taxes. And so as a result, every day is a new adventure. Many of the adventures are painful, but they are definitely new adventures.
The Hacker’s Day Job: It’s All About Impulse
Rachael: That's fantastic. So this time of year, and I will say sidebar to that. I kind of just operate under the assumption that all of my personal information's on the dark web somewhere. I get those alerts. And I think about that this time of year too, when you're doing online shopping, which is all I do. And I was reading that article that you posted about holiday scams and don't click links and text alerts, particularly when, “Hey, track your package.”
And why did I not know that, Adam?
Adam: Well, I think you did know that. I just think it's one of those things where a lot of people know it.
They just can't help themselves because if it involves anything that they're waiting for, it's all about impulse.
And that's how these folks get you. But you have to also start with a couple premises. Number one, we all have day jobs. Whether you're running a podcast, you're raising a family, you're working for someone, you're running a business, you're still involved in educational pursuits, a philanthropic pursuit. That's our day job.
However, we're facing off on a daily basis with people where we are their day job - a hacker’s day job. So you have to keep that in mind. The second thing you have to keep in mind, and so many people just still have trouble grokking this. When you look in the mirror, you see you. Some people have a very flamboyant version of what they see when they look in the mirror. But they see themselves, and they go, “I'm just a regular person. Who would want to hack me?”
The Hacker’s Day Job: Who Would Want My Information?
Adam: I mean, who would want my information? Of course, I once worked with a guy who said, "Golly, the person who stole my identity has built better credit than I had, I'll stick with him." But you see you. But to a hacker or scammer and identity thief, they're looking at Jay-Z, Beyonce, Adam Levine, because we all have what they want.
We have financial information, we have personal information that can be used for identity theft purposes, or it may have absolutely nothing to do with us. And we just may be the tributary to a larger river, which means are they trying to get to a spouse, a child, a sibling, where we work, where we're affiliated, political pursuits that we may be involved in? We could be unwittingly the way into a campaign. And so that's really the big picture. And then you add to it the fact that at this moment we are in the middle of a perfect storm.
Politically, we just came through a very shocking election for certain people, a very satisfying election for others. We still have a runoff going on in the State of Georgia, so there's going to be a lot of people interested in that. We have disinformation campaigns running wild in this country. You also have health concerns, whether it's Covid or RSV or Monkeypox, that will capture people's imagination.
In addition to which currently the student debt forgiveness program, there's millions of people that are involved in that.
The Hacker’s Day Job: A Pantheon of “Ishings”
Adam: You have the war in the Ukraine, which is of great concern and interest to many, many people. And then you have the holiday season which is where this is party time for scammers. It's El Dorado, and they're going to be out there and they're going to be trying every which way to get you to open an attachment, click on a link, respond to what I call the pantheon of ishings, the general phishing email, which is Dear cardholder, Dear member, Dear Amazon shopper, Dear UPS customer, there's spear phishing, which would be Dear Rachael, Dear Petko.
There would be vishing, which is when it's voiceover internet protocol phishing, which is when you get a phone call from someone representing themselves to be a government agency, a health department, someone you might work for. Had a great deep fake story about that, or a financial institution. A lot of people are expecting calls from their banks going, “Did you really charge this?” So you have that coming.
And then you have smishing, SMS text-based phishing where you get a text like you had mentioned, and it relates to something that you're expecting or that you just did. And the first impulse, the magic word is impulse, is you're going to click.
Rachael: We love to click as humans, we're clickers for sure.
[06:39] Always Go to the Source
Adam: Well, what I try to say to people is, “If you don't want remorse, go to the source.” Which means you don't click on the link, you don't open the attachment, you go directly to the retailer, the charity, the government agency, and communicate with them directly after you've independently determined how to get there or how to call. And the number one rule of everything is if you're contacted by anyone for any reason whatsoever and they ask you to authenticate yourself, hang up.
