Forrester Zero Trust Edge (ZTE) Unifies SASE Architecture with Zero Trust Principles
0 Minuten Lesezeit
Part of our ongoing series about Zero Trust.
On January 28, 2021, Forrester published a report by David Holmes and Andre Kindness that we think will likely become one of the seminal reports on Zero Trust: Introducing the Zero Trust Edge Model for Security and Network Services: A Secure Access Services Edge (SASE) Is A Zero Trust Edge (ZTE). This is an important milestone for both the network and security industries: two of the most influential technology analyst firms are in alignment about the need to change how businesses and government agencies should enable people to work.
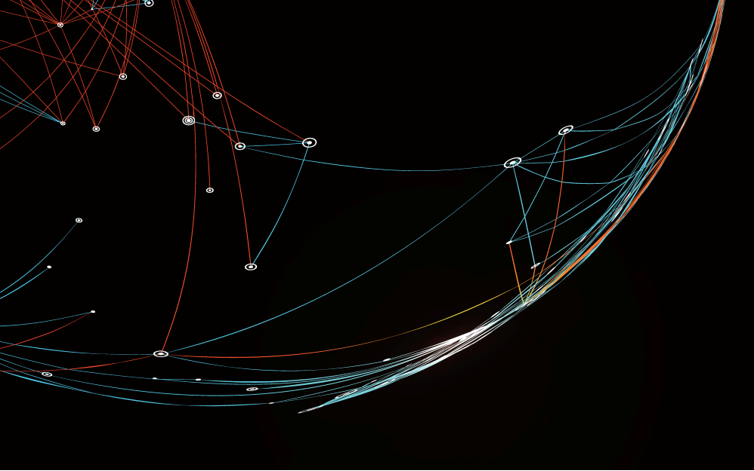
In this report, Forrester describes how “a Zero Trust edge solution securely connects and transports traffic, using Zero Trust access principles, in and out of remote sites leveraging mostly cloud-based security and networking services.” This concept of bringing security and networking together—convergence—is at the core of both ZTE and SASE.
It does away with stacks of fragmented hardware products that often have been spread throughout enterprises, replacing them with integrated cloud services that provide consistent networking and security policies for all users, no matter where they’re working—at home, in the office, or on the road.
Convergence: Security + Networking
Holmes and Kindness herald such convergence, stating “Security and Networking finally combine against a common enemy.” In fact, multiple enemies:
- Increasingly sophisticated attackers – Thieves have become much more aggressive, using the pandemic to target people who aren’t used to working remotely and may not also follow best security practices.
- Performance – With applications and data now everywhere—across the cloud, through the web, and into legacy data centers—the old one-size-fits-all approach of having all users connect through a central hub gets overloaded, slows down apps, and kills user productivity.
- Complexity and cost – Adding appliances for every new threat, challenge or capability is no longer feasible; instead, organizations are finding that software-as-a-service solutions can be operated more consistently by smaller teams without requiring siloes of knowledge.
- Compliance – As data moves around, the risk of breaches grows. Having uniform visibility and control no matter where people are working or where data resides is now a must-have.
In short, ZTE and SASE are both about enabling people to better work anywhere while they and their data stay safe everywhere.
Securing Remote Workers seen as the first step towards ZTE
As we’ve written about recently, the pandemic has shifted most organizations’ priorities. Fortunately, many applications and data were already in the process of moving from internal data centers to the cloud. This laid the foundation for the exodus that Holmes and Kindness colorfully describe as having “pushed employees outside the controls of a corporate LAN moat” and illustrates one of the first ways that ZTE is being used:
- Securing remote workers – Even when vaccines for COVID-19 become commonplace, people aren’t going to be rushing back into the office. Delivering security from the cloud enables the same policies for protecting web, cloud, private apps and general internet traffic to be enforced consistently no matter where people are connected.
- Prioritizing business application traffic at branch WANs – Organizations have been replacing expensive, private links like MPLS with faster internet broadband connections. This direct-to-cloud approach boosts performance and cuts costs but requires networking capabilities such as SD-WAN to manage the flow of traffic over the right links and ensure that the right security controls are applied. As Holmes and Kindness note, “some vendors, like Forcepoint, support SD-WAN functionality integrated with multiple security services” in their ZTE solutions.
- Securing the internet of things (IoT) – ZTE provides a straightforward way to address the proliferation of devices that will not allow 3rd party software (such as security agents) to be installed on them. Putting simple ZTE connectors into the network that route traffic from sites with IoT devices to the appropriate cloud service or enforce policies locally (delegated from that cloud service) will give organizations uniform visibility and control that otherwise would require a separate set of products.
We’ve heard the same from many CIOs and CISOs. Giving remote workers, partners, and suppliers access to crucial resources such as internal line-of-business apps without complexities of VPNs is one of their first priorities. Then, over time they plan to implement a ZTE-style architecture for enforcing the same types of security at different types of sites.
Forcepoint extends Zero Trust Edge to continuously control the usage of data
Forcepoint has long been a proponent of Zero Trust; we build its principles into many of our products. As Holmes and Kindness note, SASE solutions (such as our Data-centric SASE) are ZTE solutions. We see ZTE as a foundation for delivering Zero Trust-as-a-Service that goes beyond just securing access. That’s why our Zero Trust solutions also also provide continuous control over how sensitive data sensitive data is used.
In dem Artikel
X-Labs
Get insight, analysis & news straight to your inbox

Auf den Punkt
Cybersicherheit
Ein Podcast, der die neuesten Trends und Themen in der Welt der Cybersicherheit behandelt
Jetzt anhören