Insider Risk Protection
Real-Time Risk Detection. Instant
Policy Enforcement. Stop Breaches.
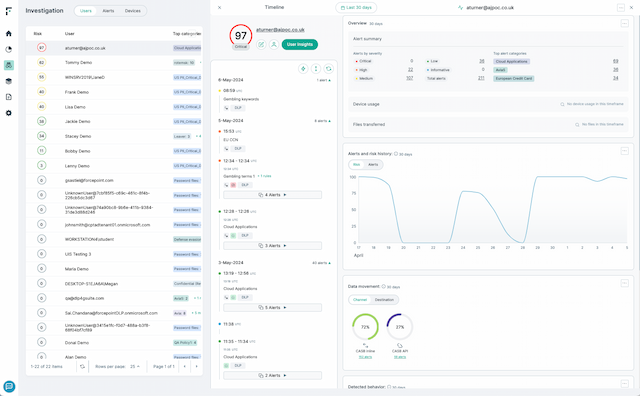
Monitor User Behavior
Gain context on user actions across apps and channels
Monitor and detect anomalies for each individual user with 150+ Indicators of Behavior
Continuously monitor user risk in real time
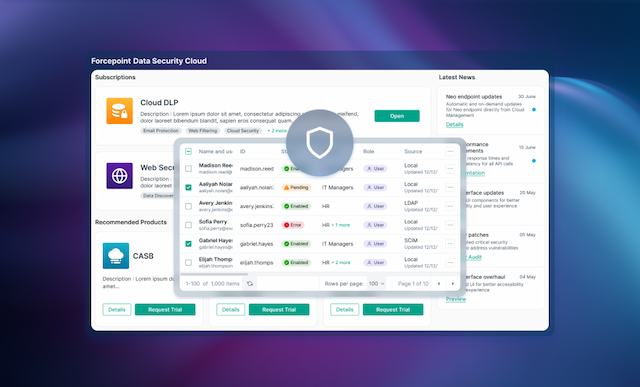
Automatically Adapt Controls
Dynamically adjust DLP policies based on user risk level
Block or limit sensitive actions when risk spikes
Avoid over-blocking trusted users to let them work freely
Static Rules Can’t Stop Insider Threats
Traditional DLP tools treat every violation the same, missing context around user intent and creating alert fatigue.
Security teams need a smarter, risk-aware approach that changes with user behavior.
Lack of visibility into user intent
Too many false-positives and alerts
One-size-fits-all controls hinder safe and productive users
Insider threats fly under the radar until it's too late
Turn Insight into Action with Automation
Forcepoint Risk-Adaptive Protection analyzes behavior, calculates user risk and automatically adjusts policy controls,
allowing you to stop threats without slowing your business down.
Track and score user risk in real time
Continuously monitor user behavior and update dynamic risk scores based on anomalies, policy violations or contextual signals like time of day, file locations or data volume.
Dynamically adjust DLP enforcement
Policies adapt automatically based on risk. For high-risk users, actions like file uploads or downloads may be blocked or restricted. Low-risk users stay productive by only logging their actions.
Reduce false positives and alert fatigue
By focusing alerts and policy actions on high-risk behavior, analysts prioritize true threats and avoid chasing noise.
Enhance insider threat investigations with context
Gain visibility into why actions were taken. RAP surfaces behavioral context and policy triggers to speed investigation and support legal or compliance reviews.
Analyst recommended.
User approved.
Forcepoint data security solutions are consistently ranked among the top in the industry by analysts and customers alike.

Forcepoint has been named a Leader in the IDC MarketScape: Worldwide DLP 2025 Vendor Assessment.

Forcepoint named the 2024 Global DLP Company of the Year for the second consecutive year by Frost & Sullivan.
Forcepoint recognized as a Strong Performer in the Forrester Wave™: Data Security Platforms, Q1 2025.
Everything You Need to Know
About Data Security
WEBCAST
Forcepoint Data Security Cloud: A Full On-Demand Demo
EBOOK
Managing Insider Risk: A Practical Guide for Modern Organizations

VIDEO
A Day in the Life of Sensitive Data

WEBCAST
See Everything, Secure Everything: Managing Insider Risk