It's different if you call them, you know where you're calling and they ask you to authenticate yourself because they're trying to protect you as opposed to making you the gift that keeps on giving.
Rachael: Right. It reminds me of a story I read this morning about this woman. She recently graduated college, and remote work is a thing now and she doesn't have a car. And so she interviewed for a job that seemed legitimate. She checked the Better Business Bureau, she checked LinkedIn, she checked all these things and they sent her a check to buy office supplies, but then asked her to take that money and send it in crypto or through this other thing. And then turns out it was a complete scam and she ended up $5,000 in debt, recently graduated. Doesn't have that kind of money.
It's scary. Not that I would ever myself, you're asking me to send you money in crypto for a new job. That sounds weird to me. But if you're young and naive and don't know, that could be a very real thing because you just literally don't know if that's how business works today.
[08:21] Hacker’s Day Job Is Taking Not Giving
Adam: No, it's a bummer. I was going to ask you if you'd like to send me some crypto as a token of our experience today.
Rachael: Sure. I have some FTX tokens I think that I can send you. Just kidding.
Adam: There you go. Yes, they're really working right now. But we had a woman on our podcast just the other day who was an investigative reporter in Nashville talking about her mom who received a letter. Now this is already now snail mail.
Supposedly from Best Buy Geek Squad saying that you've renewed your anti-malware subscription with us but you've overpaid. And her first reaction was, I never pay for three years of anything.
So therefore, what's wrong with this picture? So she calls the number because she wants to clarify and get her money back. And she first speaks with a woman and she's made to believe that this happened and they would like to get her money back to her. So the first thing they'd like is her banking information so they can get it back to her.
And then a guy got on the phone and he started talking to her about gift cards. Not that they were going to put money on gift cards for her.
They wanted her to go out and buy gift cards for them, which they catch you at a moment where you're so befuddled that you don't realize that instead of giving, they're taking.
Hacker’s Day Job Needs to Be Sophisticated, Creative, and Persistent
Adam: And she went down to CVS, she was asked to buy $2,000 worth of gift cards. They did say to her, when you go into CVS, do not bring your phone in with you. Because obviously if you're talking to someone on the phone who looks like they're instructing you to buy gift cards, the cashier gets a little suspicious. So she walked in and the cashier noticed, this is a woman in her '80's and she's buying gift cards for Target at a CVS. It's like, there's something strange about this picture. So she would only sell her two $500 cards as opposed to four. And you say to yourself, if you're suspicious, why would you sell her any?
So then they told her, no, well now you can only get two of them, so why don't you get the other two at Target? And as she's driving over there, it suddenly dawned on her, wait a minute, I'm giving these guys my money as opposed to getting money from them.
But again, this is the kind of stuff they do, and many of them are sophisticated, creative, and persistent. And oftentimes you'll see that if someone is caught up in a scam and they suddenly go, wait a minute, you're scamming me, I'm out of here, you hang up, there'll be 15 calls in a row coming at you because they're trying to get you back on the phone.
When You Thought It Was Right
Petko: I was going to say that, that kind of reminds me of once I had a family member call a phone number that says, your computer's been hacked, call this number and we'll clean it up for you. And they called the number and next thing you know, he or she is giving away a little more credit card data, personal information. And I ended up hearing about it and I called them and said, "Get off the phone, just hang up. Don't even continue the conversation."
But you're right, people are vulnerable because you think everyone's trusting. Go to Google, you go to Gmail, you trust that and somehow that one email or that one popup that just did a drive-by, if you will, and you assume it came from that provider just like UPS or the click you clicked on. You trust your phone, you trust that it says UPS, you trust it, or it says Amazon.
Rachael: Because it looks right.
Petko: These are entities you trust.
Rachael: Yes, on first glance it looks right.
Adam: No, and they're so good at spoofing phone numbers or logo. In the old days the grammar was off, the spelling was off, the colors were off, the logo didn't look right. Today, and this is because of phishing as a service, they do look right. And as a result people are compelled somewhat, to respond.
Now They Got You
Adam: There's also the great scam where you get a phone call from your bank and they will say, "This is your credit card number, yes?" And you go, "It is," because it is your credit card number. And they go, "Now this is your expiration date, right?" You go, "Yes, it is, it is." Well just to prove you're you because we need to make sure we're talking to you, just flip over your card and give us the security number. Of course the answer you give should be, "Well you know what my security number is, you're calling me."
But then the scam goes on after you give them the number. So now they have your credit or debit card, then they say, "You know what? It looks like you really are a victim of some kind of account takeover. And we're worried with all the information out there with the Equifax breach and everything else that you could be a sitting duck.
So we're going to help you with the credit reporting agencies, put a fraud alert on your file or freeze your credit. So in order to do that, we need your social security number. If you don't mind, give it to us and then we'll make the call with you." So you give them your social security number and then they get off the phone and you're going, "What? Hey, where'd you go? What's going on?"
Well, now they got you.
[13:41] Phishing as a Service
Petko: Adam, you mentioned phishing as a service. I mean I always think of all the Cloud services we have. We have Email as a service. Can you describe what's phishing as a service?
Adam: Well, phishing as a service and ransomware as a service are like kissing cousins. And what phishing as a service is is that very sophisticated people will create a program and tools to help people who are far less sophisticated use this software and/or malware and tools in order to go out there and launch these attacks against either a
specific target or a blanket target, which just mean they're going after everybody.
And what happens is it's available for sale on the dark web and they develop this. They will sell this to you for a reasonable price. All they ask in return is they get a piece of the action. So it gives them an opportunity to spread their wings and get a lot of other people involved. The only issue with it and in particular in ransomware is when you have a lot of people that have no idea what they're doing.
All they did is they bought something and watched an instructional course. They may freeze your files for instance. But when it comes time to give you the decryption key, they give you something but it doesn't work. But what it's really done is to democratize hacking and phishing, and at the same time lower the bar so that people who are far less competent in doing this.
I mean let's face it, if I'm going to be attacked by somebody, I'd much rather it be somebody that knew what they were doing, especially if it involved me getting something back.
The Perfect Storm
Rachael: Don't they have Wine of the Month Club, but you can subscribe to Phishing of the Month Club or things like that? I mean, it's fascinating just what a network they've created, what a business. I mean it's actually this great, really well-funded business that they've created.
Adam: Definitely. It's a business model. The only question is do you want Chardonnay, Cabernet, Grenache.
Petko: Going back to your perfect storm. I can imagine this is not just marketizing, but it's creating a lot of independence out there that are just creating a lot of noise. And I'm surprised that, I mean, we're not doing more as a community to kind of prevent some of this. I mean we talked about SMS phishing that goes in your phone, or we're talking about some of the email. What can we do as an industry or what can individuals do to limit the attack surface if you'll that they can be protected?
Adam: Well, and you nailed it, right, is how do you reduce your attackable surface? Especially in a world where you have billions, and that's Dr. Evil pinky to the lips, B, billions of internet of things, devices that are tracking you, eavesdropping, listening, and at the same time have a life.
But this is also the interplay of convenience versus security. And people always take convenience and they're willing to live in a surveillance economy in order to get that convenience.
The Three M’s Framework
Adam: So when I wrote the book, Swiped, with my co-host on What the Hack, Beau Friedlander, we created a framework, we call it the three M's. How do you minimize your risk of exposure, reduce your attackable surface? How did you monitor so you know as quickly as possible that you're having an issue? Then how do you manage the damage? And let's look at the first M briefly.
That first thing is password protocol. Either get a password manager, have long and strong passwords, do not share passwords across your universe of websites. Why a lot of companies and individuals have issues is that people tend to use their passwords from their private lives in their business life.
They also tend to use the same passwords, which means if they're breached somewhere, effectively they're breached everywhere. And if you look at the constants, if they have your email address, then probably they have one-half of your login credentials, because most people either are driven to use their email address as their user ID or they just do it because it's just easier or it auto-fills.
And then the second issue, when you create the password for it, is it a dumb password? Is it an easy password? Even if it's an indecipherable password, if it's been discovered as part of a breach, then it's out there. There will be brute force attacks where they will try to use every password they can think of involving you or what the AI in their program actually throws out there. And you know you're under attack.
Double Your Security from Hacker's Day Job
Adam: So number one, long and strong passwords. Number two, two-factor authentication. Not completely the silver bullet, because people have found a way to get in there and get around two-factor authentication. In particular, they steal cell numbers because they call mobile providers, convince them that they are the victim and they ask them to allow them to transfer the phone number to a new device.
You also have the whole issue of clicking on links, opening attachments. In the old days it used to be trust but verify. Today it's never trust, always question, always verify.
Even if it comes from someone you know, they could have been defrauded and they don't know it. It may have come through social media and it was a cute cat picture. There's a great story of someone I knew who was a great hacker in Europe and he knew that someone in his neighborhood was married to the CFO of a major oil company and she loved cat pictures.
So he basically sent her a malware laden cat picture. And then when she clicked on the link, used that to invade her home network and ultimately get into the computer of her husband and get the financials of that particular oil company. And then he did his version of a public service. He called a fellow and said, "So now I'm going to tell you what I have and now I'm going to tell you what you need to do to make sure I don't have it anymore." I'm your neighbor.
Be a Superhero
Adam: So also people have a tendency to download apps that look like the newest, coolest thing. They click on permissions that they have no idea how much information they're allowing someone to get, or these apps are pure scams. Also, when they set up answers to security questions, they tend to use answers that are fact-based. And those facts are either they've posted them on social media or someone else posted them on social media.
So rule of thumb, lie like a superhero. Batman, Superman, they're not going around telling people who they are.
So when you're answering these questions, if they ask you what high school you went to and you went to Ridgefield High, say you went to Sky High. If your mother's maiden name is Smith, say it's Brown. The important thing is that you not be so creative that you end up locking yourself out of the accounts.
But you have to remember, there's so much information out there. Then freeze your credit score. It's now free all over the country. You can do it in many states. You can freeze your kids' credit score. So that's something that you should be considering as well. That's the first M. Second M shorter. How do you monitor? Well, get a copy of your credit report and actually read it.
Monitor Your Actions
Adam: Pay attention to what you didn't do as opposed to what you know you did.
Monitor your credit scores. If they take a sudden precipitous drop, it's an indication you either didn't pay a bill on time, you use too much of your available credit, or your victim of identity theft. Sign up for transaction alerts with your retailers that notify you anytime there's activity in your account. Because if you're a victim during the holiday season of what's called E-skimming, where a malicious code is put on legitimate websites that there's no way that a consumer can determine whether or not there is such a thing.
The way you know is if you start getting notices from your financial institutions telling you you did things that you know didn't do. Also, and this is, most people go, "I never thought of that." When you get an explanation, a benefit statement from your health insurer, read it.
We had a woman who was 72-year-old grandmother and her insurance companies were billed on the same day, opposite sides of the country by two laboratories.
One for a sperm viability test, the other for a pregnancy test. Now she knew it wasn't her and she immediately notified the insurance companies and she had to actually fight with them to get them to pay attention.
Also, think about more sophisticated forms of credit monitoring, which are available from the credit reporting agencies, many third-party resellers, Credit.com, Credit Karma, Credit Sesame, Quizzle, the list goes on and on and on. So that's the monitoring aspect because you need to know as soon as possible.
Get Professional Help to Combat Hacker's Day Job
Adam: And then of course the very critical part is have a damage control program. And one of the easiest ways to do that as opposed to trying to do it yourself and ending up being severely psychologically overwhelmed and putting your job in jeopardy because you were so obsessed about solving the problem, is that many insurance companies, a portion of financial services companies, more credit unions than banks.
Because they're more consumer-centric, or now HR departments where you work offer programs to help through identity incidents with professionals that will make all the phone calls, write all the letters, do what’s not like the old days where you'd get a tip sheet and the best of luck, so it's one of those things where these programs are available.
In some cases they are free as a perk of your relationship. And in some cases they are deeply discounted. Then, in other cases, you got to pay full freight. It's just part of your employee benefit program, either employer-paid or voluntary benefit. And it's out there to help you.
And I got to tell you, when you face off against some bad guys and you're dealing with something way above account takeover where they're opening new accounts, they are committing child identity theft, they're committing criminal identity theft where the trail of breadcrumbs leads back to the victim.
Or they are involved in other forms like medical identity theft where your information is used in order to get medical treatment, and somehow your information gets co-mingled with their information in your medical files. Now we're talking about something way beyond finance. We're talking about health-related compromises.
Swiped: How to Protect Yourself from Hacker's Day Job
Petko: So Adam, all this is in your book, right?
Adam: It is.
Petko: So where can they get your book? 'Cause I will tell you while we were talking, I went ahead and ordered the book. I couldn't help it.
Adam: You can get the book at Amazon or wherever you buy books. Generally it's easier to get it to buy it online, but it's available and it's called Swiped: How to Protect Yourself in a World Full of Scammers, Phishers, and Identity Thieves.
And the whole point is to make people more aware of the red flags, the threats, the opportunities for the bad guys out there. One of my favorite stories in the book is there's a young guy, he's about 16 years old, he's working in Target. His name is Alex. And one day a young woman walked by and then suddenly backed up and went, "Wow, he's kind of cute."
So she took a picture, she sent it to a friend of hers in England, and all of a sudden it went viral and Alex had no idea.
Rachael: And we're going to pause it right there for today's discussion and come back next week with a part two discussion with Adam Levin. So yes, we're leaving you with a cliffhanger this week folks, and you definitely don't want to miss next week where we talk more about if you don't want remorse, go to the source. To all our listeners out there, thanks again for joining us.
Don't forget to subscribe. You just have to smash that subscription button and you get a fresh episode every Tuesday in your email inbox or to your podcast platform of choice. So until next time everybody, be safe.
About Our Guest
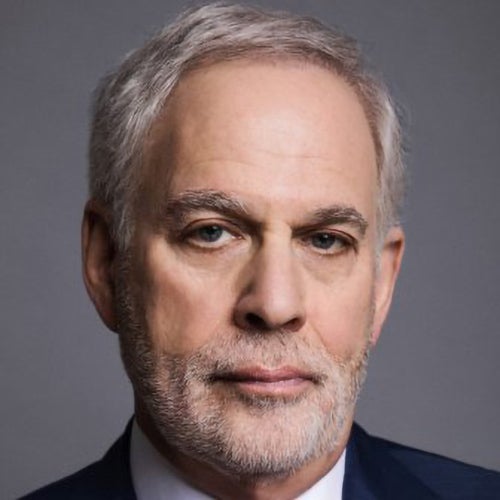
Adam K. Levin is a consumer affairs advocate and serial entrepreneur with more than 40 years of experience. He is a nationally recognized expert on cybersecurity, privacy, identity theft, fraud, and personal finance. At age 27, Levin became the youngest Director in the history of the New Jersey Division of Consumer Affairs — one of the most powerful consumer protection agencies in the U.S. He is a graduate of Stanford University and the University of Michigan School of Law.
As Chairman and founder of CyberScout, Levin built a premier global identity, data protection company, and helped pioneer the cyber insurance business. The organization was acquired in March 2021 by Sontiq, which was soon after acquired by Transunion. Levin was also co-founder of Credit.com, one of the first credit education, information and products and services companies on the Internet focused on consumer credit building. The company was acquired in 2015 by Progrexion.
Listen and subscribe on your favorite platform